How to remove client access role in exchange 2013
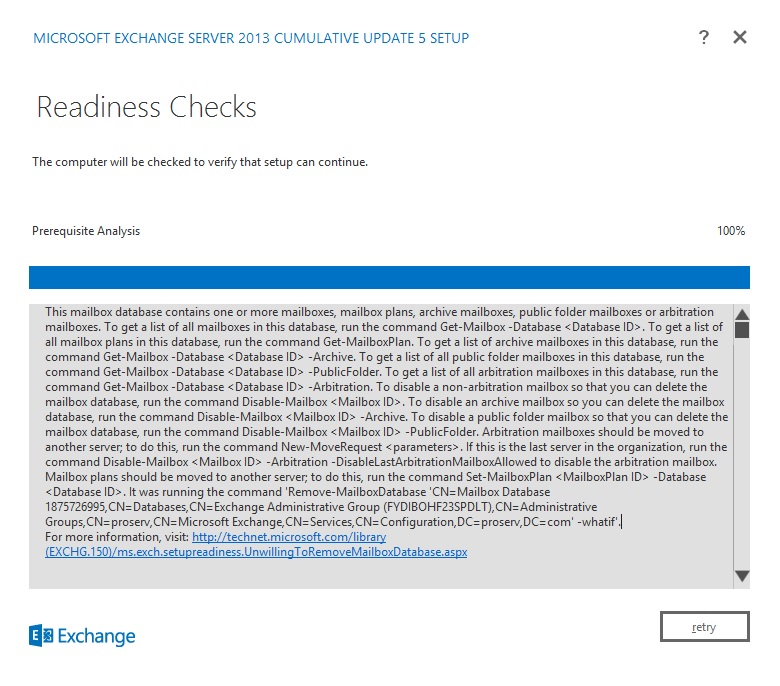
The error you are getting is coming when you are removing the mailbox role.
Therefore you are sure that you selecting the correct option? Do you have other CAS role holders in the Exchange org?
Simon.
Therefore you are sure that you selecting the correct option? Do you have other CAS role holders in the Exchange org?
Simon.
ASKER
yes i have a CAS Role holders in the same exchange server, as in the above screenshort i can not uncheck the CAS role to remove, any idea ?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
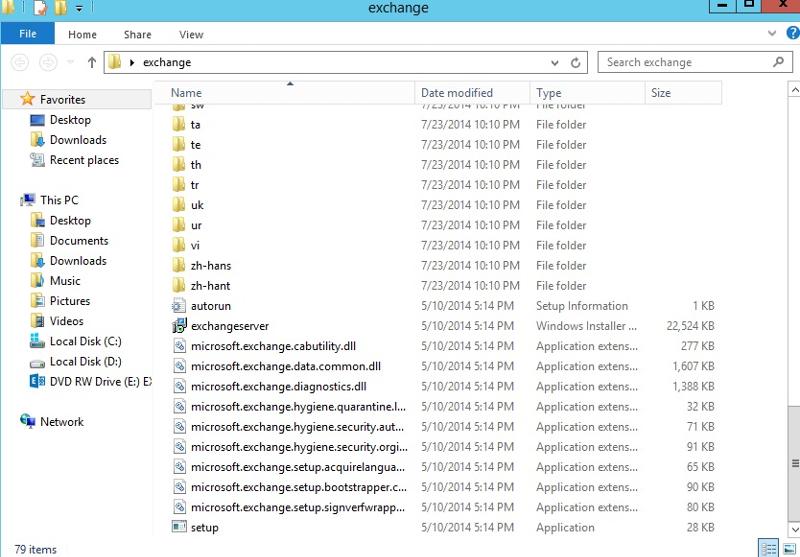
i'm using exchange server 2013 cu 5 to install before, but when i try to click on change from uninstall or change a program, below message pop up, the exchange source that i used to install this exchange is not from media or iso mount, i used the source from the bottom screenshot, i do have a iso of exchange 2013 cu5, i have tried to download a evaluation iso of exchange 2013 without any cu edition, but it dont let me to reinstall CAS, it said the current exchanger version is newer than the one from ISO downloaded from microsoft, just wonder how do i uninstall CAS ?


"i do have a iso of exchange 2013 cu5"
Where did you get that from, as they don't exist as far as I am aware.
Exchange 2013 ISOs are RTM and I believe SP1 only. All CU updates are the extracted file download method.
You need to put the installation files in the same place that they were originally.
Simon.
Where did you get that from, as they don't exist as far as I am aware.
Exchange 2013 ISOs are RTM and I believe SP1 only. All CU updates are the extracted file download method.
You need to put the installation files in the same place that they were originally.
Simon.
ASKER
the installation file that for CU 5 i placed on the desktop, and i used the cu 5 for first exchange installation, when i want to uninstall the CAS, buy clicking "change" it said please run the setup installation media location, then i tried to run the setup file from cu5 source from desktop, it doesnt allow me to uncheck the CAS from the box, also i tried to mount the exchange iso, but it said version issue, doesnt allow me to uninstall, any idea ?
It needs to be in the exact same location as it was when originally installed.
You need to double click on the CU5 download file and extract the file to a path.
You can get the location out of the registry, but the exact key I don't know for CU5.
It will be under this path somewhere:
HKLM\SOFTWARE\Microsoft\Wi
Simon.
You need to double click on the CU5 download file and extract the file to a path.
You can get the location out of the registry, but the exact key I don't know for CU5.
It will be under this path somewhere:
HKLM\SOFTWARE\Microsoft\Wi
Simon.
ASKER