looking for my.ini that I am using in mysql workbench
I am using mysql workbench on my windows7 desktop
I have installed mysql many times on my computer because I have mysql, wamp and zend php framework
how can I find the my.ini that corresponds to the mysql workbench localhost I am using in the query window
I have installed mysql many times on my computer because I have mysql, wamp and zend php framework
how can I find the my.ini that corresponds to the mysql workbench localhost I am using in the query window
ASKER
I am asking if I could type a command in mysql workbench and run a query
Where my.ini
and query would return a file path
Where my.ini
and query would return a file path
No - that can't be done.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Note: I have wamp, xampp (uninstalled and deleted), php zend framework installed.
C:\xampp\ does not exist in windows explorer (even with show hidden files and folders).
Please do not just tell me to uninstall my entire computer so I can find the actual my.ini
using mysql workbench
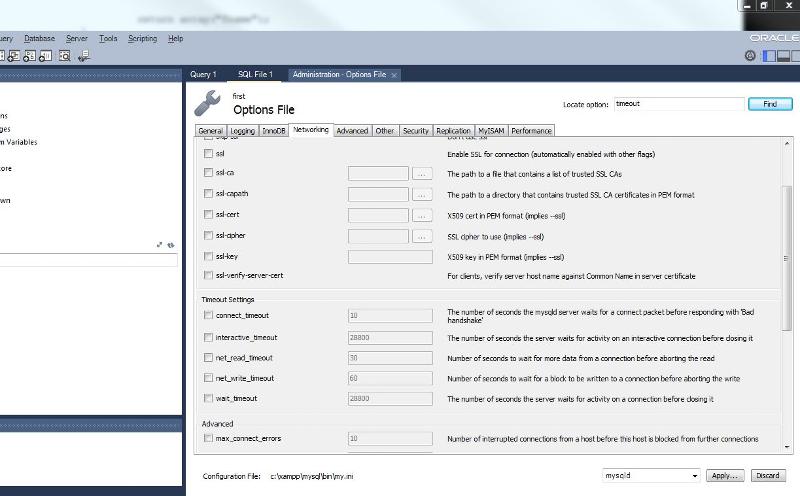
menu->server->options file
there are error dialog boxes that appear stating I am not using the correct my.ini file and a new one has to be created.
there are error dialog boxes that appear stating I am not using the correct mysqld file and a new one has to be created.
C:\xampp\ does not exist in windows explorer (even with show hidden files and folders).
Please do not just tell me to uninstall my entire computer so I can find the actual my.ini
using mysql workbench
menu->server->options file
there are error dialog boxes that appear stating I am not using the correct my.ini file and a new one has to be created.
there are error dialog boxes that appear stating I am not using the correct mysqld file and a new one has to be created.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks
So I think I will uninstall and reinstall -- when stuff starts going wrong.
Until then, mysql is running
And I should keep track of my own computer installations.
So I think I will uninstall and reinstall -- when stuff starts going wrong.
Until then, mysql is running
And I should keep track of my own computer installations.
It will depend on where you installed wamp. My copy is stored here:
C:\wamp\bin\mysql\mysql5.5
Yours may differ.