Cannot install ati catalyst driver in my laptop HPG62/win7 64bit
I have a laptop HP G62 with windows 7 64bit.
I downloaded the ati graphics driver package which inculdes the catalyst center from manufacturer's site.
I cannot install the driver package.
The package first extracts the required files in my hard disk c:\swsetup.
Then the "ATI Catalyst Install Manager" starts and fails with error:
"This application has been launched without the required privileges. Please launch this application with an administrative privilege".
I am a user with local admin privileges.
I also tried to launch the package with "run as admin" privileges. Same error again.
I changed the extract folder to my second partition g:\swsetup and I manually tried to run the "setup.exe" file with "run as admin". Same error.
I also tried to:
Right click on "setup.exe"-> compatibility tab -> privilege level -> check "run as admin".
Nothing again. Same error.
Any thoughts ?
I downloaded the ati graphics driver package which inculdes the catalyst center from manufacturer's site.
I cannot install the driver package.
The package first extracts the required files in my hard disk c:\swsetup.
Then the "ATI Catalyst Install Manager" starts and fails with error:
"This application has been launched without the required privileges. Please launch this application with an administrative privilege".
I am a user with local admin privileges.
I also tried to launch the package with "run as admin" privileges. Same error again.
I changed the extract folder to my second partition g:\swsetup and I manually tried to run the "setup.exe" file with "run as admin". Same error.
I also tried to:
Right click on "setup.exe"-> compatibility tab -> privilege level -> check "run as admin".
Nothing again. Same error.
Any thoughts ?
The catalyst control center?
Is this what your trying to install?
As you mention ati graphics driver package which includes the catalyst centre
Did you have this control Panel before then when you update drivers it also updates.
The original Catalyst consisted of these elements:
1.A new, unified driver for ATI Radeon graphics cards
2.Hydravision, ATI's proprietary desktop management software
3.An ATI "Multimedia Center"
4.ATI's Remote Wonder software
5.A new AGP diagnostic and stability tool
6.A newly redesigned control panel
This application requires Microsoft .NET Framework.
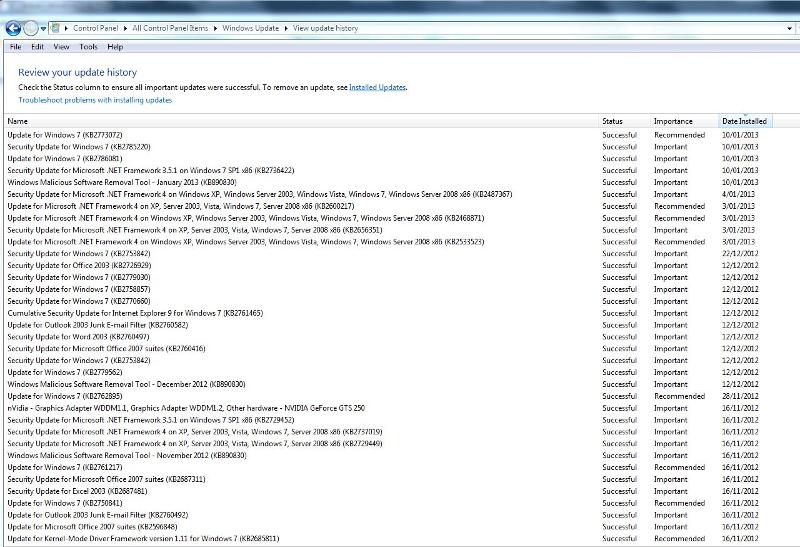
Check your windows updates please as it's offered whenever there is an update in a specific order
To apply this update, you must have the .NET Framework 4 or the Microsoft .NET Framework 4 Client Profile installed.
http://support.microsoft.com/kb/2533523
Is this what your trying to install?
As you mention ati graphics driver package which includes the catalyst centre
Did you have this control Panel before then when you update drivers it also updates.
The original Catalyst consisted of these elements:
1.A new, unified driver for ATI Radeon graphics cards
2.Hydravision, ATI's proprietary desktop management software
3.An ATI "Multimedia Center"
4.ATI's Remote Wonder software
5.A new AGP diagnostic and stability tool
6.A newly redesigned control panel
This application requires Microsoft .NET Framework.
Check your windows updates please as it's offered whenever there is an update in a specific order
To apply this update, you must have the .NET Framework 4 or the Microsoft .NET Framework 4 Client Profile installed.
http://support.microsoft.com/kb/2533523
try enabling the real admin - you can disable it again after the install :
http://www.sevenforums.com/tutorials/507-built-administrator-account-enable-disable.html
http://www.sevenforums.com/tutorials/507-built-administrator-account-enable-disable.html
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ha - on domain...that changes things - you never told us that..
Then, have you installed the chipset drivers first? That is essential to make the other drivers work.
Apart from that, why do you need to install the driver? usually they are already there, and the update system should automatically get the correct drivers. If you had to re-install the system the drivers are normally also included when you use the supported factory restore from the recovery partition of if you used the recovery DVD's you made when you got the PC.