wcgplc
asked on
Unable to untick use light version on Outlook Web App
Hello,
I am unable to untick 'use light version' on outlook web app. Does anyone know why this is?
I am unable to untick 'use light version' on outlook web app. Does anyone know why this is?
ASKER
The internet browser is Internet explorer version 11
In the exchange management console type
In there is a parameter called 'OWAPremiumEnabled' check to see if this is set to false or true
If this is false then use the following command
M@
get-CASMailbox <Mailboxname> | fl In there is a parameter called 'OWAPremiumEnabled' check to see if this is set to false or true
If this is false then use the following command
set-casmailbox <mailboxname> -OWAPremiumClientEnabled $trueM@
ASKER
I'm unsure where to type this, please advise???
What version of exchange are you using?
ASKER
We are using exchange 2010
Internet Explorer 11 has a problem with all versions of Exchange unless you have updated them in the last 48 hours.
Exchange 2010 requires SP3 with rollup 3 (released Monday)
Exchange 2013 requires CU3 (released Monday)
Exchange 2007 doesn't have a fix for it yet so you have to use compatibility mode.
http://support.microsoft.com/kb/2866064
Don't bother changing anything in Exchange, it will not help.
Simon.
Exchange 2010 requires SP3 with rollup 3 (released Monday)
Exchange 2013 requires CU3 (released Monday)
Exchange 2007 doesn't have a fix for it yet so you have to use compatibility mode.
http://support.microsoft.com/kb/2866064
Don't bother changing anything in Exchange, it will not help.
Simon.
You can type the command into the management shell by going to
Start > programs > Microsoft exchange server 2010 > Exchange management shell
Matt
Start > programs > Microsoft exchange server 2010 > Exchange management shell
Matt
ASKER
Thanks for the help!
ASKER
Hi guys im running the exchange 2010 sp3 rollout 3 tonight. Do exchange services have to be shut down before I run the installer?
The rollup will stop the services during the install.
Simon.
Simon.
ASKER
i just tried to rollout and got the following message. im attaching a screenshot now
ASKER
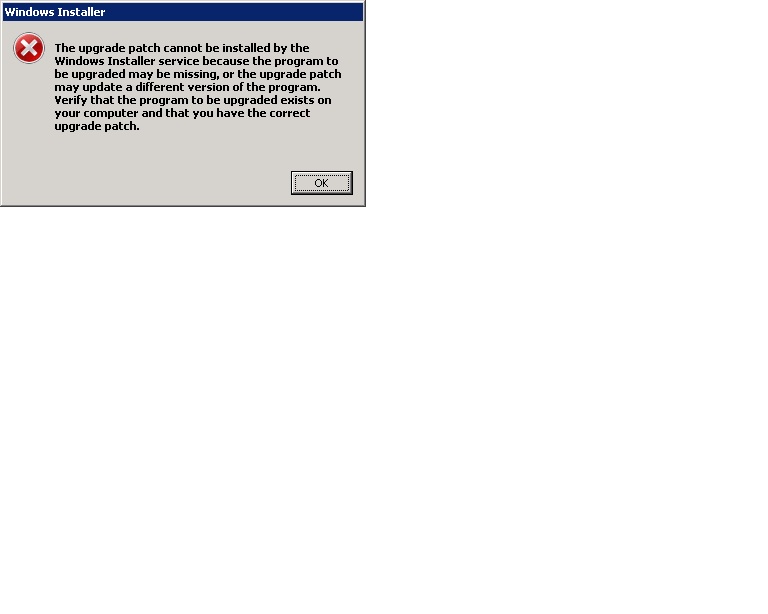
error message attached. it may be the service pack. how can i confirm which version i am on?
msexchange.jpg
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks for all the responses. Will be putting into practise. Thanks again.
M@
EDIT: See web page here with list of compatible browsers and the versions of OWA available
http://office.microsoft.com/en-gb/web-apps-help/supported-browsers-for-outlook-web-app-HA102824601.aspx