How to update a checkbox on exit
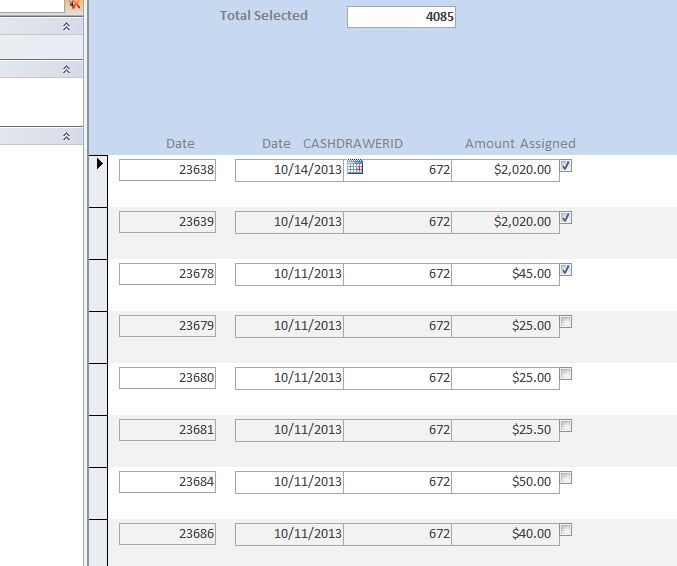
I have a form that I have attached here that we will call Form1. On this form I can check the assigned checkbox or uncheck it. I also have a second form that is open that I call Form2
I need to add an action that does the following
onExit
if Forms!Form2!txtField1 is null
unselect all the "Assigned" checkboxes on Form1
Else
Just leave the checkboxes I have selected checked as they are
I'm a bit rusty on VBA. Much appreciated
This is Form1
I need to add an action that does the following
onExit
if Forms!Form2!txtField1 is null
unselect all the "Assigned" checkboxes on Form1
Else
Just leave the checkboxes I have selected checked as they are
I'm a bit rusty on VBA. Much appreciated
This is Form1
ASKER
Hi Capricorn,
Thanks for your help.
one tiny problem.
lets say I have checked
record1
record2
record 3
when I try to close the form, if I have selected record2 for example it will uncheck everything starting at record2, so the record 1 will still be selected and assiged.
is there a way I can add some code to start at the begining of the form and not at the record I have selected?
thanks again, this has beeen very helpful
Thanks for your help.
one tiny problem.
lets say I have checked
record1
record2
record 3
when I try to close the form, if I have selected record2 for example it will uncheck everything starting at record2, so the record 1 will still be selected and assiged.
is there a way I can add some code to start at the begining of the form and not at the record I have selected?
thanks again, this has beeen very helpful
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
thanks,
as always amazing work
as always amazing work
private sub form_Unload(cancel as Integer)
on error resume next
If IsNull(Me.txtField1) then
with forms!form1.Recordset
do until .EOF
.edit
!Assigned = 0
.update
.moveNext
loop
end with
end If
end sub