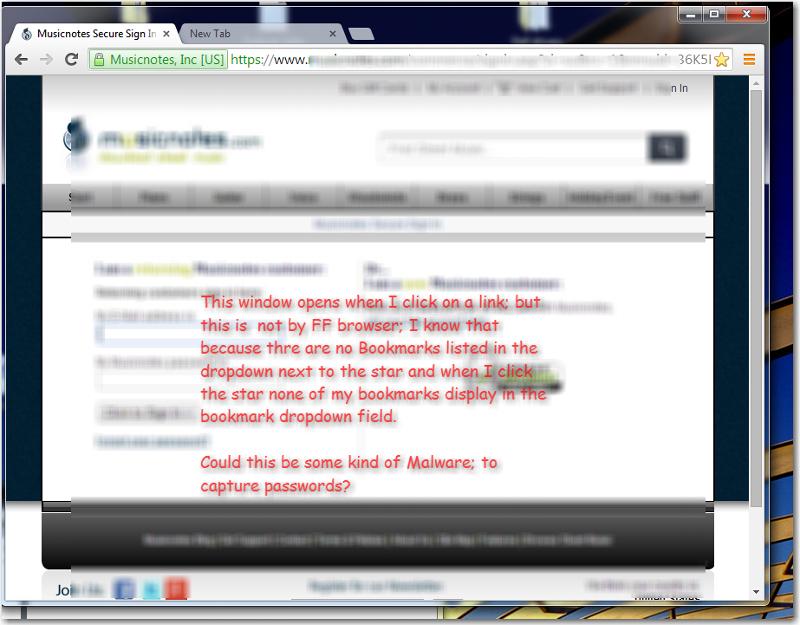
Bogus browser winder
I just noticed; this morning, when I clicked a URL a browser opened with the webpage of the URL; but I didn't recognize the browser. I didn't think too much of it at the time; I thought maybe an IE window had opened for some reason and since I'm not very familiar with the IE UI I wasn't sure. I went ahead and logged onto the site; and entered my username and password. When it happened again I got suspicious! So I closed the window and opened my browser the usual way; and pasted the URL directly.
Is there some kind of scam that redirects; when a URL is clicked on, to a bogus webpage that captures usernames and passwords?
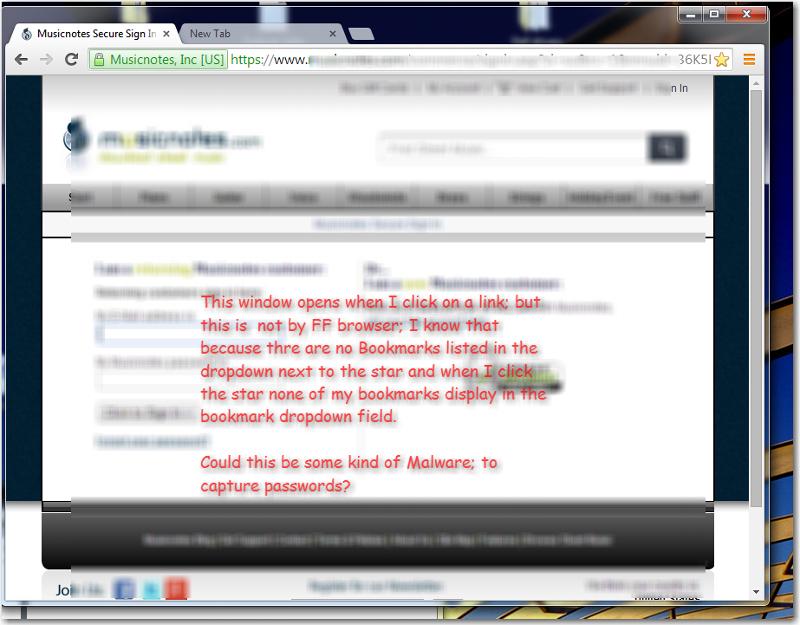
Is there some kind of scam that redirects; when a URL is clicked on, to a bogus webpage that captures usernames and passwords?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
It's very strange, but if I can't make it happen again I guess there's nothing else to do.