Exchange account not displaying any emails
I have a user that I had to rename. Since I made the change, I'm running into a problem.
I logged into OWA, and her account is empty, there's no emails in there.
I also configured the email account on a MAC, and there's no emails there either.
I'm puzzeled, because on my exchange server, under mailbox usage, it shows that the user is using 959mb out of 2 GB.
I was able to log in to OWA, so the account is ok, not locked, and the password worked, so why are there no emails in the account, but exchange is stating otherwise.
Any direction as to what is causing the problem, would be great.
Thanks.
I logged into OWA, and her account is empty, there's no emails in there.
I also configured the email account on a MAC, and there's no emails there either.
I'm puzzeled, because on my exchange server, under mailbox usage, it shows that the user is using 959mb out of 2 GB.
I was able to log in to OWA, so the account is ok, not locked, and the password worked, so why are there no emails in the account, but exchange is stating otherwise.
Any direction as to what is causing the problem, would be great.
Thanks.
What steps did you perform to rename the account?
ASKER
Using the AD Users and Computers plugin:
Did a right click on the name, and selected rename.
Then another box came up, changed the first name, alias, login and then hit save.
Then I checked Exchange and the correct email is listed as the main, or default email address in exchange, so that's correct in exchange.
I'm just baffled. I don't want to delete the account, as the user has about 1 GB used, according to exchange.
Did a right click on the name, and selected rename.
Then another box came up, changed the first name, alias, login and then hit save.
Then I checked Exchange and the correct email is listed as the main, or default email address in exchange, so that's correct in exchange.
I'm just baffled. I don't want to delete the account, as the user has about 1 GB used, according to exchange.
get-mailbox "email@address.com" | set-mailbox -Alias newSamAccountName
if that does not do it (which it probably won't but it keeps thing neat):
disconnect the user's mailbox
clean-mailboxdatabase database where user's mailbox is
re-connect the user's mailbox.
if that does not do it (which it probably won't but it keeps thing neat):
disconnect the user's mailbox
clean-mailboxdatabase database where user's mailbox is
re-connect the user's mailbox.
ASKER
How exactly do I disconnect the user's mailbox?
Then, the middle command, if my database is called db1, then the command would be:
clean-mailboxdatabase db1
Then how do I reconnect the mailbbox, as I I've never done that before?
Then, the middle command, if my database is called db1, then the command would be:
clean-mailboxdatabase db1
Then how do I reconnect the mailbbox, as I I've never done that before?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Im using exchange 2013, so from the recipients screen, I click on mailboxes and do a right click, but there is no right click. No menu pops up.
ASKER
looks like this command in exchange 2013 is gone:
"Get-mailboxDatabase | Clean-MailboxDatabase"
"Get-mailboxDatabase | Clean-MailboxDatabase"
ASKER
Now I have a bigger problem, I selected the 3 dots and now when I try to connect a mailbox, the screen is blank, it doesn't show me the mailbox I just disconnected.
How do I get it back?
How do I get it back?
ASKER
So what I did is, I clicked on a new mailbox and tied it to an existing user, so I got that back, but same old problem, no emails coming.
When I send an email from outlook, I get the email returned back to me with this error:
Undeliverable
Generating server: exchangeserver.domain.org
IMCEAEX-_o=domain_ou=Excha
Remote Server returned '550 5.1.1 RESOLVER.ADR.ExRecipNotFou
I already tried to delete the outlook cache, which I did, but it didn't do anything...
When I send an email from outlook, I get the email returned back to me with this error:
Undeliverable
Generating server: exchangeserver.domain.org
IMCEAEX-_o=domain_ou=Excha
Remote Server returned '550 5.1.1 RESOLVER.ADR.ExRecipNotFou
I already tried to delete the outlook cache, which I did, but it didn't do anything...
okay.. what you did there is made a new mailbox without data for an existing user.... that might complicate things a bit.
What do you get if you run this:
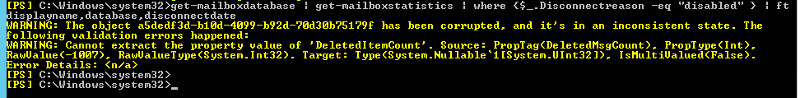
Get-MailboxDatabase | Get-MailboxStatistics | Where { $_.DisconnectReason -eq "Disabled" } | ft DisplayName,Database,Disco
What do you get if you run this:
Get-MailboxDatabase | Get-MailboxStatistics | Where { $_.DisconnectReason -eq "Disabled" } | ft DisplayName,Database,Disco
ASKER
what do you get from this:
get-Mailbox -Identity a5dedf3d-b10d-4099-b92d-70
Also, do you have another mailbox database?
get-Mailbox -Identity a5dedf3d-b10d-4099-b92d-70
Also, do you have another mailbox database?
ASKER
I have 2 databases, really just one, because the second it's only for testing, there's no data in it.
The real database is mailboxdb1
Here's the output, I just changed the domain name and the email address for privacy concerns:
mailboxIdentity.txt
The real database is mailboxdb1
Here's the output, I just changed the domain name and the email address for privacy concerns:
mailboxIdentity.txt
Hot diggity.
Try this - remove the empty mailbox you created for the user and reconnect the old one:
Connect-Mailbox -Identity "a5dedf3d-b10d-4099-b92d-7
Assuming that works, I'd like you to try moving the mailbox to your second database, but set a high tolerance for corrupted items. Should be on the second page of the local move request setup. Check "Skip the corrupted messages," checkbox and set the max number to 49 (50+ requires the -AcceptLargeDataLoss flag so you'd have to do it in powershell.)
This should move the mailbox to the second database and skip over any corrupt elements (they're gone anyway - the only place they live now is in backups) That should fix the warning you're seeing and will likely fix the display issue as well.
Try this - remove the empty mailbox you created for the user and reconnect the old one:
Connect-Mailbox -Identity "a5dedf3d-b10d-4099-b92d-7
Assuming that works, I'd like you to try moving the mailbox to your second database, but set a high tolerance for corrupted items. Should be on the second page of the local move request setup. Check "Skip the corrupted messages," checkbox and set the max number to 49 (50+ requires the -AcceptLargeDataLoss flag so you'd have to do it in powershell.)
This should move the mailbox to the second database and skip over any corrupt elements (they're gone anyway - the only place they live now is in backups) That should fix the warning you're seeing and will likely fix the display issue as well.
ASKER
I only have 1 database. The 2nd one is just a temp DB that is not being used.
Actually, can you tell me how to delete it properly, because it's not being used and no mailboxes should be in.
Actually, since the emloyee is new, she used to work for us a few years ago, she didn't say anything about her old emails, so I'm not going to stress about it. I'm just going to leave it the way it is.
I just hate Microsoft, why can't they make it where every command should be able to be executed from the GUI. Ok, I understand the powershell is powerful, but allow users to chose which one to use, not to limit users to only use powershell.
I'm just going to leave things the way they are.
So with the tolerance level, is there a way to do that in the GUI? Can you tell me how please?
I'm so busy at work, I don't have time to spend hours and hours learning powershell, it's frustrating....
Forgive me for venting using this venue.
Actually, can you tell me how to delete it properly, because it's not being used and no mailboxes should be in.
Actually, since the emloyee is new, she used to work for us a few years ago, she didn't say anything about her old emails, so I'm not going to stress about it. I'm just going to leave it the way it is.
I just hate Microsoft, why can't they make it where every command should be able to be executed from the GUI. Ok, I understand the powershell is powerful, but allow users to chose which one to use, not to limit users to only use powershell.
I'm just going to leave things the way they are.
So with the tolerance level, is there a way to do that in the GUI? Can you tell me how please?
I'm so busy at work, I don't have time to spend hours and hours learning powershell, it's frustrating....
Forgive me for venting using this venue.
you can move it right back after moving it to your tempDB.
Just right-click the user and select new local move request
Select the target DB and on the next page you will find the option to set corruption tolerance.
Just right-click the user and select new local move request
Select the target DB and on the next page you will find the option to set corruption tolerance.
ASKER
why do I even want to move a mailbox to the tempDB, I don't want to do that, just curious, why would I want to do that?
I right click on the user, and no menu comes up, nothing happens.
Please remember, I am using exchange 2013, NOT 2010. This option is not in exchange 2013, as I right click on the user, under mailboxes, and nothing comes up.
I right click on the user, and no menu comes up, nothing happens.
Please remember, I am using exchange 2013, NOT 2010. This option is not in exchange 2013, as I right click on the user, under mailboxes, and nothing comes up.
Dang, I keep forgetting. I've only done them in powershell, but this should work:
http://theucguy.net/mailbox-move-in-exchange-2013/
As for why, Reason #4 here: http://technet.microsoft.com/en-us/library/jj150543%28v=exchg.150%29.aspx
http://theucguy.net/mailbox-move-in-exchange-2013/
As for why, Reason #4 here: http://technet.microsoft.com/en-us/library/jj150543%28v=exchg.150%29.aspx
ASKER
Thanks, I understand now, but how can I tell which one is the old one?
In the EMC, I only see one mailbox, the one I linked with the user account.
If I want to link the old one, I'm not sure what I would have to do?
In the EMC, I only see one mailbox, the one I linked with the user account.
If I want to link the old one, I'm not sure what I would have to do?
You would have to disable it again so there was no mailbox linked to the user. The old mailbox with the data has an identity of "a5dedf3d-b10d-4099-b92d-7
ASKER
forget it, i"m just going to leave it the way it is
ASKER
Thanks for your help.