Wordpress remove comment info
Hi,
I'm building a website with wordpress, and i installed a theme that i downloaded from the internet. My homepage is a blog, and when i place an article i can click 'comment'.
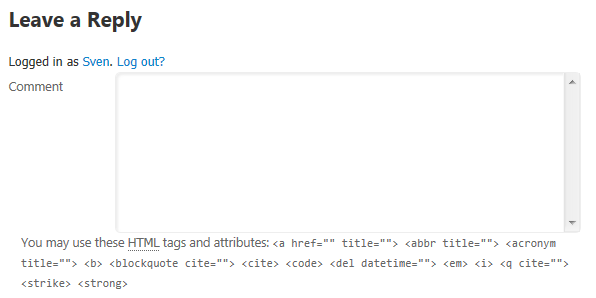
Below the comment box there is some text about HTML tags that i want to get rid of (see pic). Can someone help me with that?
I'm building a website with wordpress, and i installed a theme that i downloaded from the internet. My homepage is a blog, and when i place an article i can click 'comment'.
Below the comment box there is some text about HTML tags that i want to get rid of (see pic). Can someone help me with that?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Hi Andy,
Here is the link to the theme that I use;
http://www.riotreactions.eu/wordpress-themes/mantra/mantra-1-9-9-5
Your help would be appreciated....
When you're at it, can you maybe take a look to how I can remove the footer info of the creators of the theme?
Thanks!!!
Here is the link to the theme that I use;
http://www.riotreactions.eu/wordpress-themes/mantra/mantra-1-9-9-5
Your help would be appreciated....
When you're at it, can you maybe take a look to how I can remove the footer info of the creators of the theme?
Thanks!!!
ASKER
It is a setting in the theme that i use!
If you have a link either to your site or to the download for your theme, I can take a look and give you more specific advice on what you'll need to edit. More than likely, you're going to need to make a small modification to your theme. Thanks!