Users logging on to domain accounts with current password despite "User must change password at next logon" flag
Hey folks,
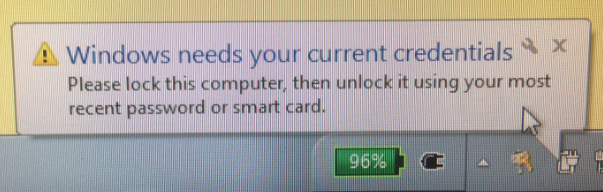
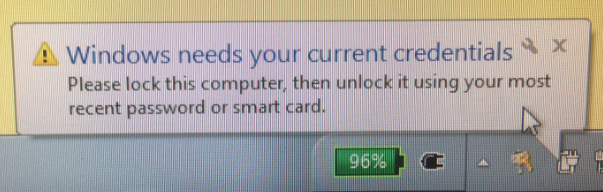
After flagging multiple domain user accounts with the "User must change password at next logon" flag in Active Directory Users and Computers, hours later upon logging in a percentage of them are still able to login using their locally cached password credentials. Upon logging in, they are soon afterwards prompted with a popup asking them to log in with their current credentials (see embedded image).
INFO:
*All computers are attached via ethernet cable to the internal network
*All computer accounts and user accounts are in good/equivalent standing on our network, with the same memberships
Frankly, I'm stumped. How can we ensure that the "must change password" flag snags all of our users before logging on, and not just some?
Thanks.
After flagging multiple domain user accounts with the "User must change password at next logon" flag in Active Directory Users and Computers, hours later upon logging in a percentage of them are still able to login using their locally cached password credentials. Upon logging in, they are soon afterwards prompted with a popup asking them to log in with their current credentials (see embedded image).
INFO:
*All computers are attached via ethernet cable to the internal network
*All computer accounts and user accounts are in good/equivalent standing on our network, with the same memberships
Frankly, I'm stumped. How can we ensure that the "must change password" flag snags all of our users before logging on, and not just some?
Thanks.
a percentage of them are still able to login using their locally cached password credentials That means that they don't have access to the domain controller during the logon phase which they NEED to have..
ASKER
"That means that they don't have access to the domain controller during the logon phase which they NEED to have.. "
The machines are attached directly to our internal network (and can be seen, for instance, from the domain controller via management tools or pinging) and have this issue despite that.
The machines are attached directly to our internal network (and can be seen, for instance, from the domain controller via management tools or pinging) and have this issue despite that.
When the machine boots up the network is not ready and they are logging on before the network is stable and authenicating with a domain controller and the machine is using the cached credentials.
Add a Group Policy
Computer Configuration|Administrati
gpupdate /force
Add a Group Policy
Computer Configuration|Administrati
gpupdate /force
ASKER
That's definitely a solution, but shouldn't a 30 minute window (or a 2 hour window) be enough for the client nodes to communicate automatically with the domain controller? Is there something I can enter on the command line to "synchronize" the DC with the client computers in terms of account credentials?
I've seen this problem before. Back then, it was a problem with client security software that simply changed the client-server communication only after logon.
So for a test, uninstall your AV/firewall software if present and reboot. Also update your NIC drivers.
So for a test, uninstall your AV/firewall software if present and reboot. Also update your NIC drivers.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.