Hyperlinks no longer work after converting .wps files to .docx
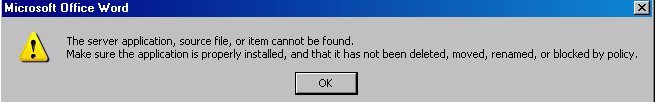 Recently I converted over a thousand .wps files to .docx, using a VB macro. Now I have discovered that embedded URL shortcuts no longer open their respective web pages. These shortcuts were embedded in the .wps files, and there are still shortcut icons in the .docx files, but when they are clicked, there is an error message (see screenshot). I hope I won't need to manually recreate every embedded URL!
Recently I converted over a thousand .wps files to .docx, using a VB macro. Now I have discovered that embedded URL shortcuts no longer open their respective web pages. These shortcuts were embedded in the .wps files, and there are still shortcut icons in the .docx files, but when they are clicked, there is an error message (see screenshot). I hope I won't need to manually recreate every embedded URL!
check the shortcut properties -you may see where it has screwed up and be able to do a search/replace to fix
ASKER
Thank you for your comments. Right-clicking a shortcut, the menu has cut, copy, paste, package object, hyperlink, insert caption, borders & shading, and format object. There is no option for Properties. I tried installing Microsoft Office Compatibility Pack, but it hasn't changed the behavior.
what are the properties in "hyperlink" as this is the bit that is wrong
ASKER
Test.docxThe "hyperlink" context menu does not have properties. It asks for an address to insert a hyperlink. I attached a sample docx file with non-functioning embedded URL shortcuts.
looks like your conversion has stripped all the hyperlink info, however not sure how you managed to get the above error in the first place
ASKER
I just found that these links still work on a different machine running Windows 7. The machine with the error message is running Windows XP SP-3.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank you for your thorough analysis. Originally, the URL shortcuts were embedded by copying a Windows Favorite shortcut to Wordpad, and from there, pasting it into a wps file. I could not paste it directly without using Wordpad as an intermediate step.
I am using Word 2007, having recently converted all my wps files to Word. Much to my relief, after posting this question I found that one of my computers still opens web pages when the shortcuts in Word are clicked. That is a Windows 7 desktop. My Windows XP laptop won't open the URL, and displays the error message. So, I'm not in as desperate a situation as I first thought. Still, if there is a way to be able to work with these files on my laptop, that would be helpful.
I'm not really eager to convert the embedded shortcuts into text hyperlinks, and would prefer to leave them as icons, if there is a way to make them useful.
A sample of the original wps file with embedded shortcuts can be downloaded from www.mauitradewinds.com/Experts I can't embed it here, because .wps is not an accepted file extension for Experts Exchange attachments.
I am using Word 2007, having recently converted all my wps files to Word. Much to my relief, after posting this question I found that one of my computers still opens web pages when the shortcuts in Word are clicked. That is a Windows 7 desktop. My Windows XP laptop won't open the URL, and displays the error message. So, I'm not in as desperate a situation as I first thought. Still, if there is a way to be able to work with these files on my laptop, that would be helpful.
I'm not really eager to convert the embedded shortcuts into text hyperlinks, and would prefer to leave them as icons, if there is a way to make them useful.
A sample of the original wps file with embedded shortcuts can be downloaded from www.mauitradewinds.com/Experts I can't embed it here, because .wps is not an accepted file extension for Experts Exchange attachments.
Aaah, good. Thanks for that link. I was going to ask for an example. I don't have Works, but can remote into someone else's computer that has Works and open the WPS file natively. It looks like it was created in Works 2000. I'll see what I can figure out. Incidentally, if you ever need to attach a file that isn't accepted by Experts-Exchange, you can always change the extension to .TXT as long as you indicate what it needs to be renamed back to. It may show a file mismatch notification here.
Here is the attached WPS file, so you can always remove the "Experts" folder from your site if you wish.
<EDIT: attachment removed meantime>
I found what appears to be some leftover metadata that does not show as text and may be something that you aren't really keen on others seeing. Open the file in Notepad and you'll see what I mean.
Do all of your converted files contain links in this format, and is that the ONLY content in all of them, or is there text also?
Here is the attached WPS file, so you can always remove the "Experts" folder from your site if you wish.
<EDIT: attachment removed meantime>
I found what appears to be some leftover metadata that does not show as text and may be something that you aren't really keen on others seeing. Open the file in Notepad and you'll see what I mean.
Do all of your converted files contain links in this format, and is that the ONLY content in all of them, or is there text also?
ASKER
Thank you for your comments. Works 2000 is the application which created those files. The files contain text as well as links in that format. I initially uploaded the wps file after converting it to .txt format. When I downloaded it from this site and converted it back to wps, it would not open. So I edited my comment and removed the embedded file. I see what you mean about the meta data. I removed the text from that file, thinking all that was left was the embedded shortcuts and their icons. Anyhow, the remaining data is not confidential, but thank you for the head's up.
ASKER
I installed Windows 7 and Office 2007 on the laptop, and the links open now. It's only under Windows XP that the error message appears.
Yes, there's something screwy with XP. It's probably the way the Object Linking and Embedding (OLE) functionality is handled in XP and has apparently been improved in later Windows versions.
I had hoped that perhaps the WPS documents were just a method of archiving links and didn't contain text, because I saw a way that I could probably have extracted the hyperlinks from each document and created new Word documents with standard hyperlinked images. My idea wouldn't work with additional text in the documents. I'm presuming that your preference for retaining hyperlinked images is probably so that the original layout (page breaks, etc) is maintained.
I think I'm going to have to throw in the towel for this contest. I posted a link to this question in your other question where the expert named terencino provided you with the Macro code in the hope that he will be alerted and visit here with some ideas.
By the way, if you see a UK IP Address beginning 79.78 in your website logs it was just me wondering if I could afford one night in the Star Wind ;-)
I had hoped that perhaps the WPS documents were just a method of archiving links and didn't contain text, because I saw a way that I could probably have extracted the hyperlinks from each document and created new Word documents with standard hyperlinked images. My idea wouldn't work with additional text in the documents. I'm presuming that your preference for retaining hyperlinked images is probably so that the original layout (page breaks, etc) is maintained.
I think I'm going to have to throw in the towel for this contest. I posted a link to this question in your other question where the expert named terencino provided you with the Macro code in the hope that he will be alerted and visit here with some ideas.
By the way, if you see a UK IP Address beginning 79.78 in your website logs it was just me wondering if I could afford one night in the Star Wind ;-)
Thank you David. I wasn't expecting points for throwing in the towel. It's appreciated. I hope you can get this all sorted out painlessly.
ASKER
Thank you Bill. Guests from Oxford just left this morning, and we got a new reservation yesterday, from a honeymoon couple in York. So, it can be done!