SBS 2011 Backup Freezes Server
I'm having recent troubles with an SBS 2011 server (HP Proliant ML350) where the backup is causing the server to become unresponsive, and the only way we can fix it is by doing a hard reset (holding in the power button until it turns off, and then turning it back on - not really good for the server).
The problem has only started in the last week, after running fine for the previous 4-5 months. There are two USB backup drives being used (both Seagate GoFlex 1.5TB), and the problem happens with both drives. I have run chkdsk on both of these drives and they come up and clean (no errors). I have used the same model of drive for other SBS 2011 backups without problems.
The server itself has two drives (C: and E:) - have run chkdsk on these and again - all clean.
Just prior to the server freezing, there are lots (thousands) of Disk Errors (Event ID 7) in the System log, saying "The device, \Device\Harddisk2\DR4, has a bad block).
Any suggestions as to what I should do next to fix this? This one's a bit of a puzzle.
The problem has only started in the last week, after running fine for the previous 4-5 months. There are two USB backup drives being used (both Seagate GoFlex 1.5TB), and the problem happens with both drives. I have run chkdsk on both of these drives and they come up and clean (no errors). I have used the same model of drive for other SBS 2011 backups without problems.
The server itself has two drives (C: and E:) - have run chkdsk on these and again - all clean.
Just prior to the server freezing, there are lots (thousands) of Disk Errors (Event ID 7) in the System log, saying "The device, \Device\Harddisk2\DR4, has a bad block).
Any suggestions as to what I should do next to fix this? This one's a bit of a puzzle.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
When you look in Disk Manager what hard disk is indicated?
What is the RAID setup on the server? Hardware RAID controller? SAS or SATA for disks? RAID 5, 6, 10?
Philip
What is the RAID setup on the server? Hardware RAID controller? SAS or SATA for disks? RAID 5, 6, 10?
Philip
ASKER
The RAID is hardware RAID using the HP B110i controller.
There's 2 x 250GB SATA disks setup as RAID 1 for the OS, and another 2 x 1TB SATA disks setup as RAID 1 for the data.
I've run the HP diagnostics software on all the disks and they all come back clean.
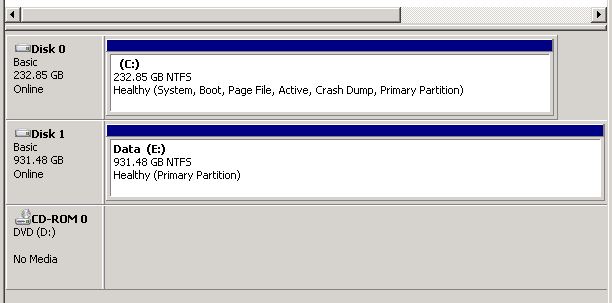
Not sure what you mean by which hard disk is "indicated" in disk manager? It simply shows me the hard drives currently attached to the system as it would normally.
There's 2 x 250GB SATA disks setup as RAID 1 for the OS, and another 2 x 1TB SATA disks setup as RAID 1 for the data.
I've run the HP diagnostics software on all the disks and they all come back clean.
Not sure what you mean by which hard disk is "indicated" in disk manager? It simply shows me the hard drives currently attached to the system as it would normally.
\Device\Harddisk2\DR4
The way that error code reads it sounds like one of the disks in the second RAID set has some bad blocks on it.
This one?
http://h18004.www1.hp.com/products/servers/proliantstorage/arraycontrollers/smartarrayb110i/index.html
http://h20000.www2.hp.com/bizsupport/TechSupport/Document.jsp?objectID=c02555555&prodSeriesId=3958193
This is a software RAID based setup. So, between the SATA disks and the software RAID setup I would not expect there to be much in the way of logging for bad sectors as there would be with a hardware RAID setup.
Philip
The way that error code reads it sounds like one of the disks in the second RAID set has some bad blocks on it.
This one?
http://h18004.www1.hp.com/products/servers/proliantstorage/arraycontrollers/smartarrayb110i/index.html
http://h20000.www2.hp.com/bizsupport/TechSupport/Document.jsp?objectID=c02555555&prodSeriesId=3958193
This is a software RAID based setup. So, between the SATA disks and the software RAID setup I would not expect there to be much in the way of logging for bad sectors as there would be with a hardware RAID setup.
Philip
ASKER
Well there you go - I always thought that controller was hardware-based, like the P410i!
Is there a way I can match up \Device\Harddisk2\DR4 to a physical disk? I assume that's what you were getting at with the Disk Management screen?
Here's a screenshot from the Disk Management window - note that none of the backup drives are currently plugged in.
Is there a way I can match up \Device\Harddisk2\DR4 to a physical disk? I assume that's what you were getting at with the Disk Management screen?
Here's a screenshot from the Disk Management window - note that none of the backup drives are currently plugged in.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
The server is at a remote customer's site which I don't have access to today, however I am sending them two new backup drives (Lacie Rugged Mini 1TB) which they should receive tomorrow.
I will configure them remotely and attempt to run a backup and report back here.
I will configure them remotely and attempt to run a backup and report back here.
RDGateway not set up?
Remote Web Access not set up?
Philip
Remote Web Access not set up?
Philip
ASKER
Yes I can log in remotely but there is nobody at the customer's end today that I would trust to plug in the right drives correctly. The usual person responsible for their backups is away but they will be back tomorrow.
Got it. Long day. Grey matter no longer responding. ;)
Philip
Philip
ASKER
Completely understand. Thanks for your help so far, hopefully we can get this resolved tomorrow.
You would think they would test bad somehow, but my experience has been they only show bad under heavy load. They eventually get worse until they fill the event logs and hang the server. That has happened to me twice with two different servers.
ASKER
Latest update - after configuring the two new USB backup drives it seems the backup now runs successfully. So the problem was indeed the USB drives, even though they didn't test as "bad" with chkdsk!
I will get them back and run Seagate diagnostic Seatools on them and see if that shows up any problems.
Thanks for your help guys.
I will get them back and run Seagate diagnostic Seatools on them and see if that shows up any problems.
Thanks for your help guys.
ASKER
Just strange that both drives started doing the same behaviour at the same time.