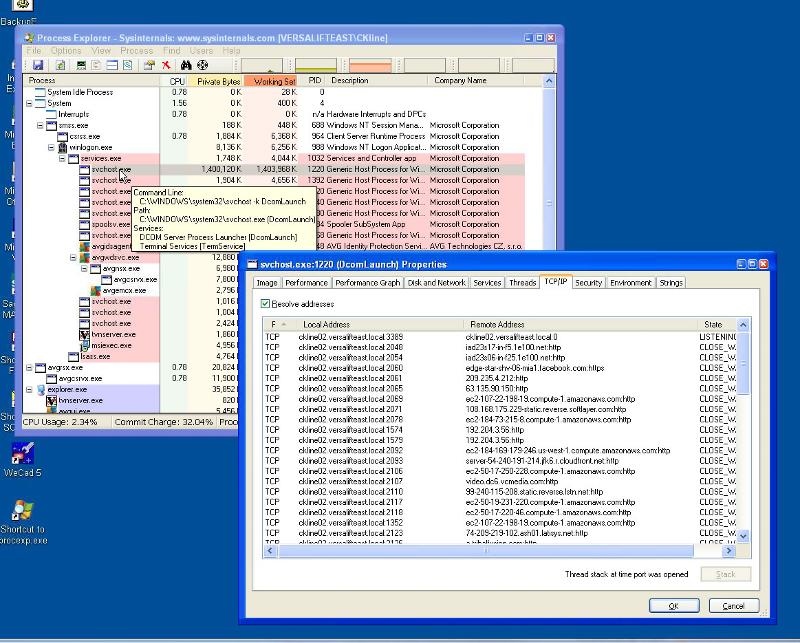
DcomLaunch using up ton of memory and TCP/IP connections
Issue with an employee's pc getting very slow and unresponsive after a while. Upon research I've found that the SVCHost process running the DCOM Launcher and TermServices is what is causing the issue. It will start out using 200,000K after reboot and as you can see with the screen print can really start to hog the memory. But what is more odd is all the TCPIP connections using all sorts of ports locally to HTTP ports. I've run AVG Scan and Malawarebytes but nothing is showing up as bad. Anyone have any ideas?? User is having to reboot every hour or so or his pc will just freeze up altogether. 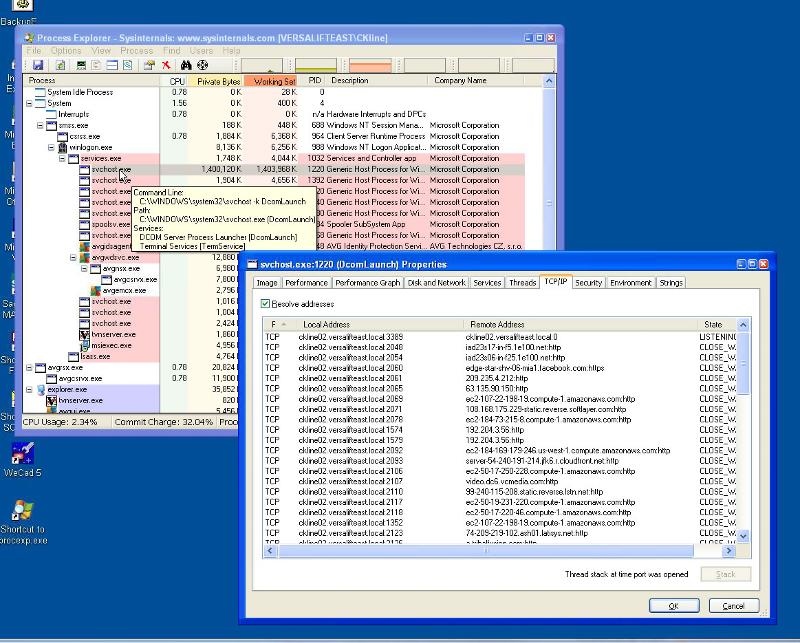
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Took 3 days to figure it out, but it is fixed.
In the System Configuration Utility dialog box, click Selective Startup on the General tab.
Click to clear the Load Startup Items check box.
Note The Use Original Boot.ini check box is unavailable.
Click the Services tab.
Click to select the Hide All Microsoft Services check box.
Click Disable All, and then click OK.
When you are prompted, click Restart.
Also do these to cleanup general corruption and repair/replace damaged/missing system files.
Run DiskCleanup - Start - All Programs - Accessories - System Tools - Disk Cleanup
Start - type this in Search Box -> COMMAND find at top and RIGHT CLICK - RUN AS ADMIN
Enter this at the prompt - sfc /scannow