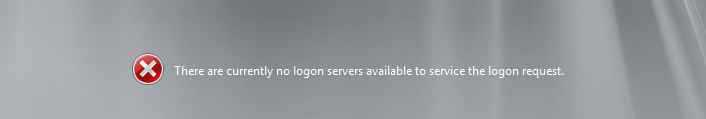
There are currently no logon servers available to service the logon request
ASKER
Hi Sommerblink,
Thanks for the quick respond. I have waited more than 1hr and tried, but the outcome is the same.. i also suspect some kind of service or services not starting, but i don't know how to check services without loging in to the domain controller?
Any Ideas?
Thanks,
Indika from Melbourne
Thanks for the quick respond. I have waited more than 1hr and tried, but the outcome is the same.. i also suspect some kind of service or services not starting, but i don't know how to check services without loging in to the domain controller?
Any Ideas?
Thanks,
Indika from Melbourne
Can you RDP to the server from a station and logon? If not, and if nothing else works, hold down the power button to force the system to shut down and bring it up again. If still nothing, do F8 on the next go and try safe mode... maybe some new driver/update is preventing all the services from starting. All else fails... how are your backups?
Maybe someone has a better idea, but the problem that you have is that your domain controller can't find itself.
In a normal network (read: non-SBS) it is almost always the case that there are more than one domain controllers on the network. With SBS, since it is all wizard-based, rarely is this practice preached, although it is perfectly acceptable to do and preferred.
So, since you have physical access to the server, I want you to get a thumb drive. Boot the server and mash the F8 key down until you get to the boot option screen. Choose Repair Your Computer or Recovery Console (or whatever it is called, should be top option). Once loaded, start Command Prompt. Go to C:\Windows\System32\winevt
Now, I don't have a SBS server to try this on (this was all a 2008 R2 DC), but do you have Safe Mode with Networking? If so, what happens when you boot the server with that? Were you able to login? If so, I want to double-check that your DNS settings are correct. The first and only DNS entry should be 127.0.0.1, unless of course you do have a second domain controller on your network on your Local Area Connection network card. Do you have other network cards listed here?
Zip up those event logs and post them here, or if you're good with event logs, you can open those up on another computer as well. The ones that I'm interested in are System.evtx and Application.evtx.
In a normal network (read: non-SBS) it is almost always the case that there are more than one domain controllers on the network. With SBS, since it is all wizard-based, rarely is this practice preached, although it is perfectly acceptable to do and preferred.
So, since you have physical access to the server, I want you to get a thumb drive. Boot the server and mash the F8 key down until you get to the boot option screen. Choose Repair Your Computer or Recovery Console (or whatever it is called, should be top option). Once loaded, start Command Prompt. Go to C:\Windows\System32\winevt
Now, I don't have a SBS server to try this on (this was all a 2008 R2 DC), but do you have Safe Mode with Networking? If so, what happens when you boot the server with that? Were you able to login? If so, I want to double-check that your DNS settings are correct. The first and only DNS entry should be 127.0.0.1, unless of course you do have a second domain controller on your network on your Local Area Connection network card. Do you have other network cards listed here?
Zip up those event logs and post them here, or if you're good with event logs, you can open those up on another computer as well. The ones that I'm interested in are System.evtx and Application.evtx.
ASKER
Hi Sommerblink and fl_flyfishing,
I think found the issue, before i restarted the server, i have installed some updates. now for some reason, the server is going to "Safe Mode" by default, doesn't matter what i select from F8 Menu, it alsway goes to "Safe Mode". i found extra line on "Windows boot loader editor" which some forums ask to remove, but when i try to do it, it comes up error. anyway i know "Safeboot Minimal" line is the issue. i will update you if i manage to delete that line through "bcdedit"
4.SBS-Enlite-Solutions-no-logon-.png
I think found the issue, before i restarted the server, i have installed some updates. now for some reason, the server is going to "Safe Mode" by default, doesn't matter what i select from F8 Menu, it alsway goes to "Safe Mode". i found extra line on "Windows boot loader editor" which some forums ask to remove, but when i try to do it, it comes up error. anyway i know "Safeboot Minimal" line is the issue. i will update you if i manage to delete that line through "bcdedit"
4.SBS-Enlite-Solutions-no-logon-.png
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
yes my Bad.. sorry for the confusion.. anyway i think can fix the issue from now... Thanks for your time and help..
Even though you are logging onto your domain controller, the domain controller doesn't know that until all the prerequisite services are also running. The main service is DNS.
If you've waited the full 15 minutes, then we might have other problems. If it started working, then the problem is that you are simply logging in too quickly and you have to allow the server to get everything running first.