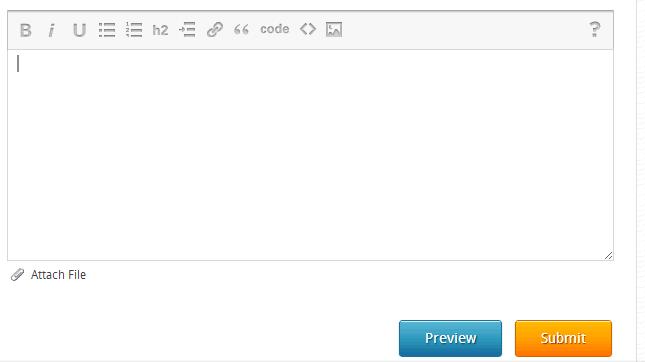
What control did they use on this?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Here you go!
http://docs.cksource.com/CKEditor.NET
http://docs.cksource.com/CKEditor.NET
ASKER
Thanks for the input everyone. :)
ASKER
Do you know any documents or tutorial for this control?