Public Module
In the last part of my question Here mbizup suggests
" If there is a sub or function that I need to use across multiple forms, I generally will place it in a separate public module. You can pass form and/or control names to public functions as needed. "
My question...
Is there an example somewhere of passing Form and control names through or to a public function?
" If there is a sub or function that I need to use across multiple forms, I generally will place it in a separate public module. You can pass form and/or control names to public functions as needed. "
My question...
Is there an example somewhere of passing Form and control names through or to a public function?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Ok folks,
Gonna take a look at these later this morning and get back to you with points
Gonna take a look at these later this morning and get back to you with points
Just one other point, doing your routines like this:
Public Sub DoStuff(strFormName as String, strControlName as String)
Forms(strFormName).Requery
Forms(strFormName).control
End Sub
is a tad slower rather then addressing it as an object because your forcing Access to lookup the object in the forms collection each time you reference it rather then giving it a direct pointer.
However it's a lot easier to use that way. For example, you can easily call it from the debug window simply by typing:
Call DoStuff("JimsForm","FirstC
and hitting return. You can't do that always when it's defined as an object:
Public Sub DoStuff(frm as Form, ctl as Control)
I actually use both approaches making sure I use the latter for the critical stuff to ge the best performance and the first for procedures I might want to call on the fly as I test and debug.
Jim.
Public Sub DoStuff(strFormName as String, strControlName as String)
Forms(strFormName).Requery
Forms(strFormName).control
End Sub
is a tad slower rather then addressing it as an object because your forcing Access to lookup the object in the forms collection each time you reference it rather then giving it a direct pointer.
However it's a lot easier to use that way. For example, you can easily call it from the debug window simply by typing:
Call DoStuff("JimsForm","FirstC
and hitting return. You can't do that always when it's defined as an object:
Public Sub DoStuff(frm as Form, ctl as Control)
I actually use both approaches making sure I use the latter for the critical stuff to ge the best performance and the first for procedures I might want to call on the fly as I test and debug.
Jim.
<< is a tad slower rather then addressing it as an object because your forcing Access to lookup the object in the forms collection each time you reference it rather then giving it a direct pointer.>>
BTW, a best of both worlds approach is to do what I showed, especially if your going to perform a lot of operations on it:
Sub LockControl(strFormName as string, strControlName as string)
Dim frm as form
Dim ctl as control
Set frm = Forms(strFormName)
set ctl = Forms(strFormName)(strCont
and now you have objects to work with even though you passed in strings.
Jim.
BTW, a best of both worlds approach is to do what I showed, especially if your going to perform a lot of operations on it:
Sub LockControl(strFormName as string, strControlName as string)
Dim frm as form
Dim ctl as control
Set frm = Forms(strFormName)
set ctl = Forms(strFormName)(strCont
and now you have objects to work with even though you passed in strings.
Jim.
ASKER
Ok guys...
I built a module and placed this in it
Option Compare Database
Public Function DoStuff(strFormName As String, strControlName As String) As String
DoStuff = Forms(strFormName).Control
End Function
I'm calling it with this...
Dim s As String
s = DoStuff("MarketingVisitati
The FORM Name I got by actually doing a F2 on the name of the form from the Forms window in MS Access and copying the name.
When I look at the properties in the form...I see that the Caption is the same thing

On other forms I can access the information I need.
But on this particular form...I get a "Can't fins the Form error message"
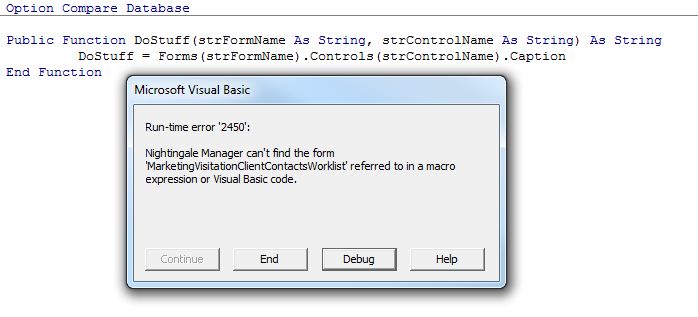
I have tried every way possible to acces this subform per question https://www.experts-exchange.com/questions/27981361/MS-Access-2003-cannot-access-Subform-making-me-crazy.html
Any ideas?
ALthough this may need to be placed in a new question?
I built a module and placed this in it
Option Compare Database
Public Function DoStuff(strFormName As String, strControlName As String) As String
DoStuff = Forms(strFormName).Control
End Function
I'm calling it with this...
Dim s As String
s = DoStuff("MarketingVisitati
The FORM Name I got by actually doing a F2 on the name of the form from the Forms window in MS Access and copying the name.
When I look at the properties in the form...I see that the Caption is the same thing
On other forms I can access the information I need.
But on this particular form...I get a "Can't fins the Form error message"
I have tried every way possible to acces this subform per question https://www.experts-exchange.com/questions/27981361/MS-Access-2003-cannot-access-Subform-making-me-crazy.html
Any ideas?
ALthough this may need to be placed in a new question?
Since you're dealing with subforms, the references to your forms and controls are going to be different - depending on where you place the code you call your public function or sub with.
This is a 5-minute (ugly) sample that demonstrates this:PublicFunction.mdb
The code in the sample uses Jim D's suggestion of using the form object rather than the form name when calling your routine. This simplifies working with subforms - especially since you need to look at your subforms as controls containing forms.
It calls the public function from a variety of places, refering to a main form, sub form and sub-subform. Take a look at the code behind the buttons for the differences.
Note - To work with a subform as a form, you need to first refer to the control housing the subform and then specify that you want to work with it as a form (hence the Me.subformControlName.Form syntax)
This is a 5-minute (ugly) sample that demonstrates this:PublicFunction.mdb
The code in the sample uses Jim D's suggestion of using the form object rather than the form name when calling your routine. This simplifies working with subforms - especially since you need to look at your subforms as controls containing forms.
It calls the public function from a variety of places, refering to a main form, sub form and sub-subform. Take a look at the code behind the buttons for the differences.
Note - To work with a subform as a form, you need to first refer to the control housing the subform and then specify that you want to work with it as a form (hence the Me.subformControlName.Form syntax)
<<
The FORM Name I got by actually doing a F2 on the name of the form from the Forms window in MS Access and copying the name.
>>
Also - when dealing with subform paths, the "subform name" you need to refer to is actually the name of the control that houses your subform -- which might not be the same as the name you see in the Forms window. The subform control name is determined by right-clicking the 'frame' of the subform control in your form's design, bringing up its property sheet and looking up the Name property.
The FORM Name I got by actually doing a F2 on the name of the form from the Forms window in MS Access and copying the name.
>>
Also - when dealing with subform paths, the "subform name" you need to refer to is actually the name of the control that houses your subform -- which might not be the same as the name you see in the Forms window. The subform control name is determined by right-clicking the 'frame' of the subform control in your form's design, bringing up its property sheet and looking up the Name property.
ASKER
Hey folks,
Thanks. Looks like I should do a split on the points between mbizup and Jim D
Any objections?
Jim was first and mbizup gave a working example.
Thanks. Looks like I should do a split on the points between mbizup and Jim D
Any objections?
Jim was first and mbizup gave a working example.
Looks like I need to go back to JimD; there are two Jim's in the thread. Jim Horn was first.
I'm fine with no points or whatever.
JimD.
I'm fine with no points or whatever.
JimD.
ASKER
Well done guys.
I wanted everyone with valid input to get points
I wanted everyone with valid input to get points
Function/Sub:
Sub LockControls(strFormName as string)
Dim frm as form
Set frm = Forms(strFormName)
frm is now a form object and you can access it's methods and properties. ie.
If frm.visible = True then
Jim.