missing dropbox.selekteditem.value in vb2008
ASKER
Sorry for low details.
I want to have the id and the Text.
What i found in www is...bind the combox to a list.
So i put my sqlreader into a list and set the list as datasource
and set .valuemember=id
and set .textmember = text
and i want ..after.selctedindexchange
I want to have the id and the Text.
What i found in www is...bind the combox to a list.
So i put my sqlreader into a list and set the list as datasource
and set .valuemember=id
and set .textmember = text
and i want ..after.selctedindexchange
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
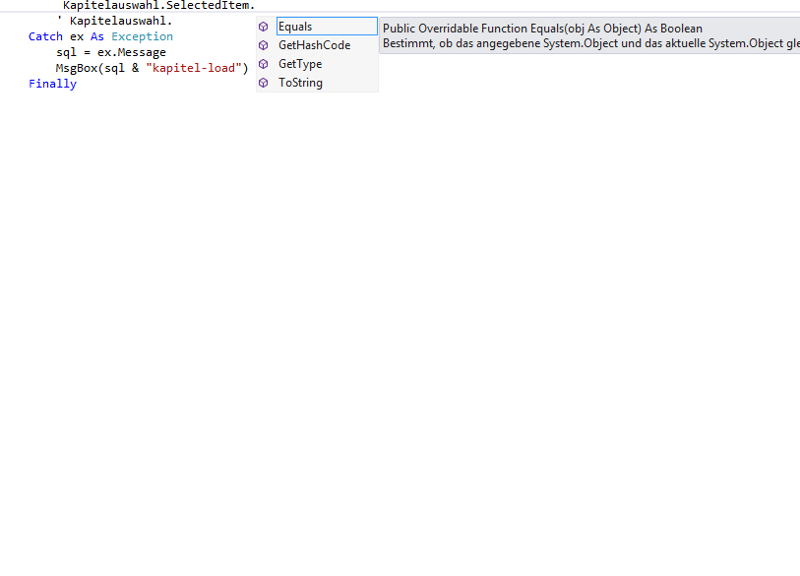
I know it can be confusing with all the properties a combobox has to access the selected item in the control.
I highly recommend that you read this blog entry on this topic.
I will copy it here in case the link changes or gets removed.