sjs
asked on
Bootable USB from an ISO
I am trying to create a bootable USB from a windows 8.1 ISO. doing it on a windows 2008 server.using, virtual CloneDrive, and through the cmd prompt run as an Administrator, with diskpart and xcopy commands. I am getting the message "The target does not support symbolic links".
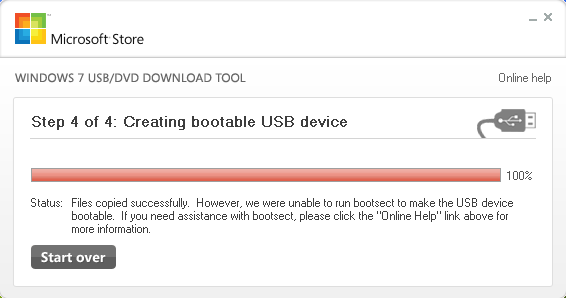
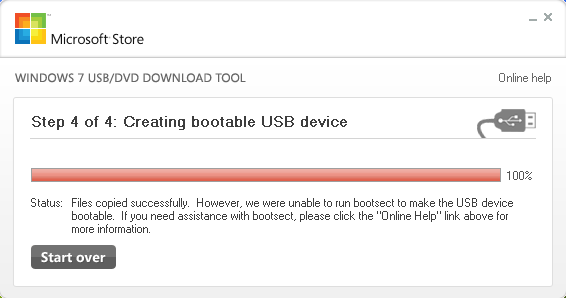
Also I have tried Microsoft's windows 7 ISO to usb utility and it did copy fine but at the end the message was could not create a boot partion.
Also I have tried Microsoft's windows 7 ISO to usb utility and it did copy fine but at the end the message was could not create a boot partion.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
can you read and write to that usb device?
if not, format it first
if not, format it first
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Both the Windows 7 USB/DVD download tool & ISO to USB worked fine. It was the ISO. I had downloaded again and it worked fine.
Thanks for your help
Thanks for your help
i have tried the given Windows 7 USB/DVD Download Tool, but for some reasons it prompts the following error messaging telling me the USB drive won't boot.
per my research on the error, i also tried BOOTSECT.EXE as mentioned in a Microsoft KB article. this file actually comes with in the 8.1 ISO, but i got the following error when running it on XP (as you know, 8 is not installed yet).
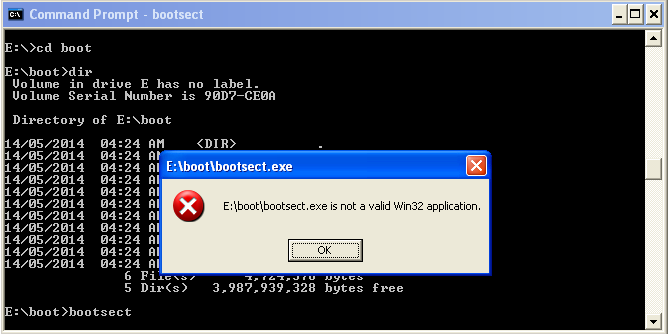
any comments please? thanks heaps.
per my research on the error, i also tried BOOTSECT.EXE as mentioned in a Microsoft KB article. this file actually comes with in the 8.1 ISO, but i got the following error when running it on XP (as you know, 8 is not installed yet).
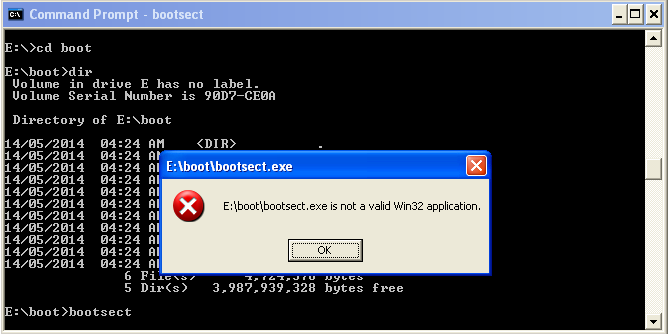
any comments please? thanks heaps.
try rufus, works easy http://rufus.akeo.ie/
ASKER
I did use the Windows 7 USB/DVD download tool and that's when i got the message that it copied fine but could not create a bootable USB.
comfortjeanius I have not tried many utilities but not the ISO to USB. I will download and try now.