Access Relationships Where to find the join type
ASKER
Hi. Thanks. So where do I find the type of joins between tables
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
thanks for the help
Welcome!
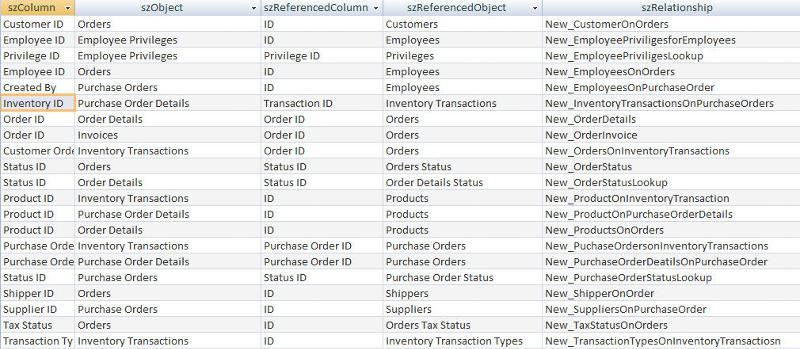
Let me explain.You have a reference table say categories containing 10 different category. You have an other table say products and and you want each table should belong to one of these categories. So you define a foreign key relation between these tables on the columns regarding to the category data...