Monitoring performance of a Vmware physical mode RDM Perfmon
We have an ESSbase server that is running within our Vmware virtual environment. Lately there have been some performance issues, the vendor seems to think that it could be tied to the storage on which the data lives.
From within windows on the guest OS running perfmon during slow performance we noticed that the counter for Disk Transfers/sec was averaging about 40 and sometimes as high as 200. From everything Ive seen online this points to a disk bottleneck.
This server has an RDM attached which is comprised of 4 15k sas drives in a RAID 10 configuration from our EMC VNX SAN so it should be performing better than this.
Im just looking for some advice on what I can monitor through vmware or windows that might provide some insight into the slowness.
Any help is appreciated.
From within windows on the guest OS running perfmon during slow performance we noticed that the counter for Disk Transfers/sec was averaging about 40 and sometimes as high as 200. From everything Ive seen online this points to a disk bottleneck.
This server has an RDM attached which is comprised of 4 15k sas drives in a RAID 10 configuration from our EMC VNX SAN so it should be performing better than this.
Im just looking for some advice on what I can monitor through vmware or windows that might provide some insight into the slowness.
Any help is appreciated.
ASKER
"4 x 15K SAS drives, in RAID 10, if you want more IOPS, you'll need to add more VMs."
Im guessing you meant disks here. That is something we are currently looking into but would take time.
"Is it read or write, which is causing the issues?"
I waiting on the DBA to be available to run tests to determine.
So would you reccomend monitoring this using perfmon tools or the performance metrics in Vcenter.
Im guessing you meant disks here. That is something we are currently looking into but would take time.
"Is it read or write, which is causing the issues?"
I waiting on the DBA to be available to run tests to determine.
So would you reccomend monitoring this using perfmon tools or the performance metrics in Vcenter.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
What is the latency?
The way to increase this is too add more spindles to the RAID 10 set.
Is the database running slowly?
It's not a poor database or application, with no indexes, a poor designed database will always be a poor slow VM.
Can you move the VM to a local disks and test?
The way to increase this is too add more spindles to the RAID 10 set.
Is the database running slowly?
It's not a poor database or application, with no indexes, a poor designed database will always be a poor slow VM.
Can you move the VM to a local disks and test?
ASKER
This is a Hyperion installation each update is taking approx A minute and a half to respond and be committed
Moving to a Nother DataStor on the VM might be a possibility but I won't be able to do that until I talk to the team responsible for managing this system
Adding more disks to that raid group is our last option since it will require a purchase of additional disk
Moving to a Nother DataStor on the VM might be a possibility but I won't be able to do that until I talk to the team responsible for managing this system
Adding more disks to that raid group is our last option since it will require a purchase of additional disk
Not to fast, we've been testing a new product from PernixData.
http://www.pernixdata.com/
If you've never heard of them, they are going to take the Storage/VMware world over!
We no longer need to add any more disks to our SANs to increase latency and IOPS!
Simple idea, an SSD/PCI-e flash card in the host, (not in the SAN) so closer to the CPU reduces even more latency, read and writes are cached in the SSD, and trickled back to the storage.
ALL storage is supported. No need to add more disks to your LUN/SAN!
It's BRILLIANT, highly recommended!
and you can select which VMs benefit, and therefore size your cache accordingly.
It's better than ALL the other versions!
oh, and the two co-founders are two guys which left VMware, the guy which designed the VMFS storage system, and another member from the Storage Team.
So there know a little about VMFS Storage!
Before adding more disks, I would look at this solution above, we've always been told by SAN vendors, add more spindles, add more spindles to increase IOPS and Latency, or purchase SSDs, or purchase Flash Cache Head.....
now it's changed.....enter PernixData.
PS I do not work for PernixData, I've just used and tested the product!
It's Excellent!
http://www.pernixdata.com/
If you've never heard of them, they are going to take the Storage/VMware world over!
We no longer need to add any more disks to our SANs to increase latency and IOPS!
Simple idea, an SSD/PCI-e flash card in the host, (not in the SAN) so closer to the CPU reduces even more latency, read and writes are cached in the SSD, and trickled back to the storage.
ALL storage is supported. No need to add more disks to your LUN/SAN!
It's BRILLIANT, highly recommended!
and you can select which VMs benefit, and therefore size your cache accordingly.
It's better than ALL the other versions!
oh, and the two co-founders are two guys which left VMware, the guy which designed the VMFS storage system, and another member from the Storage Team.
So there know a little about VMFS Storage!
Before adding more disks, I would look at this solution above, we've always been told by SAN vendors, add more spindles, add more spindles to increase IOPS and Latency, or purchase SSDs, or purchase Flash Cache Head.....
now it's changed.....enter PernixData.
PS I do not work for PernixData, I've just used and tested the product!
It's Excellent!
So you will need to look at performance metrics within the VM.
4 x 15K SAS drives, in RAID 10, if you want more IOPS, you'll need to add more VMs.
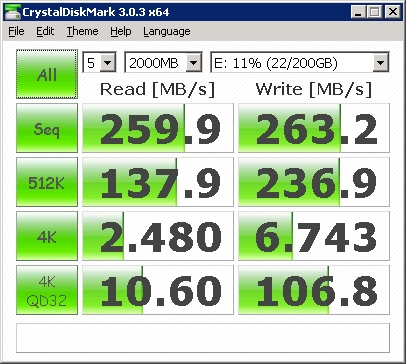
Is it read or write, which is causing the issues?
How many IOPS do you require?