ChiIT
asked on
Exchange Retention Policies RPT vs DPT and inbox
Hi all,
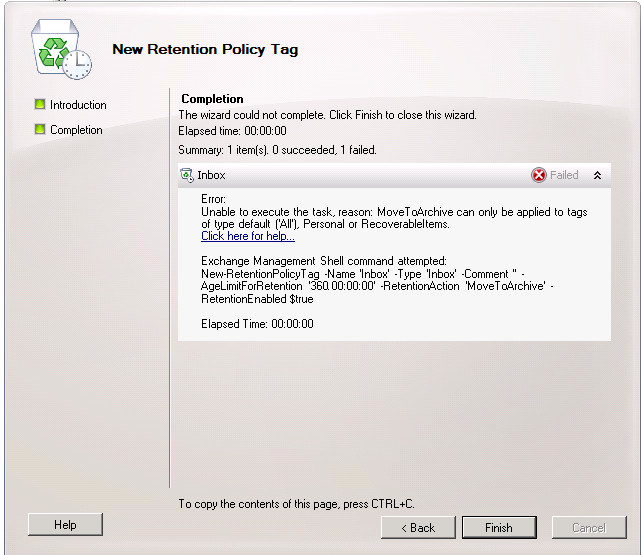
I've been reading up on exchange 2010 retention policies in preparation for implementing a policy and have a question about archiving the inbox. I know you can't use a dpt on the inbox, only an rpt, however there is no option to archive when using an rpt.
How can I archive items that are in the inbox? I'd like to be able to archive inbox items if they exceeded a specific age.
Thanks in advance.
I've been reading up on exchange 2010 retention policies in preparation for implementing a policy and have a question about archiving the inbox. I know you can't use a dpt on the inbox, only an rpt, however there is no option to archive when using an rpt.
How can I archive items that are in the inbox? I'd like to be able to archive inbox items if they exceeded a specific age.
Thanks in advance.
ASKER
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
No problem and thank you for the info. I think I'll stick with option 1, I'm going to leave this open just until I re-read everything today in case I have any other questions...
Sounds good pal. I have NO idea why there are so many limitations here with the retention policies, but what you posted above is honestly news to me.
ASKER
They are "features"
They are "features"
Ah, I see you speak "MSFT talk" also ;) Lots of "caveats" also..
I really did a lot of work with retention policies, tags structure in the past.. and this change shocks me but at the same time it makes sense (mainly for Exchange online.. because you have an archive already in place there - why not use it?)
ASKER
It suprised me because I'd say most people leave emails in their inbox and not move to subfolders, so the inbox seems to be the one that would grow, and the only option there is to delete, which not what kid want to do.
ASKER
Didn't mean to say kid. Meant to say not what you'd want to do.
Hehe - I gotcha pal. Let me know if you have any other questions. I reread a lot of this (and now I am going to write a blog on it at exchangelaboratory.com) but yea.. that is insane.
ASKER
Thanks and appreciate your help. I'll keep an eye open for the blog post and close this out tonight.
By chance you don't know of any free ebd to pst tools do you?
By chance you don't know of any free ebd to pst tools do you?
I do not, and the paid ones I have seen customers (in the past use) never worked out as planned.
Can you send me to the link where you read this? I would recommend reading this, which I wrote about two years ago and cannot update http://blogs.technet.com/b/theexchangeguy/archive/2012/06/04/retention-polices-and-tags-101.aspx (current blog is exchangelaboratory.com, I dont work for MSFT anymore).
You have two primary types of retention tags that you can apply within a retention policy (forget about personal retention tags, users can apply those manually within Outlook)...
Retention Policy Tags: a retention policy tag can only be applied to the default folders
Default Policy Tags: a default policy tag is a blanket tag, which is then applied to all folders that DO NOT have a retention policy tag assigned to them
Keep in mind with the retention policy tag, you cannot say "just tag the root folder and the items within there, not the subfolders", as this is not possible.. if you place the retention policy tag of "Inbox: move to archive after 30 days" this applies to the root folder "inbox" and then all subfolders and items within those subfolders.
Moving on..
For every single policy tag you have the following actions:
- Delete and Allow Recovery – this means we will delete the item, and keep it within the Recoverable Items Folder for the deleted items retention period (allowing recovery)
- Permanently Delete – this is something I typically do not recommend, as this hard deletes an item. What does hard delete mean? When this item is deleted it bypasses the Recoverable Items Folder and is no longer recoverable unless you have a backup.
- Move to Archive - if you have an online archive, then the item will be moved there.
The problem with the default policy tag (which MS never fixed, as they claim its "by design") is that if you apply a default policy tag to the mailbox, this ALSO tags the online archive.
--------------------------
Now that I got that out of the way (my article is a tad bit more clear, but I am probably going to rewrite it as a lot of things changed in terms of calendar tagging and tasks tagging) to accomplish your task do the following:
- Create a new Retention Policy Tag. Set the tag name, tag type (in this case, you would choose the Inbox but remember this will tag both the Inbox folder and all subfolders) along with the age limit for retention and the action to take (move to archive)
- Create a new retention policy, and add the Inbox "move to archive" retention tag
- Assign that retention policy to a users mailbox
- Force run the Managed Folder Assistant to run against the mailbox, which will then start tagging the items with the retention periods
Thats it.. note that when I say "archive" I mean "online archive", an archive mailbox which is held within the Exchange database as a mailbox and NOT a PST file. that is something different and retention policies / tags would not apply here.