how to give access to website folders using ftp?
According with this question, now I have an ftp server from a CentOS distro, actually I have created a user but now I wonder how to associate that user with the folder in which should connect to:
https://www.experts-exchange.com/questions/28336243/How-to-set-up-a-static-IP-in-a-CentOS-Server-6-5.html
We pretend to install more than one website in the CentOS vps, and assign one or more ftp user(s) to each website folder.
Regards.
https://www.experts-exchange.com/questions/28336243/How-to-set-up-a-static-IP-in-a-CentOS-Server-6-5.html
We pretend to install more than one website in the CentOS vps, and assign one or more ftp user(s) to each website folder.
Regards.
Assuming you already created local user account, it will most likely in their respective home drive in /etc/passwd once they logged in via ftp. We won't know until you provide more information on the type of ftp software and configuration file.
ASKER
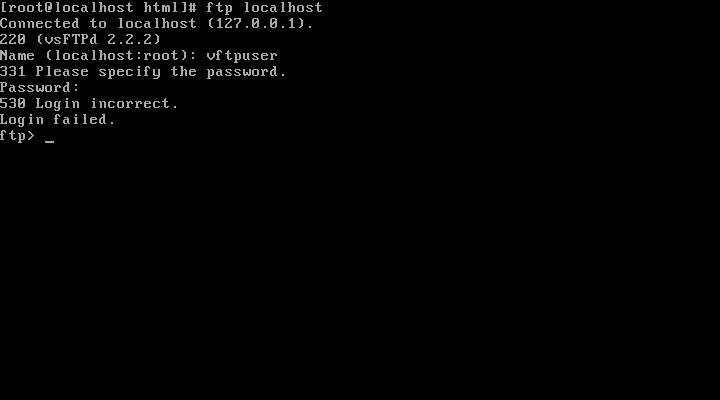
First of all, I have tried to get into FTP, but I couldn't never be connected, I tested the user and password directly on the server and everything is ok.
I have installed LAMP, so the idea is to get access to home folder of each website there.
I have installed LAMP, so the idea is to get access to home folder of each website there.
OK...
1. Create a local user having access to that directory
2. Configure VSFTPD with default parameters.
3. either disable SELinux or configure setsebool for ftp_home_dir and ftp_full_access
You users will be able to access web folders via ftp. in case issues you might need to allow few booleans of http... depends on version and distro you are using
Its SELinux which is playing around. :)
TY/SA
1. Create a local user having access to that directory
2. Configure VSFTPD with default parameters.
3. either disable SELinux or configure setsebool for ftp_home_dir and ftp_full_access
You users will be able to access web folders via ftp. in case issues you might need to allow few booleans of http... depends on version and distro you are using
Its SELinux which is playing around. :)
TY/SA
ASKER
After your post I did what is showed here: http://yohanes.pradono.com/2012/11/18/installing-vsftpd-with-virtual-users-enabled-and-using-pam_pwdfile-for-authentication
But I couldn't have success.
I have disabled SELinux and rebooted the server but I still got the message 530 Login incorrect.
Regards.
But I couldn't have success.
I have disabled SELinux and rebooted the server but I still got the message 530 Login incorrect.
Regards.
Are you trying with root ?
If yes,,, you need to remove entry of "root" user in below two files
1. /etc/vsftpd/ftpusers
2. /etc/vsftpd/users_list
If not please paste the screen output
TY/SA
If yes,,, you need to remove entry of "root" user in below two files
1. /etc/vsftpd/ftpusers
2. /etc/vsftpd/users_list
If not please paste the screen output
TY/SA
Add the "vftpuser" in the file /etc/vsftpd/user_list
And Try connecting...
And Try connecting...
Give me output of below
#sestatus
#setsebool -b | grep ftp
TY/SA
#sestatus
#setsebool -b | grep ftp
TY/SA
ASKER
NARANTHIRAN:
After adding vftpuser to user_list file I got the error "530 Permission Denied" (Actually the link from I followed the procedure of setting up vsftp says that adding the user will block it).
Sandeep_Agarwal_ :
#sestatus
SELinux status: disabled
#setsebool -b | grep ftp
setsebool: SELinux is disabled
After adding vftpuser to user_list file I got the error "530 Permission Denied" (Actually the link from I followed the procedure of setting up vsftp says that adding the user will block it).
Sandeep_Agarwal_ :
#sestatus
SELinux status: disabled
#setsebool -b | grep ftp
setsebool: SELinux is disabled
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Sandy:
Now its working, but the FTP redirects to the user local folder, in this case "/home/test/" folder, is there any way to make the ftp user points to specific virtual host, lets say /var/www/html/mywebsite1 or /var/www/html/mywebsite2 ?
Thanks in advance.
Now its working, but the FTP redirects to the user local folder, in this case "/home/test/" folder, is there any way to make the ftp user points to specific virtual host, lets say /var/www/html/mywebsite1 or /var/www/html/mywebsite2 ?
Thanks in advance.
Yes you can Point to the specific directory u want...
By editing the following file against the user and add the directory u want to point..
For example:
Username:x:502:503::/var/w
By editing the following file against the user and add the directory u want to point..
For example:
Username:x:502:503::/var/w
ASKER
Sorry, could you explain a little bit more how to perform that command and the file edition?
Thanks.
Thanks.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Correct... Use usermod
TY/SA
TY/SA