VPN clients can't connect - Error 812
Hi there,
We recently migrated one of our client's server from SBS2008 to Server Essentials 2012. The SBS used to manage the VPN connections but now the new policy we've created on Essentials 2012 doesn't seem to be allowing any connections. Windows clients receive the following error:
Error 812 : The connection was prevented because of a policy configured on your RAS/VPN server. Specifically, the authentication method used by the server to verify your username and password may not match the authentication method configured in your connection profile. Please contact the Administrator of the RAS server and notify them of this error.
We've confirmed all necessary ports are open on the firewall (though the error message indicates to me that it's more of a policy issue rather than establishing a connection) and also tried connecting to VPN from the LAN to the server's local IP and received the same error.
We've confirmed that the user accounts connecting are in the VPN access group that we've specified in the policy, we have deleted all NPS policies and started from scratch, we have also confirmed that the static range / pool has been set.
After a failed connection attempt, the following error shows in the event viewer under System on the server with Event ID 20271
"The user ##### connected from 192.168.#.# but failed an authentication attempt due to the following reason: The connection could not be established because the authentication method used by your connection profile is not permitted for use by an access policy configured on the RAS/VPN server. Specifically, this could be due to configuration differences between the authentication method selected on the RAS/VPN server and the access policy configured for it.
"
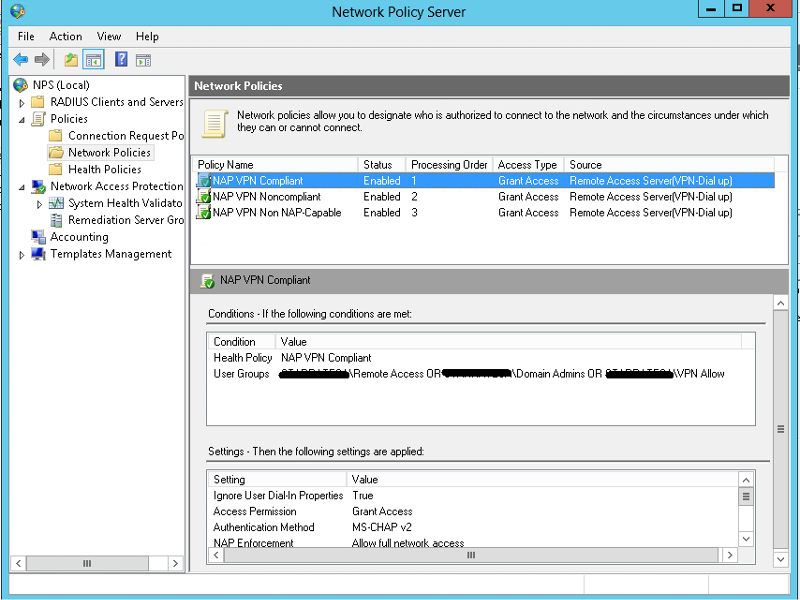
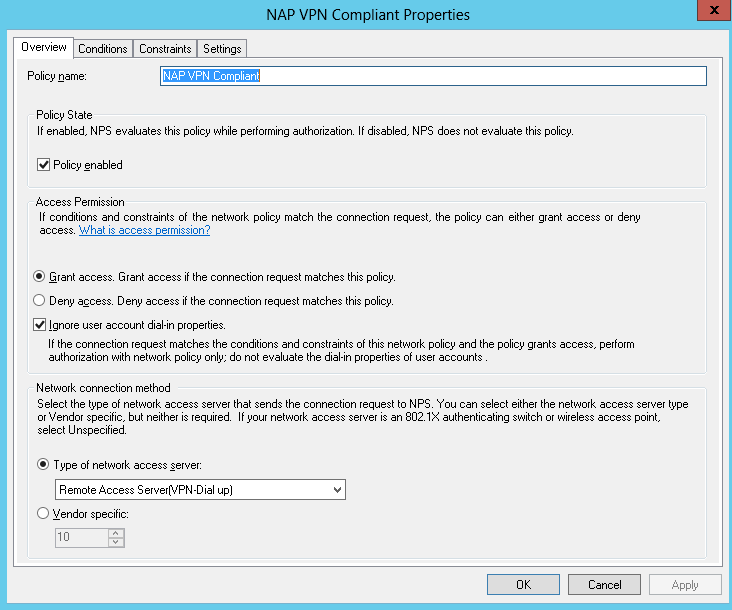
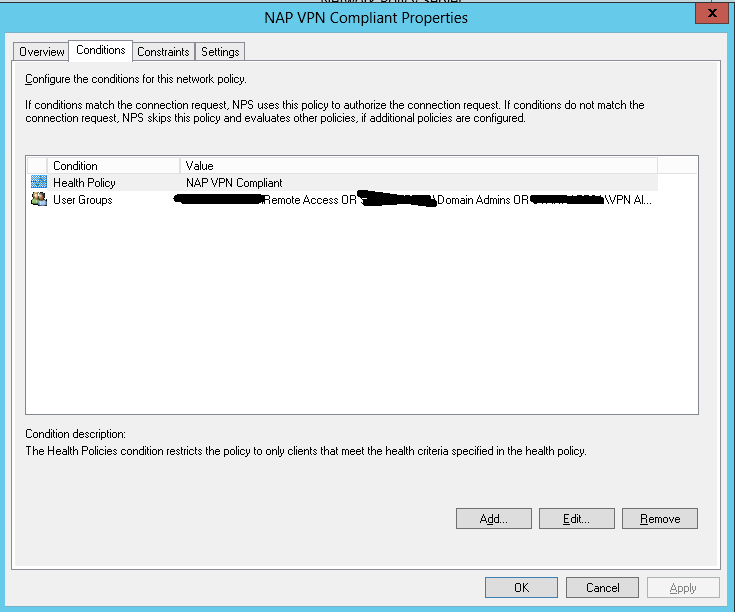
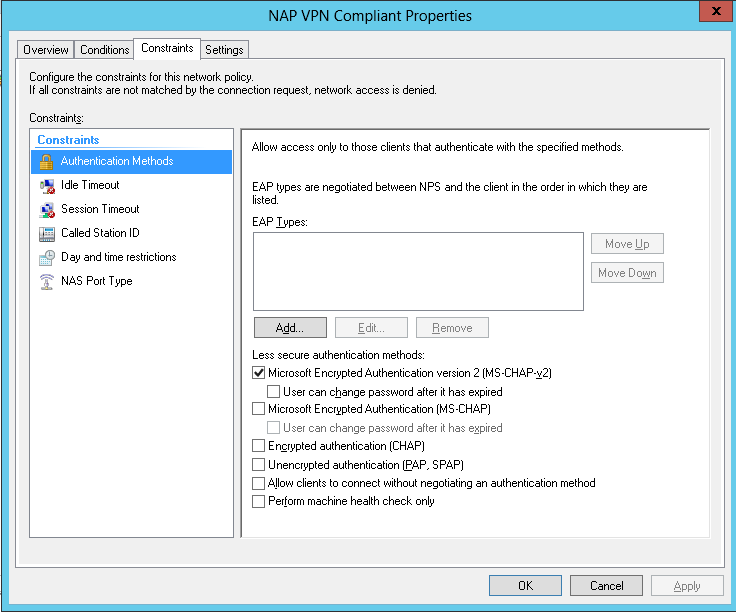
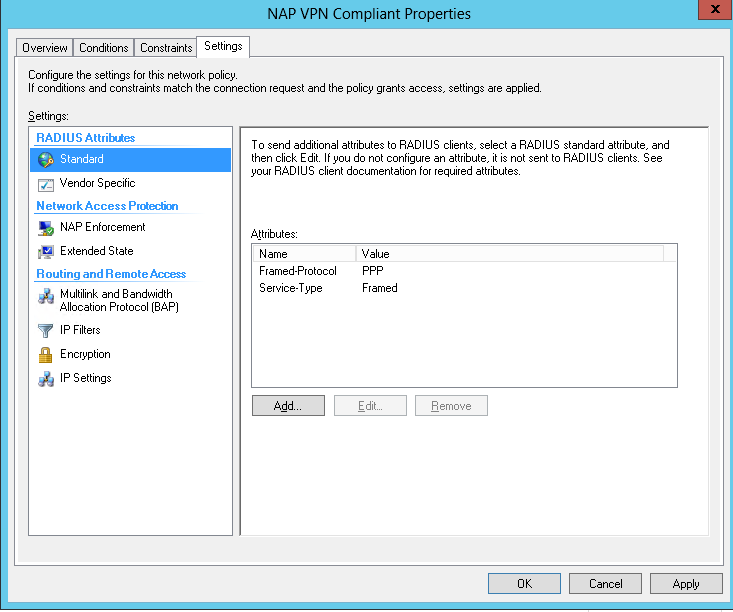
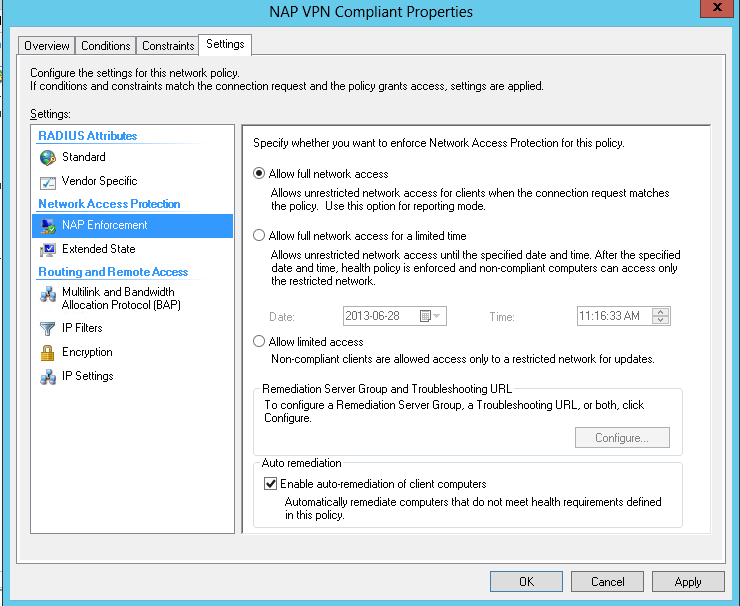
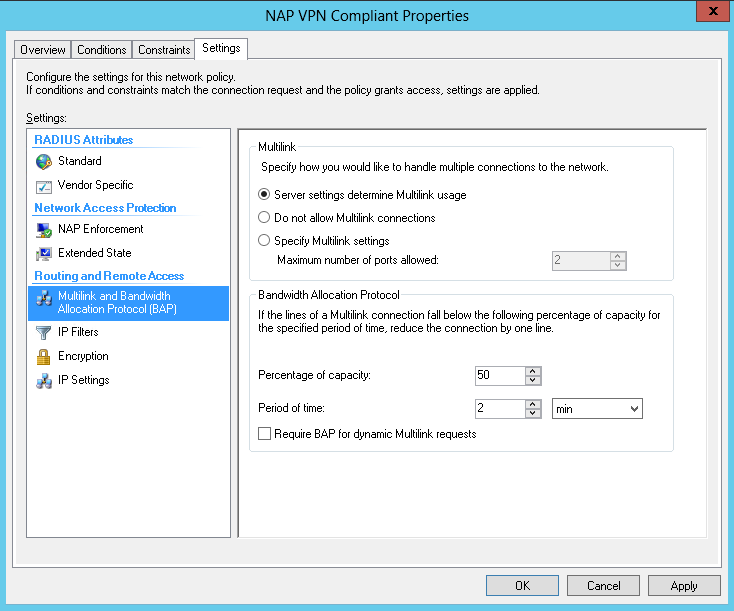
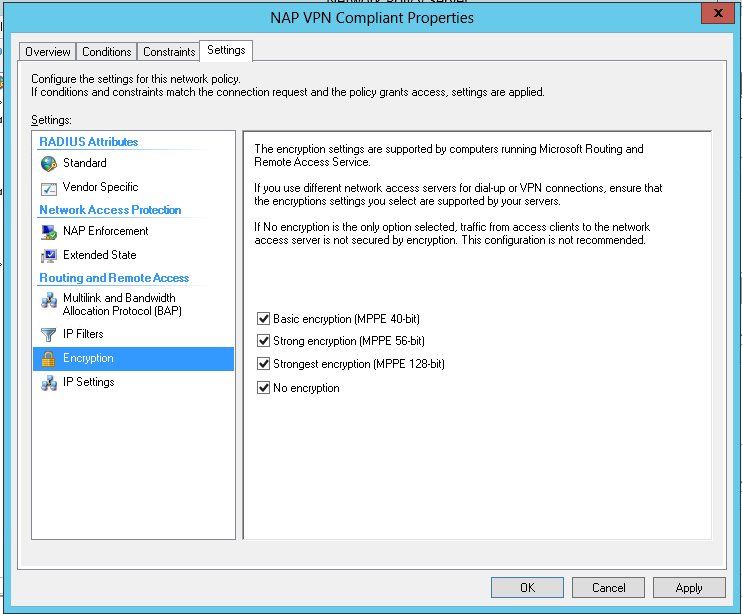
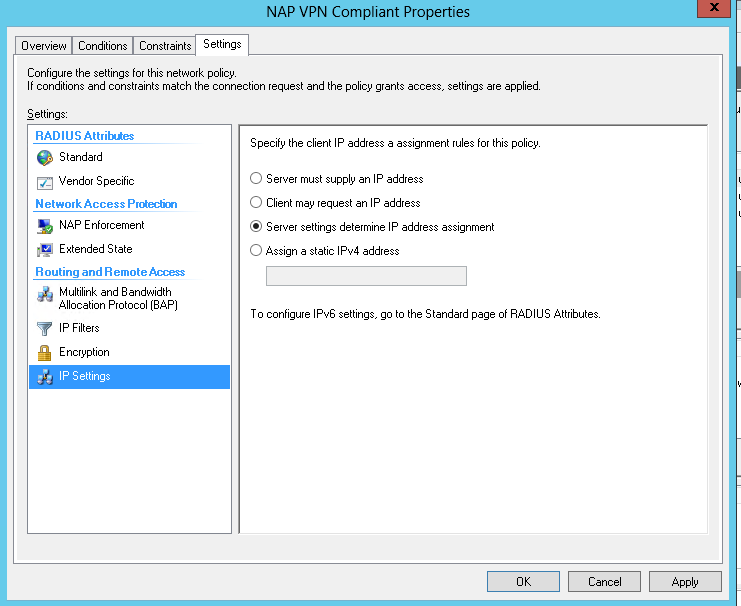
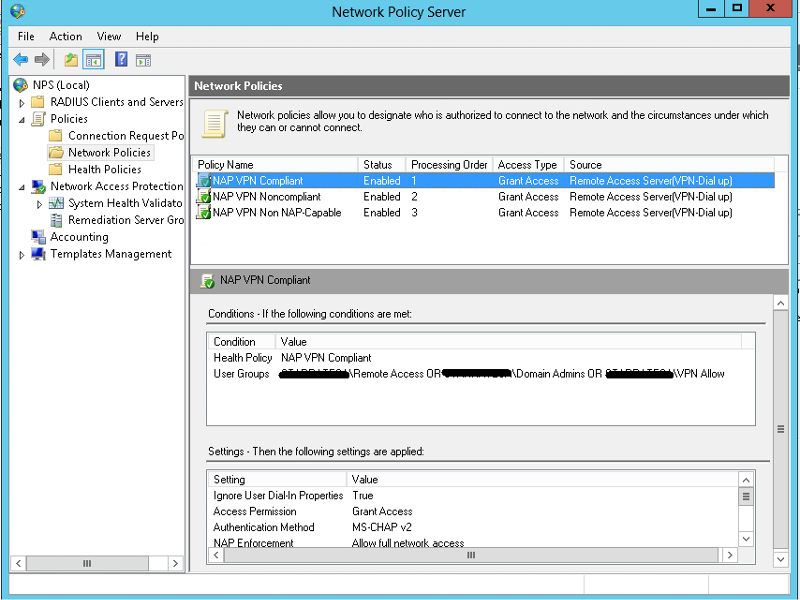
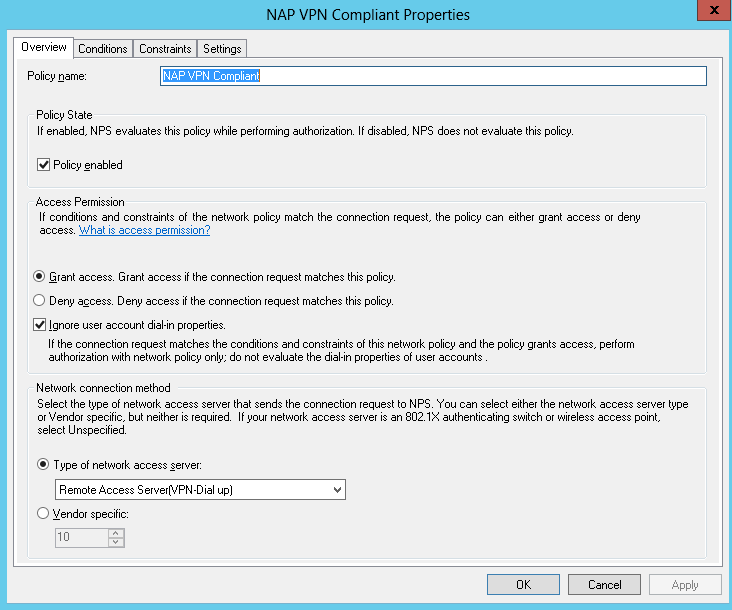
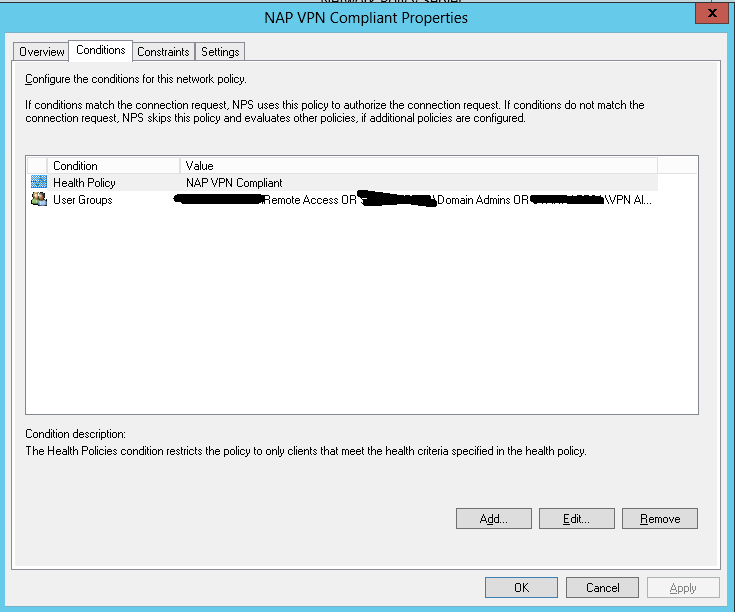
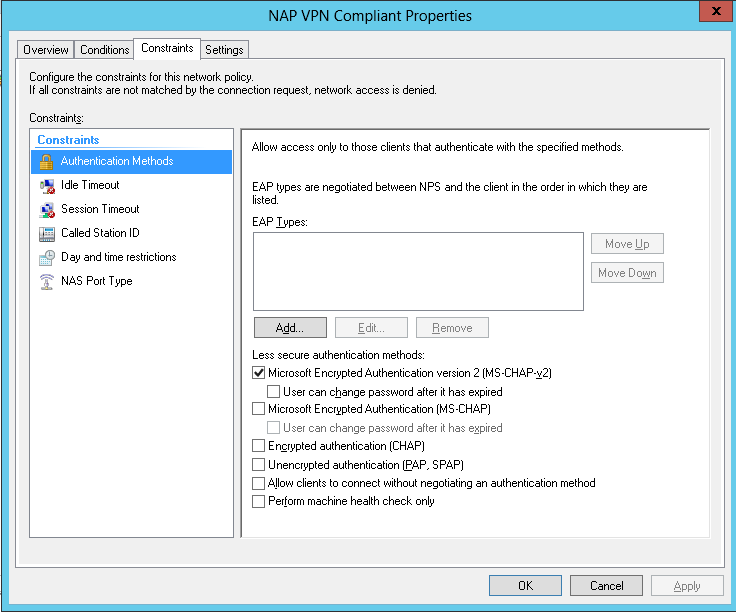
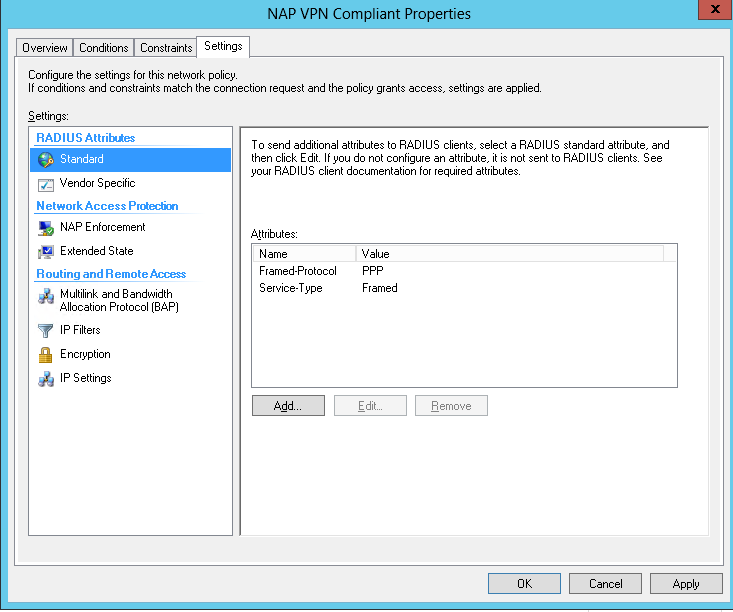
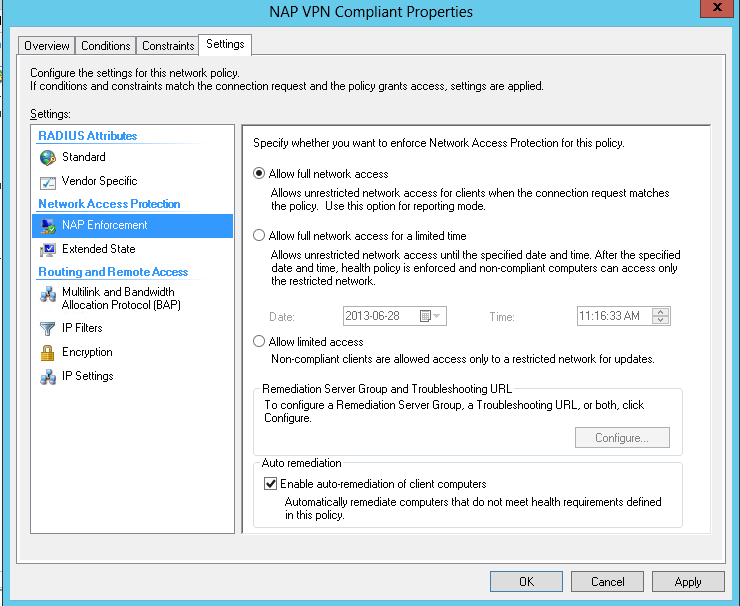
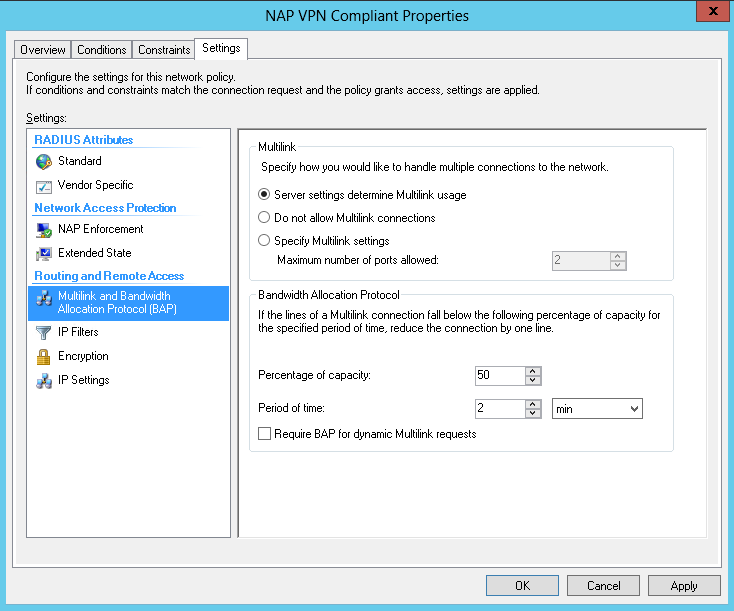
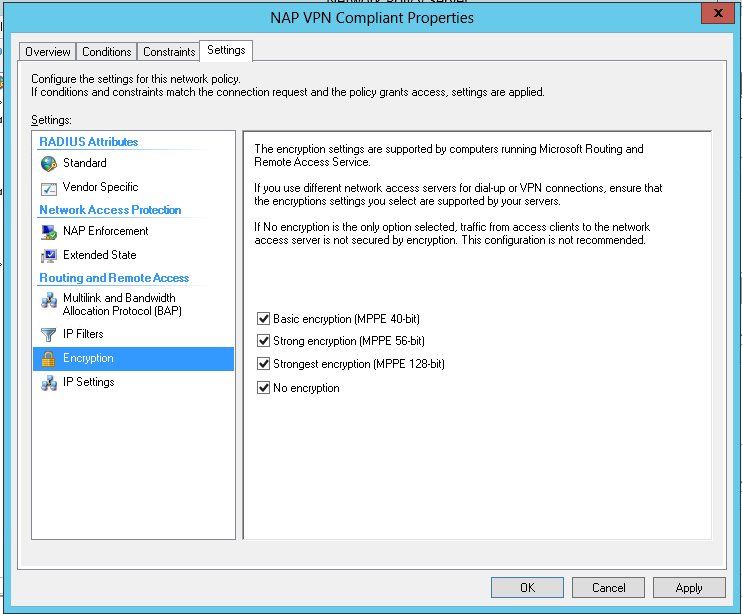
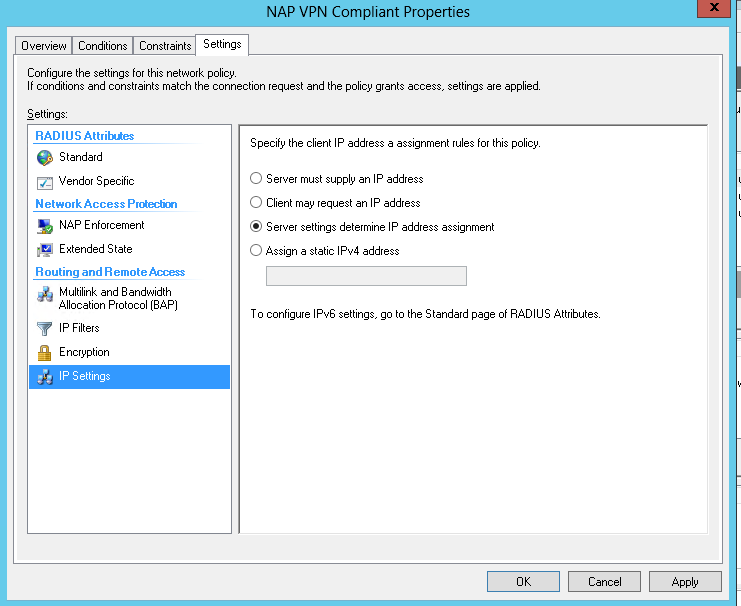
See screenshots of policy configuration below
We recently migrated one of our client's server from SBS2008 to Server Essentials 2012. The SBS used to manage the VPN connections but now the new policy we've created on Essentials 2012 doesn't seem to be allowing any connections. Windows clients receive the following error:
Error 812 : The connection was prevented because of a policy configured on your RAS/VPN server. Specifically, the authentication method used by the server to verify your username and password may not match the authentication method configured in your connection profile. Please contact the Administrator of the RAS server and notify them of this error.
We've confirmed all necessary ports are open on the firewall (though the error message indicates to me that it's more of a policy issue rather than establishing a connection) and also tried connecting to VPN from the LAN to the server's local IP and received the same error.
We've confirmed that the user accounts connecting are in the VPN access group that we've specified in the policy, we have deleted all NPS policies and started from scratch, we have also confirmed that the static range / pool has been set.
After a failed connection attempt, the following error shows in the event viewer under System on the server with Event ID 20271
"The user ##### connected from 192.168.#.# but failed an authentication attempt due to the following reason: The connection could not be established because the authentication method used by your connection profile is not permitted for use by an access policy configured on the RAS/VPN server. Specifically, this could be due to configuration differences between the authentication method selected on the RAS/VPN server and the access policy configured for it.
"
See screenshots of policy configuration below
ASKER
Thanks Patricksr1972,
New server is not RADIUS. I've tried matching the authentication protocols but it still doesn't come right. User has dial in access granted. Can you please elaborate/advise on " edit "Connections to Microsoft Routing and Remote Access Server"". I've looked through the RRAS console and can't see anything out of place.
New server is not RADIUS. I've tried matching the authentication protocols but it still doesn't come right. User has dial in access granted. Can you please elaborate/advise on " edit "Connections to Microsoft Routing and Remote Access Server"". I've looked through the RRAS console and can't see anything out of place.
Did you use the Essentials console wizard to create the VPN? You should rather than using RRAS. If so I have found though the 812 error implies it is a server issue, it can be the wrong protocol configuration on the client.
3 'things' I would check:
-Make sure in the user's properties in the Essentuals console they have the ability to connect to the VPN checked
-On the connecting client, under VPN properties, Security, make sure "allow these protocols" and "MS Chap v2" are checked
-On the same tab, try selecting PPTP as the VPN type rather than automatic.
3 'things' I would check:
-Make sure in the user's properties in the Essentuals console they have the ability to connect to the VPN checked
-On the connecting client, under VPN properties, Security, make sure "allow these protocols" and "MS Chap v2" are checked
-On the same tab, try selecting PPTP as the VPN type rather than automatic.
ASKER
Thanks for your reply,
I used the wizard.to create it and have checked those 3 items a number of times but still have the problem
I used the wizard.to create it and have checked those 3 items a number of times but still have the problem
That is interesting (RRAS policy). That is the default policy created if you build the VPN using RRAS (or the RRAS wizard), rather than the Essentials wizard. If you right click on "Remote Access Policies) you should not have a properties option butt rather an option to "launch NPS". you could try right clicking on the server name in RRAS and choose disable, which should unconfigure RRAS, and then use the Essentials wizard under Anywhere Access in the console.
2011 Essentiasl didn't have the wizard and you had to do it manually. I bloged about it. I don't recomend using this method to configure it on 2012, but you could review it to compare configurations, they are very similar.
http://blog.lan-tech.ca/2012/01/28/sbs-2011-essentials-configuring-vpn-access/
2011 Essentiasl didn't have the wizard and you had to do it manually. I bloged about it. I don't recomend using this method to configure it on 2012, but you could review it to compare configurations, they are very similar.
http://blog.lan-tech.ca/2012/01/28/sbs-2011-essentials-configuring-vpn-access/
ASKER
I deleted the ones that were created by the wizard as we had the same issue before when the wizard ones were there (812 Error and same errors in event viewer) and recreated the policies from scratch following another blog which suggested this as a resolution.
Once recreated the same 812 error was there as before when the wizard had created the policies.
Can we re-run the wizard how do we do this? (Do you think this would have any effect?)
When you say have you made sure the users have dial-in access what do you mean? (As we have created a group (remote access) which is in the policy to have granted access which the users are appart of this group, we have not set the activities directory properties for the user as this is normally ignored and the NPS policy is applied?)
Once recreated the same 812 error was there as before when the wizard had created the policies.
Can we re-run the wizard how do we do this? (Do you think this would have any effect?)
When you say have you made sure the users have dial-in access what do you mean? (As we have created a group (remote access) which is in the policy to have granted access which the users are appart of this group, we have not set the activities directory properties for the user as this is normally ignored and the NPS policy is applied?)
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
We have rerun the wizard and it seems to be working properly now. Thanks everyone for all your help.
The error is very straightforward, there are different protocols used to communicate. Did you set up the new server to use radius or ....? Please make sure both sides speak the same language.
Oh last minutes brainwave.. do the users have dial-in rights? and secondly i am curious; in your RRAS management toolbox did you edit "Connections to Microsoft Routing and Remote Access Server" (if not RRAS connections are not possible)