sglee
asked on
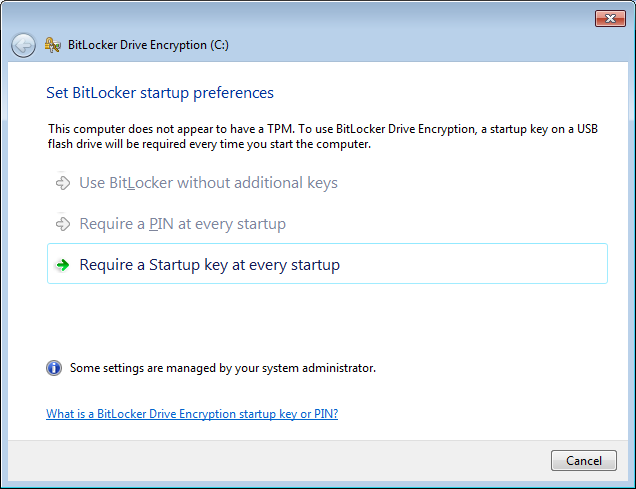
BitLocker without TPM
 Hi,
Hi, I have Win7 Ultimate laptop that does not have TPM. So I ran Gpedit.msc to do the following: Computer Configuration \ Administrative Templates \ Windows Components \ Bit Locker Drive Encryption \ Operating System Drives and double click on Require additional
authentication at startup.
Now when I turn on the Bit Locker on drive C, I get the message above with only one option "Require a Startup key at every startup".
Does this mean that the user has to stick a USB flash drive to his laptop EVERYTIME he turns it on?
Thanks.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
(1) So if the computer comes with TPM option in BIOS, then we don't need external USB?
(2) Say I create a USB and keep it plugged into the laptop all the time. I guess that is what we need to do. But then if someone takes that USB or say you lost it, then you can't turn on the computer?
(2) Say I create a USB and keep it plugged into the laptop all the time. I guess that is what we need to do. But then if someone takes that USB or say you lost it, then you can't turn on the computer?
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
@ZabagaR, @richrumble
Having gone thru the whole setup, I see the benefit of having built-in TPM because I won't need an external USB or having to type in 48 digit each time when you reboot the computer.
On the other hand, I can kind of see the benefit of not having TPM too, in case your OS is corrupted and you want to save the files and document out of that hard drive using another computer.
Well, I will just prepare to purchase small (1-4GB) USB flash drives for a number of PCs that I need to upgrade to Win 7 Ultimate. I thought about TruCrypt too, but I decided to go with MS solutions for wide range of support including paid support if necessary instead of depending on "free of charge forum".
Thanks for your help and I don't have further questions.
Having gone thru the whole setup, I see the benefit of having built-in TPM because I won't need an external USB or having to type in 48 digit each time when you reboot the computer.
On the other hand, I can kind of see the benefit of not having TPM too, in case your OS is corrupted and you want to save the files and document out of that hard drive using another computer.
Well, I will just prepare to purchase small (1-4GB) USB flash drives for a number of PCs that I need to upgrade to Win 7 Ultimate. I thought about TruCrypt too, but I decided to go with MS solutions for wide range of support including paid support if necessary instead of depending on "free of charge forum".
Thanks for your help and I don't have further questions.
BL main advantage is it's central management, if you need to roll out to a lot of people, that's where the benefit is. TC is what I recommend and have used for 10 years without issue. TPM is to thwart cold boot physical attacks and bootloader rootkits, which all seem like good ideas, but if your data doesn't justify that kind of effort you don't have to do it. The security provided by pgp//tc and others are good enough for personal use, BL is better for Corp.
-rich
-rich
I've used both as well. Bitlocker can take advantage of active directory if you're using it. I'm not sure what your config is but it seemed like a 1 off encrypted laptop, as opposed to a laptop on a domain in an enterprise.....what rich said above!!
Buy the smallest thumb drive and remember not to use that thumb drive for anything else.. whatever you do don't format that thumb drive after you have bitlocker enabled
ASKER
If That them drive is lost, but the computer and hard drive are unchanged, then can I recreate the keys and store them on the new thumb drive? If yes, does it generate new keys or the same keys?
See this article: http://technet.microsoft.com/en-us/library/dd875529%28v=ws.10%29.aspx
You can't recover unless you have a copy of those keys, one key only, but it can be backed up.
-rich
You can't recover unless you have a copy of those keys, one key only, but it can be backed up.
-rich
ASKER
There is no server system on this site, just individual several PCs.
You'll want to back up the keys that are on the flash drives yourself then.
-rich
-rich
ASKER
If the user lost original usb flash drive (where I saved the keys when I enabled BitLocker) and nothing has changed on the computer and the hard drive, can I save the keys again on another USB flash drive?
Yep: http://windows.microsoft.com/en-gb/windows7/what-is-a-bitlocker-recovery-key
To copy your BitLocker recovery key-rich
Open Bitlocker Drive Encryption by clicking the Start button Picture of the Start button, clicking Control Panel, clicking Security, and then clicking Bitlocker Drive Encryption.¿
Click Manage BitLocker, and then follow the instructions.
If the user lost original usb flash drive (where I saved the keys when I enabled BitLocker) and nothing has changed on the computer and the hard drive, can I save the keys again on another USB flash drive? Make as many copies of the recovery key as prudent.. If the machine is turned off and the usb key is lost then you have to enter the 25 character key.
Domain Joined machines the recovery key will be in Active Directory. If you have a Microsoft Account associated with this machine then it will be in your skydrive folder
http://windows.microsoft.com/en-CA/windows-8/bitlocker-recovery-keys-faq
Domain Joined machines the recovery key will be in Active Directory. If you have a Microsoft Account associated with this machine then it will be in your skydrive folder
http://windows.microsoft.com/en-CA/windows-8/bitlocker-recovery-keys-faq
It should be noted that the original question "Does this mean that the user has to stick a USB flash drive to his laptop EVERYTIME he turns it on?" should have been denied, because we have the option to setup a password from the command line (manage-bde -on c: -password). This is already possible with win7 but only on the command line while win8 has it in the GUI.
ASKER
@McKnife
Are you saying that the user don't have to have USB flash drive connected to the computer everytime the computer is turned on? In other words, we can store the password somewhere in the computer permanently; therefore I don't have to get a usb flash drive for each computer that I enable bitlocker?
Are you saying that the user don't have to have USB flash drive connected to the computer everytime the computer is turned on? In other words, we can store the password somewhere in the computer permanently; therefore I don't have to get a usb flash drive for each computer that I enable bitlocker?
No it cannot, as I linked before
http://windows.microsoft.com/en-us/windows-vista/bitlocker-drive-encryption-overview
-rich
http://windows.microsoft.com/en-us/windows-vista/bitlocker-drive-encryption-overview
BitLocker can also be used without a TPM. To use BitLocker on a computer without a TPM, you must change the default behavior of the BitLocker setup wizard by using Group Policy, or configure BitLocker by using a script. When BitLocker is used without a TPM, the required encryption keys are stored on a USB flash drive that must be presented to unlock the data stored on a volume.TC however can use a recovery disk or the 20+ character password the user has to remember. You can also purchase YubiKey Standards to remember the password for the user. http://www.yubico.com/applications/disk-encryption/disk-encryption-truecrypt/
-rich
ASKER
I see.
It is not a problem. If the USB flash drive is lost, then I would have a hard copy as well as my user. As long as we can turn on the computer with password/key, then I can re-create a new USB flash drive. Unfortunately they don't have "File Server".
It is not a problem. If the USB flash drive is lost, then I would have a hard copy as well as my user. As long as we can turn on the computer with password/key, then I can re-create a new USB flash drive. Unfortunately they don't have "File Server".
My remembrance has failed me. With win7 the -pw switch was present but invalid for the OS partition. This was indeed not possible before win8 came out. Sorry. It could only be used with non-OS partitionss.
ASKER