VMware VSphere 5
hi there experts i'm new on vmwar
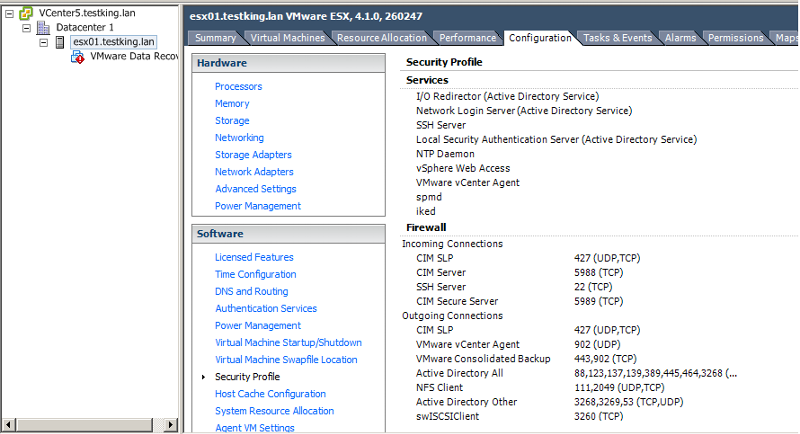
i have installed the the vmware data recovery plugins on the cventer but when open
the vsphere client to deploy the ovf template there is no vmware data recovery on inventary
thnx
vcenter.png
i have installed the the vmware data recovery plugins on the cventer but when open
the vsphere client to deploy the ovf template there is no vmware data recovery on inventary
thnx
vcenter.png
Click Hosts and Clusters or VMs and Templates.
ASKER
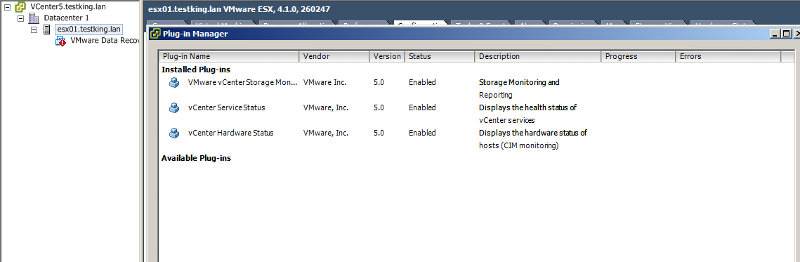
i found it on Hosts and Clusters andVMs and Templates but when i click on manage plugins i didin't found the plug ins for data recovery
that's because you need to install the VMware Data Recovery plugin.
Procedure
1 Run the plug-in installer VMwareDataRecoveryPlugin.m
2 Follow the prompts of the installation wizard.
3 Start the vSphere Client, and log in to a vCenter Server.
4 Select Plugins > Manage Plugins and make sure that the Data Recovery plug-in is enabled.
Procedure
1 Run the plug-in installer VMwareDataRecoveryPlugin.m
2 Follow the prompts of the installation wizard.
3 Start the vSphere Client, and log in to a vCenter Server.
4 Select Plugins > Manage Plugins and make sure that the Data Recovery plug-in is enabled.
ASKER
i have already installed the plug ins on vcenter server
ASKER
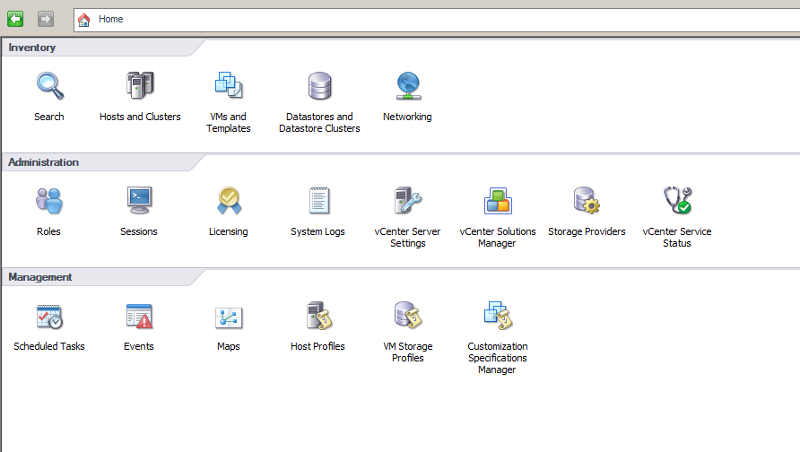
i have good configured my vcb but i can't plan a backup there is no icon on home
vcb.png
vcb.png
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
thnx hanccocka i have installed the plugins on vsphere client and it works