Outlook Certificate Error!
Okay so here's our situation. We have our mail server (Server1) and we have our corporate mail server (server2) We were recently merged by our corporate headquarters so we have decommissioned our (server1) mail services. We will use it for active directory etc, but the mail services is decommissioned.
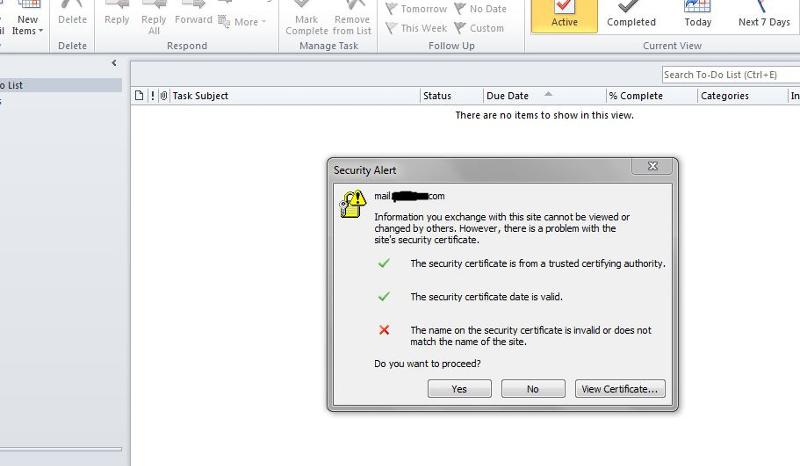
Today however the certificate expired, since I don't know much about it, I simply ran the fix my network SBS 2011 network tool. Now every time someone opens outlook they get this message:
This is odd because outlook is not even pointing at that server anymore.
How do I fix this certificate on my SBS 2011 machine so it doesn't pop up anymore for the users? Heck I don't care if it requires turning off the mail role even. We just need it gone! Because as soon as you hit Yes or continue, it keeps popping back up for the users and it's very annoying.
Today however the certificate expired, since I don't know much about it, I simply ran the fix my network SBS 2011 network tool. Now every time someone opens outlook they get this message:
This is odd because outlook is not even pointing at that server anymore.
How do I fix this certificate on my SBS 2011 machine so it doesn't pop up anymore for the users? Heck I don't care if it requires turning off the mail role even. We just need it gone! Because as soon as you hit Yes or continue, it keeps popping back up for the users and it's very annoying.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER