Dominator1025
asked on
Can you dynamically program a windows task scheduler?
My workgroup has a series of Access macros/reports that run each day with the help of windows task scheduler. Most of the files being imported each day maintain the same name.
Is there a way to program the scheduler to run when the Date Modified property is updated?
Is there a way to program the scheduler to run when the Date Modified property is updated?
Is there a way to program the scheduler to run when the Date Modified property is updated
Not per se.
The scheduler runs on a time basis, period.
Now, a VBScript that checks the files you have in mind, checks to see if Access is open, and if the files have changed and Access is not running, fires up Access to do the rest could be written. It then can be scheduled to run very frequently.
But the task scheduler itself, that gets set off strictly by a time event.
Create a VB script that that checks if files have been modified. In the script, if a modified file is detected, then launch the task scheduler. This can be done with the SCHTASKS command. Something like SCHTASKS /Run /TN <my scheduled tasks>.
I hope this helps,
0doc
I hope this helps,
0doc
@Nick67
> The scheduler runs on a time basis, period.
That's wrong. Starting with windows xp we could trigger tasks on event creation. With Vista/7/8/8.1 this is even GUI driven possible (with xp there was eventtriggers.exe).
That said: you could setup ntfs auditing on that file. Whenever it gets changed, an event would get created in the security event log and that event can be attached to your task.
> The scheduler runs on a time basis, period.
That's wrong. Starting with windows xp we could trigger tasks on event creation. With Vista/7/8/8.1 this is even GUI driven possible (with xp there was eventtriggers.exe).
That said: you could setup ntfs auditing on that file. Whenever it gets changed, an event would get created in the security event log and that event can be attached to your task.
Hi,
Back to my original comments - use the task scheduler to run the test process at an interval, say hourly, and execute if file date is updated. Process can be any scripting language.
Regards,
Bill
Back to my original comments - use the task scheduler to run the test process at an interval, say hourly, and execute if file date is updated. Process can be any scripting language.
Regards,
Bill
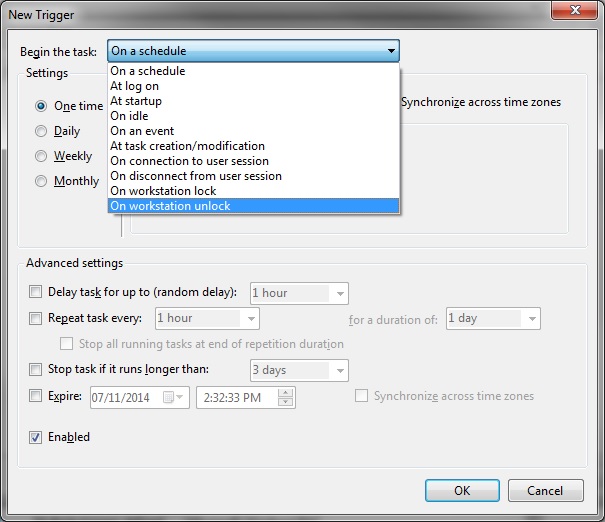
Neat enough. Here are the full list of things that can set off a task in Win 7.
Perhaps the only fly in the ointment of doing it through auditing and the event log is that the Access process may also trip the auditing and set off the task again. But then, that depends very much upon other options (don't run this task if it is already running) and what code you make the task do.
But @McKnife, you were right, time isn't the only trigger by a long shot.
Thanks,
Nick67
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
I would write a DOS batch file that checks the file date and runs access /macros if the file date is changed. It will take some research but you can use an if statement.
Run the batch file each hour or whatever using the event scheduler.
Regards,
Bill