SINC_dmack
asked on
Error 812 when connecting to Windows Server 2008 R2 VPN
We recently took over a network where the previous in-house IT guy was fired. He was unbecoming of any credentials, so we've had to reset devices or crack passwords in order to be able to administer properly.
The site was using a Sonicwall TZ215 to act as a VPN server. I've given up on getting that to work--the Sonicwall Global VPN client appears to connect but then throws an error. (I don't remember what but it doesn't matter since I've scrapped it anyway.) I also tried to configure the TZ215's SSL VPN which I seemed to make progress on, until I realized that I couldn't find anywhere to download the Sonicwall VPN client.
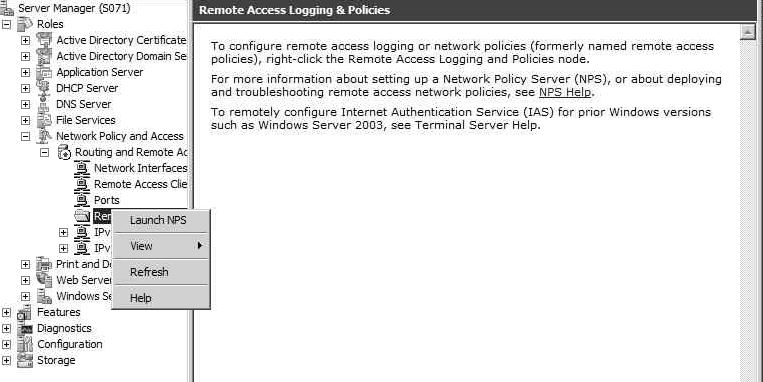
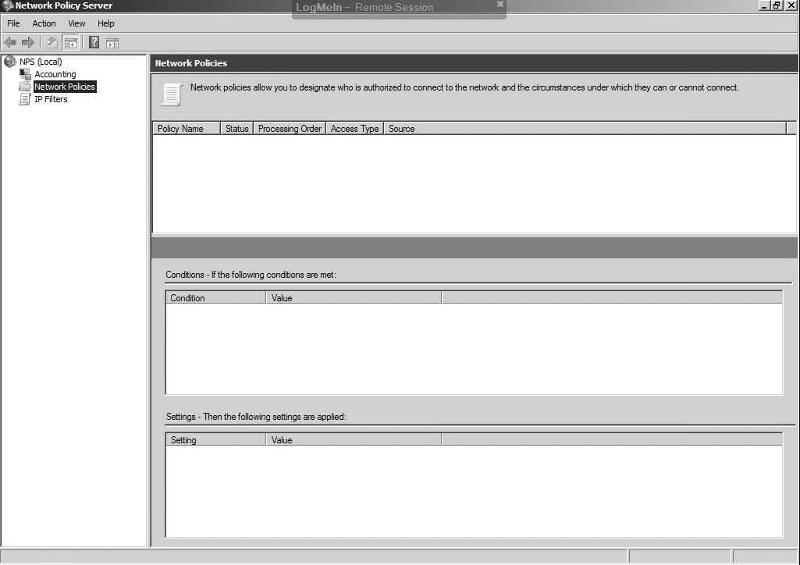
So I defaulted to the lowest common denominator--the Windows Server '08 R2 VPN server. I started out by trying to fix the existing RRAS configuration, but eventually gave up on that. I deleted all of the existing NPS policies (Server Manager -> Roles -> Network Policy and Access -> NPS -> Policies -> Network Policies -> delete everything under Policy Name), disabled RRAS so it would delete its settings (Server Manager -> Roles -> Routing and Remote Access -> right click and Disable Routing and Remote Access), and then I uninstalled RRAS and NPS and rebooted the server.
I reinstalled RRAS using one of the many how-tos on the internet. Some of the specified installing NPS; others didn't. Most recently, I used this one which did not include NPS: http://www.petenetlive.com/KB/Article/0000103.htm
When I attempt to connect via the (internal local Windows 7 Pro) client, I get Error 812: The connection was prevented because of a policy configured on your RAS/VPN server. Specifically, the authentication method used by the server to verify your username and password may not match the authentication method configured in your connection profile.
I have disabled the firewall on the server for testing purposes.
I am using the administrator account for testing. I have gone to ADUC -> Administrator properties -> Dial-in tab -> Network Access Permission -> Allow Access is bulleted.
When I check the Event Viewer, I see EventID 20258 – “The account for user \domain\administrator connected on port VPN3-127 does not have Remote Access privilege. The line has been disconnected.”
I created a new user called admintest and it gets the same error in the event log.
I’ve gone to Computer -> Properties -> Remote Settings -> Remote tab. The bullet is next to Allow connections from computer running any version of Remote Desktop. Under Select Users, I have verified that administrator and admintest are listed.
I am out of ideas. Please advise.
The site was using a Sonicwall TZ215 to act as a VPN server. I've given up on getting that to work--the Sonicwall Global VPN client appears to connect but then throws an error. (I don't remember what but it doesn't matter since I've scrapped it anyway.) I also tried to configure the TZ215's SSL VPN which I seemed to make progress on, until I realized that I couldn't find anywhere to download the Sonicwall VPN client.
So I defaulted to the lowest common denominator--the Windows Server '08 R2 VPN server. I started out by trying to fix the existing RRAS configuration, but eventually gave up on that. I deleted all of the existing NPS policies (Server Manager -> Roles -> Network Policy and Access -> NPS -> Policies -> Network Policies -> delete everything under Policy Name), disabled RRAS so it would delete its settings (Server Manager -> Roles -> Routing and Remote Access -> right click and Disable Routing and Remote Access), and then I uninstalled RRAS and NPS and rebooted the server.
I reinstalled RRAS using one of the many how-tos on the internet. Some of the specified installing NPS; others didn't. Most recently, I used this one which did not include NPS: http://www.petenetlive.com/KB/Article/0000103.htm
When I attempt to connect via the (internal local Windows 7 Pro) client, I get Error 812: The connection was prevented because of a policy configured on your RAS/VPN server. Specifically, the authentication method used by the server to verify your username and password may not match the authentication method configured in your connection profile.
I have disabled the firewall on the server for testing purposes.
I am using the administrator account for testing. I have gone to ADUC -> Administrator properties -> Dial-in tab -> Network Access Permission -> Allow Access is bulleted.
When I check the Event Viewer, I see EventID 20258 – “The account for user \domain\administrator connected on port VPN3-127 does not have Remote Access privilege. The line has been disconnected.”
I created a new user called admintest and it gets the same error in the event log.
I’ve gone to Computer -> Properties -> Remote Settings -> Remote tab. The bullet is next to Allow connections from computer running any version of Remote Desktop. Under Select Users, I have verified that administrator and admintest are listed.
I am out of ideas. Please advise.
ASKER
Gajendra, I have seen that link (and quite a few on how to configure the SSL VPN on the TZ215) but I don't understand where to install the NetExtender client.
You say "You can download NetExtender after login using using HTTPS and either the IP address and port or URL and port to access the Virtual Office VPN connect site" but I have no idea what the IP address or port or URL are for the Virtual Office VPN connect site.
You say "You can download NetExtender after login using using HTTPS and either the IP address and port or URL and port to access the Virtual Office VPN connect site" but I have no idea what the IP address or port or URL are for the Virtual Office VPN connect site.
ASKER
Please check this link
Log out of your Network Security Appliance administration panel to return to the login page.
Click the link in the lower right-hand corner of the dialog that points you to the SonicWALL Virtual Office.
Enter the user name and password you entered and click "Login" to access the SonicWALL Virtual Office.
Download and install the provided NetExtender application.
Double-click the NetExtender icon in your system tray once the installation is complete.
You need to install NetExtender on client machine.
Log out of your Network Security Appliance administration panel to return to the login page.
Click the link in the lower right-hand corner of the dialog that points you to the SonicWALL Virtual Office.
Enter the user name and password you entered and click "Login" to access the SonicWALL Virtual Office.
Download and install the provided NetExtender application.
Double-click the NetExtender icon in your system tray once the installation is complete.
You need to install NetExtender on client machine.
ASKER
Hi Gajendra, I logged out of the TZ215, but there's no Sonicwall Virtual Office link at the login page. I also logged in and browsed through the menus (not too closely, but I did check the VPN and SSL VPN menu trees) but didn't see any mention of the Virtual Office.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
My solution resolved the problem, but it didn't fix it using the existing hardware or software, so I feel like I sort of cheated.
You can download NetExtender after login using using HTTPS and either the IP address and port or URL and port to access the Virtual Office VPN connect site