Check if DNS is installed in Ubuntu
I need a command to find out if DNS is installed on ubuntu.
I installed and uninstalled bind9 on ubuntu.., I run the following command before and after bind9 installed, I got the same output:
dpkg -s bind9
apt-cache search bind9
I wonder what is the right command to find out if bind9 is installed or not.
Thanks
I installed and uninstalled bind9 on ubuntu.., I run the following command before and after bind9 installed, I got the same output:
dpkg -s bind9
apt-cache search bind9
I wonder what is the right command to find out if bind9 is installed or not.
Thanks
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
ok 2 hyphens before get
ASKER
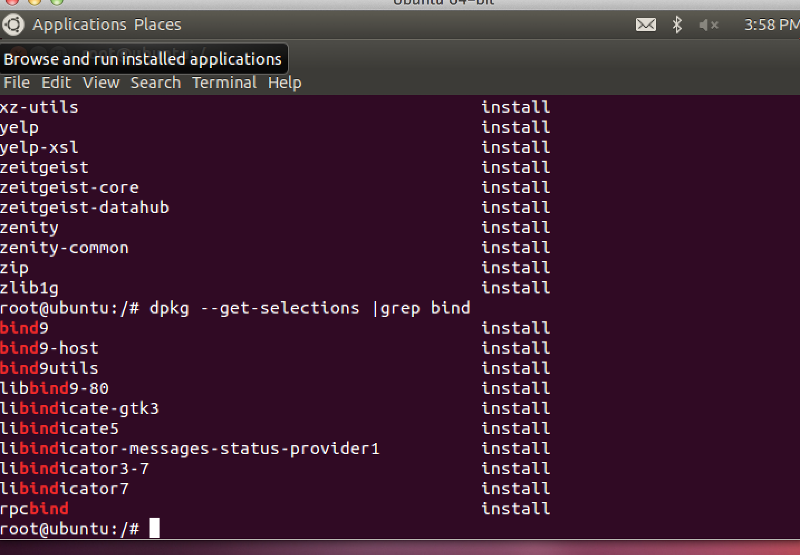
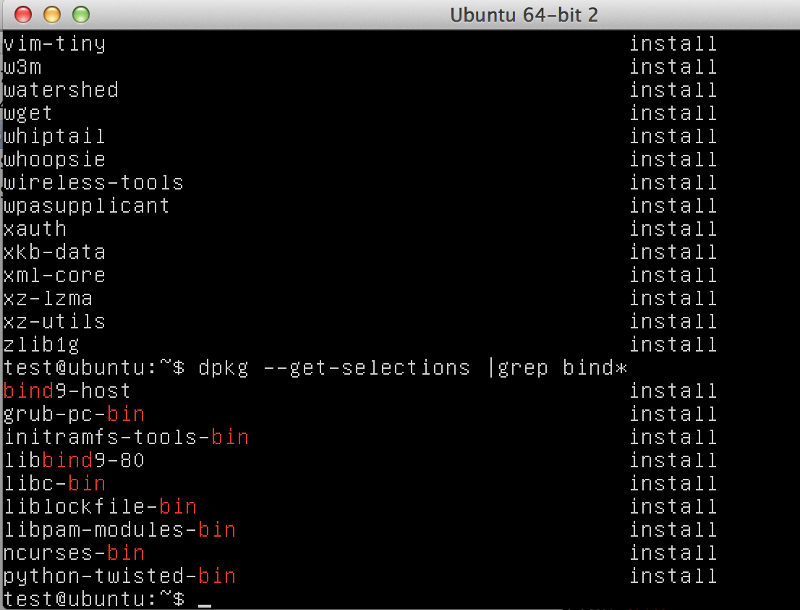
in which server is DNS installed , per the above snapshots ?
It is the rich text box, fame should go to one that typed a loooong hyyypheeen first ;)
you can see with
netstat -anpu
if anything on port 53
or in pstree try to find process called "named"
you can see with
netstat -anpu
if anything on port 53
or in pstree try to find process called "named"
Your picture has so huge font.
Please OCR and googel yourself. Really i cannot walk 5m from monitro to see your letters....
Please OCR and googel yourself. Really i cannot walk 5m from monitro to see your letters....
ASKER
the fonts look ok to me
ASKER
I guess the one that shows plain bind9 , is the one that DNS server installed on it
ASKER
dpkg --get-selections
Thank you Guys!
Thank you Guys!
ASKER