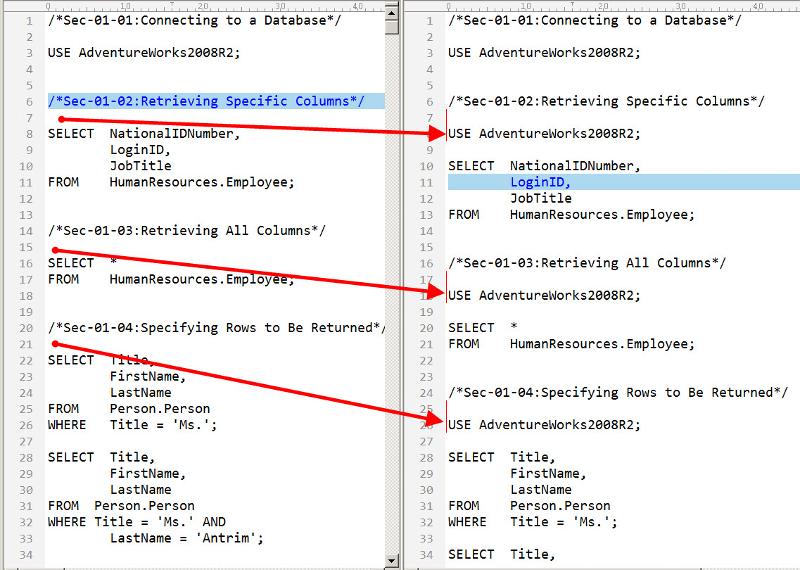
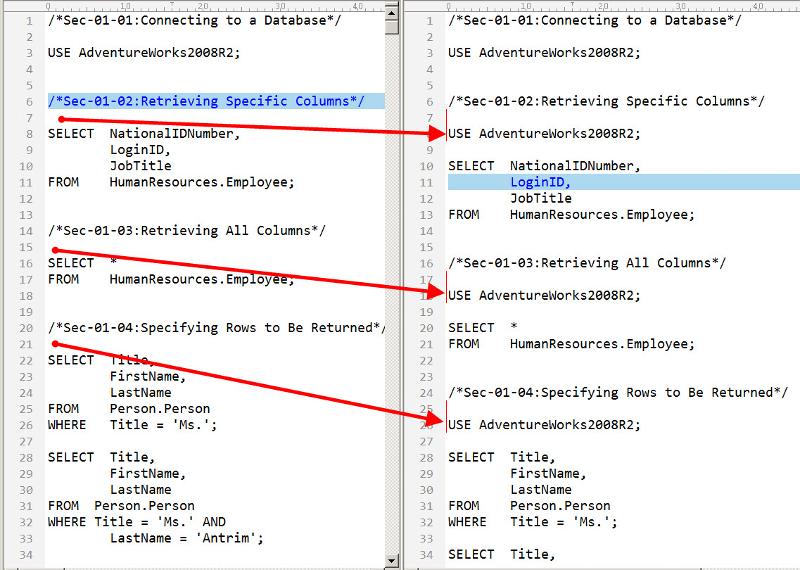
Need USE's found and added in following text
In the attached file, each section needs a USE statement that is picked up from the previous section. It will change through the different sections.
Original on Left, Desired on Right
 sqlrecipes-original.txt
sqlrecipes-original.txt
Original on Left, Desired on Right
 sqlrecipes-original.txt
sqlrecipes-original.txt
ASKER
Thanks
Adventureworks2008r2 is just one of them.
Most of the sections are Adventureworks2012, but there are several others.
Adventureworks2008r2 is just one of them.
Most of the sections are Adventureworks2012, but there are several others.
OK, I don't see in your example file where the "USE" statement is picked up from, so I guess you have somewhere a list and will modify the regex either programatically inside a loop or by hand (30 sections is not that much - probably faster by hand than writing the code)
ASKER
There actually 380 sections.
Whenever you see the word 'use' a new database is being used. It can change several times within a section.
There are 30 chapters. The first number is the chapter, the second number is the exercise within the chapter.
Whenever you see the word 'use' a new database is being used. It can change several times within a section.
There are 30 chapters. The first number is the chapter, the second number is the exercise within the chapter.
Not very familiar with PERL, so here how to do it in Powershell:
$originalName="\path\to\or
$copyName="\path\to\copy\f
$use = ""
echo "" > $copyName #empty copy file
foreach ($line in get-content $originalName) {
echo $line >> $copyName
if ($regex = $line -match "\/\*Sec.*?\/") {echo `n`n$use`n >> $copyName}
elseif ($regex = $line -match "^USE.*?;") {$use = $line}
}
It will do a line by line search of $originalName and copy the result to $copyName
- update $use for every line with "USE" at the beginning
- append $use to every line that has a section in it
- send every other line unchanged
HTH,
Dan
$originalName="\path\to\or
$copyName="\path\to\copy\f
$use = ""
echo "" > $copyName #empty copy file
foreach ($line in get-content $originalName) {
echo $line >> $copyName
if ($regex = $line -match "\/\*Sec.*?\/") {echo `n`n$use`n >> $copyName}
elseif ($regex = $line -match "^USE.*?;") {$use = $line}
}
It will do a line by line search of $originalName and copy the result to $copyName
- update $use for every line with "USE" at the beginning
- append $use to every line that has a section in it
- send every other line unchanged
HTH,
Dan
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
OK, so you chose to ignore a working solution (tested on your sample text) and created your own.
Whatever works for you, I guess.
Whatever works for you, I guess.
ASKER
"OK, so you chose to ignore a working solution (tested on your sample text) and created your own.
Whatever works for you, I guess. "
I was not able to use the solution in powershell at this time..
Whatever works for you, I guess. "
I was not able to use the solution in powershell at this time..
ASKER
In the instructions to delete my question, it didn't mention how to handle the points.
Not tested with PERL (I do not have it here) but it works using replace with regex in Notepad++.
It will use AdventureWorks2008R2 for all sections. If that was not the intending result, try
s/(\/\*Sec-01.*?\/)/$1\nUS
HTH,
Dan