ttorno
asked on
problem with user sharing contacts with co-workers
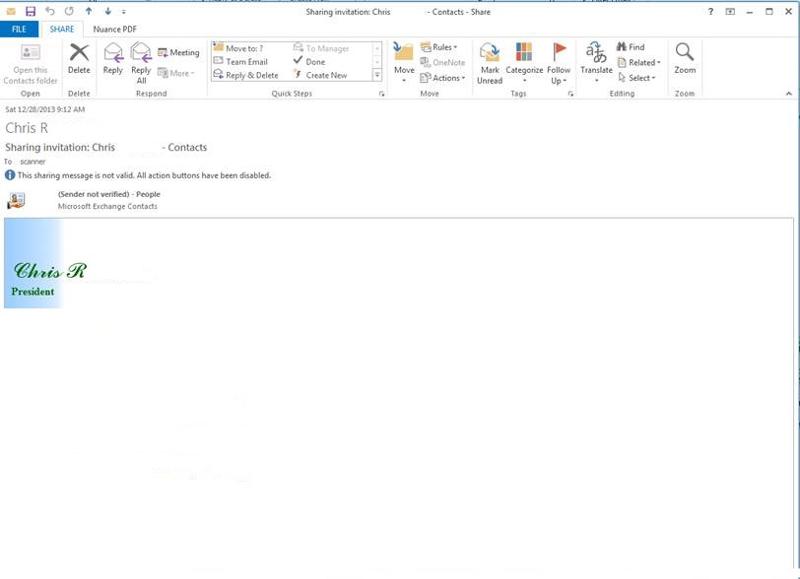
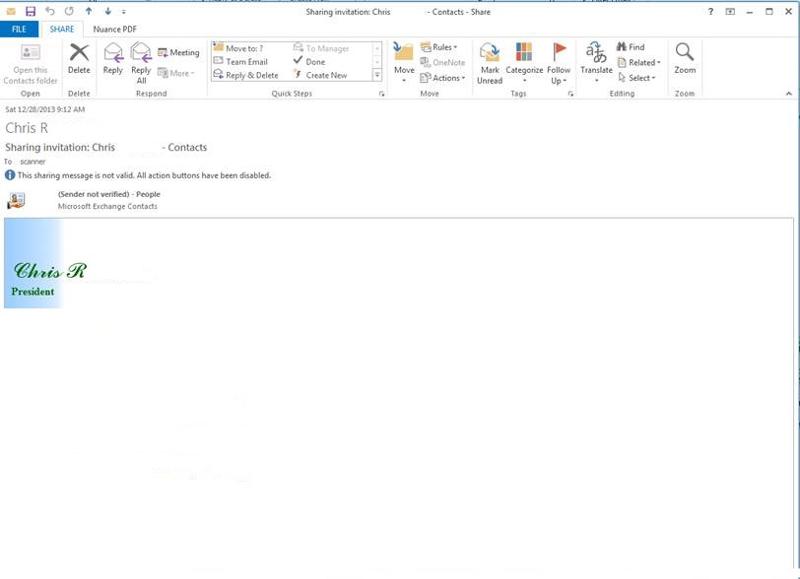
Customer is trying to share contacts with a co-worker. The Owner who is sharing out his contacts with a co-worker. The co-worker receives the email, but there is an error: Sender not verified)
The server is SBS-2008, with exchange 2007
Each user is using Office 2013.
The owner who shares out his contacts with certain people in the office, he is able to share it out to 3 people and not a fourth.
I was reading that it might be due to the fact the user is configured as a POP 3 account, but that is not the case all of the users are configured with exchange accounts. So that rules that out.
I have gone over the A/D accounts to make sure all of the fields are filled in and they are.
I am at a loss, at least this is not a crisis..
The server is SBS-2008, with exchange 2007
Each user is using Office 2013.
The owner who shares out his contacts with certain people in the office, he is able to share it out to 3 people and not a fourth.
I was reading that it might be due to the fact the user is configured as a POP 3 account, but that is not the case all of the users are configured with exchange accounts. So that rules that out.
I have gone over the A/D accounts to make sure all of the fields are filled in and they are.
I am at a loss, at least this is not a crisis..
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.