aasikolo
asked on
WiFi as WAN
I am trying to set up what I'm told is a WiFi as WAN. I have a Sierra Wireless Overdrive Pro Mobile Hot spot and I need a couple of Ethernet ports, which the hot spot does not have.
I bought a cradlepoint MBr95 wireless router, Their website does not list my hot spot as a supported product, but the vendor, who has been trying to troubleshoot the situation tells me that any wireless router would do the trick.
We've gone through the wireless as wan set up on the router. To test, once the WiFi antenna on my laptop is turned off and connected to the router using Ethernet cable we still cannot access the internet through hte Ethernet connections on the router,
Any suggestions are welcome to get the ethernet ports working. It is important to note that I do not know what I am doing.
P.S. The router and modem do not have conflicting IP addressed any more, The router was assigned a new address.
I bought a cradlepoint MBr95 wireless router, Their website does not list my hot spot as a supported product, but the vendor, who has been trying to troubleshoot the situation tells me that any wireless router would do the trick.
We've gone through the wireless as wan set up on the router. To test, once the WiFi antenna on my laptop is turned off and connected to the router using Ethernet cable we still cannot access the internet through hte Ethernet connections on the router,
Any suggestions are welcome to get the ethernet ports working. It is important to note that I do not know what I am doing.
P.S. The router and modem do not have conflicting IP addressed any more, The router was assigned a new address.
ASKER
Connection states oscillate between 'connecting' and 'available.' Doesn't stop.
Connected to LAN port 1,2,3, and/or 4
IP address of Sierra Wireless is 192.168.0.1
IP address of MBR95 is 192.168.1.1
I have no idea what the rest of those addresses you mentioned are or where to find out what they are.
Connected to LAN port 1,2,3, and/or 4
IP address of Sierra Wireless is 192.168.0.1
IP address of MBR95 is 192.168.1.1
I have no idea what the rest of those addresses you mentioned are or where to find out what they are.
> Connection states oscillate between 'connecting' and 'available.' Doesn't stop.
That's the problem.
It needs to say "Connected" or you can't use the MBR95 as a bridge.
Did you enter the Profile manually or import it from Site Survey?
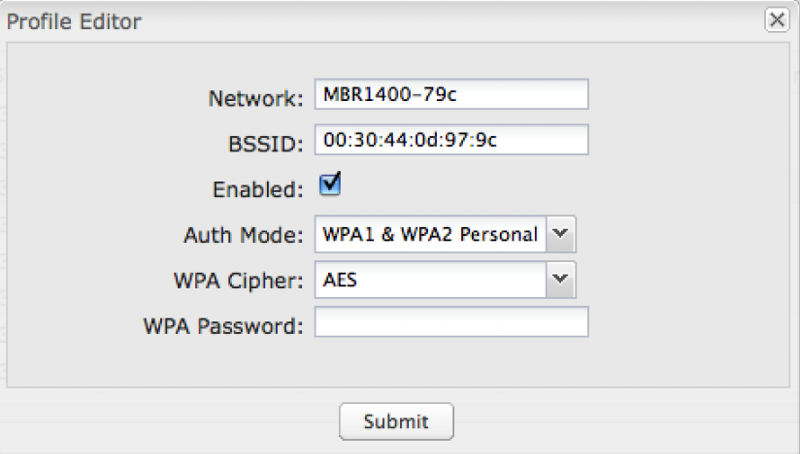
What is Auth Mode, and Cipher set to in the Profile Editor?
Can you temporarily disable security on the Sierra (also 'None' in the CradlePoint's Profile Editor), and connect OK then?
I recommended using ports 1, 2 or 3 because some CradlePoints have port 4 set as a second WAN port by default. That doesn't appear to be the case with the MBR1400/MBR95... but when you get it working correctly you might want to set the blue WAN port to be a LAN port instead, which would give you 5 ethernet ports instead of 4.
ASKER
Imported from the site survey.
The only thing I've entered is the password, which it accepts.
Auth Mode and Cipher are set to whatever the default was.
I haven't tried disabling security. Will give that a try.
The only thing I've entered is the password, which it accepts.
Auth Mode and Cipher are set to whatever the default was.
I haven't tried disabling security. Will give that a try.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I caved and took it down to the sprint store, and the tech figured it out. Unfortunately he didn't share what he did.
Thanks for your time
Thanks for your time
When you look on the Status tab of the MBR95's setup screens, in the sub-category Internet Connections, what does it say for Connection State?
Connected to the router "where" exactly?
(Try it connected to LAN port 1, 2 or 3.)
What is the LAN address of the Sierra, its DHCP range/scope, the WAN IP of the MBR95 and the LAN IP of the MBR95?