chima
asked on
Windows pop-up messages
Hello,
I keep getting the gray unofficial looking pop-up messages instructing me to update the apps I have installed, for example, firefox. I'm using Windows 7 on an Hewlett Packard laptop, these pop up messages might be generated by HP. None the less I wanted to ask you, before I feel safe clicking on it. The pop ups appear at the tool bar. I have my taskbar at the right side, therefore by toolbar is at the bottom and the pop up shows up at the bottom right of my screen.
It might be HP's "Action Center?" I stopped using their PC assistance after it messed up my system.
I am using an anti-virus software.
The image below shows the type of pop up I am getting;
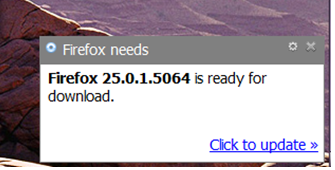
I keep getting the gray unofficial looking pop-up messages instructing me to update the apps I have installed, for example, firefox. I'm using Windows 7 on an Hewlett Packard laptop, these pop up messages might be generated by HP. None the less I wanted to ask you, before I feel safe clicking on it. The pop ups appear at the tool bar. I have my taskbar at the right side, therefore by toolbar is at the bottom and the pop up shows up at the bottom right of my screen.
It might be HP's "Action Center?" I stopped using their PC assistance after it messed up my system.
I am using an anti-virus software.
The image below shows the type of pop up I am getting;
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
chima--Glad to have helped.
ASKER