AXISHK
asked on
VM Converter
After converting a VM, I have encountered the following message :
"Editing virtual machine settings fails with the error: You cannot use the vSphere client to edit the settings of virtual machines of version 10 or higher"
1. Is there a vCentre appliance that can be setup easily ? I'm using VMware 5.5 Essential Kit ?
2. How to install the powershell ?
In fact, I use old version 4.3 to convert Window 2003 server but it pop out for any error. Something likes the IDE can't support, Flap option. Searching the web and it recommend to use later version of converter. Actually, which version should I use ?
Tks
http://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2061336
"Editing virtual machine settings fails with the error: You cannot use the vSphere client to edit the settings of virtual machines of version 10 or higher"
1. Is there a vCentre appliance that can be setup easily ? I'm using VMware 5.5 Essential Kit ?
2. How to install the powershell ?
In fact, I use old version 4.3 to convert Window 2003 server but it pop out for any error. Something likes the IDE can't support, Flap option. Searching the web and it recommend to use later version of converter. Actually, which version should I use ?
Tks
http://kb.vmware.com/selfservice/microsites/search.do?language=en_US&cmd=displayKC&externalId=2061336
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
If your Hypervizor is 5.x I would use 5.5. What are the errors? When you convert it with 5.5 you should have an option for the hardware version. Try selecting 7 or 9
You have created a version 10 virtual machine, and virtual machine version 10 and above CAN NOW ONLY be edited with the VMware vSphere Web Client.
NOT the vSphere Client.
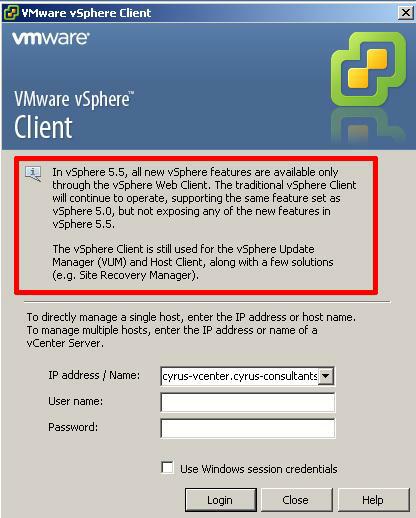
If you are using VMware vSphere 5.5, you should be now using the Web Client to access vCenter Server, because you cannot complete all management now with the old vSphere Client, all new features are not available to the vSphere Client after 5.0. You will see this error warning, when you logon to using the client.
As for conversion of Windows 2003, I seem to recall support for this was removed from Converter 5.5, Converter 5.5 only supported Windows 2003 R2, so it depends which version fo Windows 2003 you have.
HOW TO: P2V, V2V for FREE - VMware vCenter Converter Standalone 5.5
HOW TO: Synchronize changes when completing a P2V or V2V with VMware vCenter Converter Standalone 5.1
HOW TO: Improve the transfer rate of a Physical to Virtual (P2V), Virtual to Virtual Conversion (V2V) using VMware vCenter Converter Standalone 5.0
NOT the vSphere Client.
If you are using VMware vSphere 5.5, you should be now using the Web Client to access vCenter Server, because you cannot complete all management now with the old vSphere Client, all new features are not available to the vSphere Client after 5.0. You will see this error warning, when you logon to using the client.
As for conversion of Windows 2003, I seem to recall support for this was removed from Converter 5.5, Converter 5.5 only supported Windows 2003 R2, so it depends which version fo Windows 2003 you have.
HOW TO: P2V, V2V for FREE - VMware vCenter Converter Standalone 5.5
HOW TO: Synchronize changes when completing a P2V or V2V with VMware vCenter Converter Standalone 5.1
HOW TO: Improve the transfer rate of a Physical to Virtual (P2V), Virtual to Virtual Conversion (V2V) using VMware vCenter Converter Standalone 5.0
ASKER
Those servers are Window 2003R2...
For VMware vSphere Web Client. does it mean I need to configure vCenter and access through it ?
Do I still need a individual management IP address for each VMware host ?
Tks
For VMware vSphere Web Client. does it mean I need to configure vCenter and access through it ?
Do I still need a individual management IP address for each VMware host ?
Tks
ASKER
Install the vCenter and access the vSphere Web client on it. However, it fails
Failed to connect to VMware Lookup Service
https://10.0.23.100:7444/lookupservice/sdk - SSL certificate verification failed. In fact, during the setup, I see the error. Any idea ?
BTW, I have also changed the IP address (as it was assigned with DHCP by default). Will that also be the problem ?
Tks
vCenter.png
Failed to connect to VMware Lookup Service
https://10.0.23.100:7444/lookupservice/sdk - SSL certificate verification failed. In fact, during the setup, I see the error. Any idea ?
BTW, I have also changed the IP address (as it was assigned with DHCP by default). Will that also be the problem ?
Tks
vCenter.png
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Tks
ASKER
Tks