format disk SQL 64K and performance issue
Hello,
How can I check if disk is formatted 64K?
If not, how can I do it?
Thanks
How can I check if disk is formatted 64K?
If not, how can I do it?
Thanks
How can I check if disk is formatted 64K?
open an elevated command prompt and type diskpart
type list volume and it will show all the volumes; find the volume number by the drive letter you want to check
type select volume x (replace x with the actual volume number)
type filesystems and it will show the allocation size
If not, how can I do it?
the volume will need to be formatted which means you will have to backup any data on that volume first
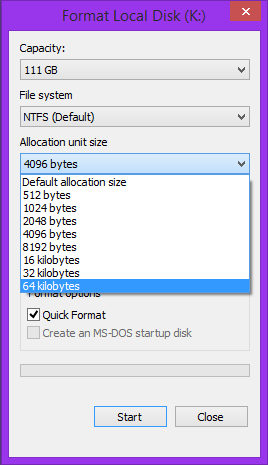
when you format the drive (right-click on the drive in explorer and select format), change the allocation unit size to 64k in the options
ASKER
Thanks but is it possible to align volume disk.
I'm not sure I understand the question.
ASKER
Several volumes have been created on the same disk. Is it possible to align a volume and format each to 64 k. Thanks regards
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
http://www.sqlsolutionsgroup.com/improve-io-performance/