How do I get rid of risidual user accounts in a workgroup environment.
Good evening experts,
this is probably going to be an easy one, but is there a simply way to get ride of user account left over folders when I delete them. Let me explain with visuals, because a picture is worth a thousand words. Here is my scenario:
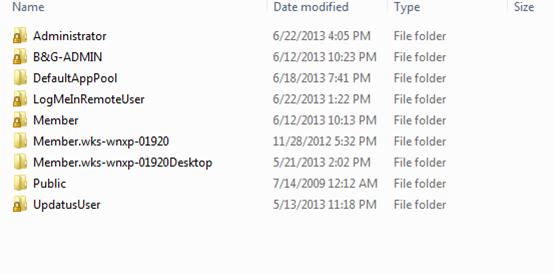
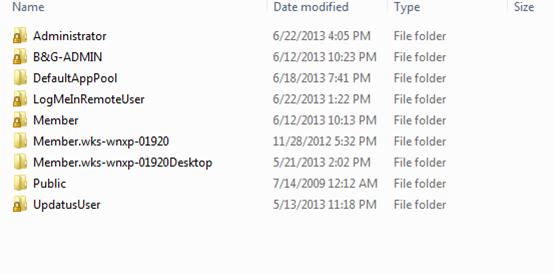
Here is a hypothetical member user list:
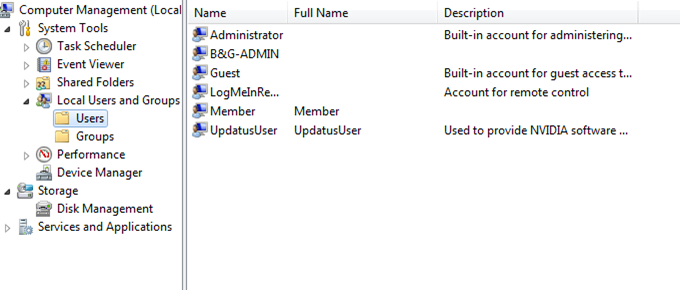
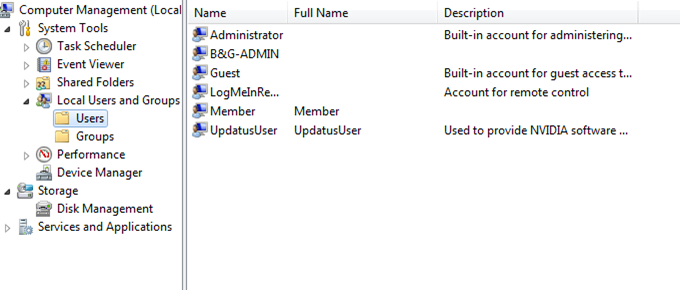
Here is where I go to delete accounts:
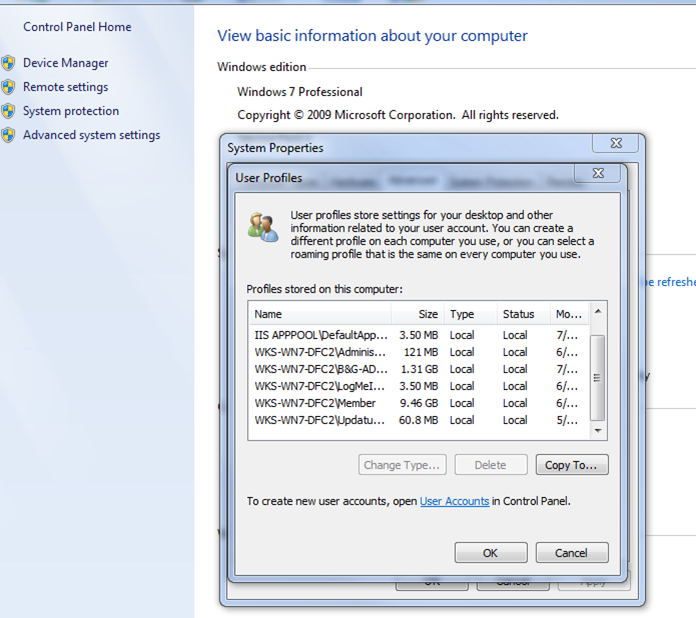
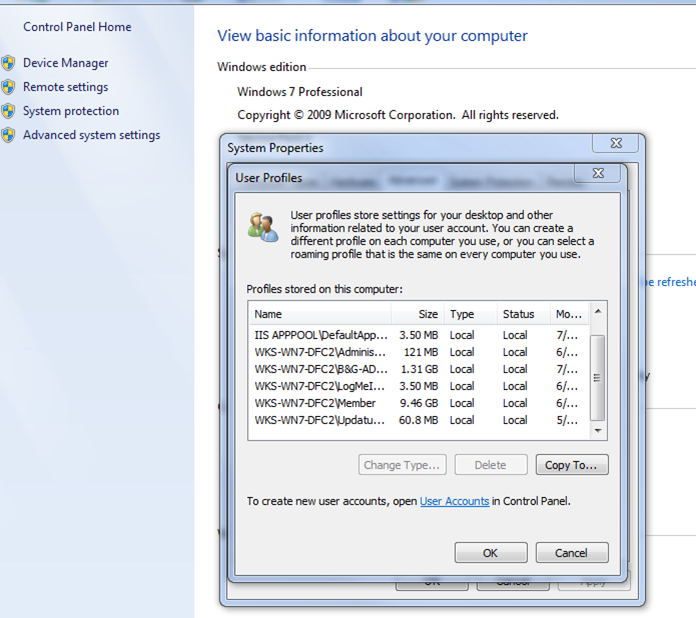
Here is where I go to take care of any residual leftovers:
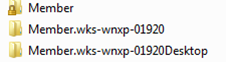
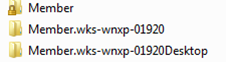
I would like to get rid of the unwanted accounts that put periods after the account and stay there. I can enumerate all of the users on all my machines using primal scripts and I can tell you this condition exist on most of my machines, so when I am coding, I have to do a case statement to take into consideration:
I don't want to have to go into safemode to delete the folders, but I am willing to do a reboot if there is some process or software that will delete those folders and any subfolders along with the files.
Your help is appreciated.
this is probably going to be an easy one, but is there a simply way to get ride of user account left over folders when I delete them. Let me explain with visuals, because a picture is worth a thousand words. Here is my scenario:
Here is a hypothetical member user list:
Here is where I go to delete accounts:
Here is where I go to take care of any residual leftovers:
I would like to get rid of the unwanted accounts that put periods after the account and stay there. I can enumerate all of the users on all my machines using primal scripts and I can tell you this condition exist on most of my machines, so when I am coding, I have to do a case statement to take into consideration:
I don't want to have to go into safemode to delete the folders, but I am willing to do a reboot if there is some process or software that will delete those folders and any subfolders along with the files.
Your help is appreciated.
ASKER
Did that. doesn't work that way. Residual folders still exist.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Okay, I'll grant that you are correct in that the profile should be deleted first. That is my problem, but still doesn't answer the original question, how do I get rid of the residual folders? I have gone as far as to take owner ship of the folders, log into the administrators account and still cant delete all of the folders with the deleted account. That's the golden nugget answer I am looking for. Now that you've proven that I have been deleting my accounts the wrong way, how do I get rid of the folders?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
That's the golden nugget I was looking for
Thank you much. : )
Having a Live distro around, does come in handy every once in a while. ; )
Having a Live distro around, does come in handy every once in a while. ; )
You will have to restart the computer and log into the adminstrator account or an account with admin rights in order to get the delete button for each of the profiles.