Graycon
asked on
Double NAT/Twice NAT VPN Setup
Please help with configuration of a Double NAT VPN
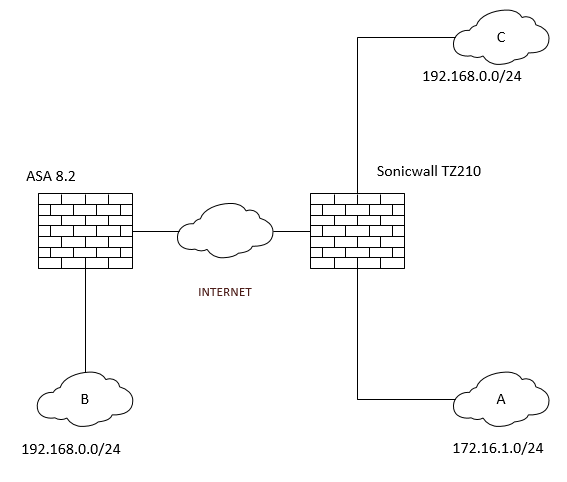
Client A has a Site to Site VPN to Client B
Client A will soon have a Vlan in it's network to Client C
Client A and C have the same Subnet, and changing them is non optional. (192.168.0.0/24)
I need to reconfigure the VPN so that there is no longer a conflict.
Client A will send traffic to new remote network 10.255.255.0/24
Client B will NAT traffic from 10.255.255.0/24 to 192.168.0.0/24 and Vica-versa on it's way back to Client A
Client B is running Cisco ASA 8.2
Client A is running a Sonicwall TZ210 (or similar)
I need assistance with configurations for the Cisco ASA... I speculate the Sonicwall will just update the remote network details for IPSec.
Client A has a Site to Site VPN to Client B
Client A will soon have a Vlan in it's network to Client C
Client A and C have the same Subnet, and changing them is non optional. (192.168.0.0/24)
I need to reconfigure the VPN so that there is no longer a conflict.
Client A will send traffic to new remote network 10.255.255.0/24
Client B will NAT traffic from 10.255.255.0/24 to 192.168.0.0/24 and Vica-versa on it's way back to Client A
Client B is running Cisco ASA 8.2
Client A is running a Sonicwall TZ210 (or similar)
I need assistance with configurations for the Cisco ASA... I speculate the Sonicwall will just update the remote network details for IPSec.
When connecting two internal networks on the same subnet via a VPN, perform NAT through the VPN tunnel so that the conversation between the two networks is: public network to private network.
The SonicWall just needs to NAT 10.255.255.0/24 to 192.168.0.0/24, forcing to the VPN tunnel. The answers come back from 192.168.0.0/24, and are translated to 10.255.255.0/24 again if arriving via the tunnel.
Packets from/to 192.168.0.0 on A/C network will not get translated.
That way, nothing has to be done on the ASA side, only SonicWall needs to perform destination NAT.
Packets from/to 192.168.0.0 on A/C network will not get translated.
That way, nothing has to be done on the ASA side, only SonicWall needs to perform destination NAT.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Any update on this?
please have a look on this recent (ongoing) thread:
https://www.experts-exchange.com/questions/28253197/Dual-physical-firewall-design.html?anchorAnswerId=39554501#a39554501
Exactly the same. The consensus so far is not to use the quite complicated dual FW setup any more but one next gen firewall.
But your question is answerd here:
https://www.experts-exchange.com/questions/28253197/Dual-physical-firewall-design.html?anchorAnswerId=39535804#a39535804