Mahmoud Noubani
asked on
Domain and trust between two domains but list users only from one side.
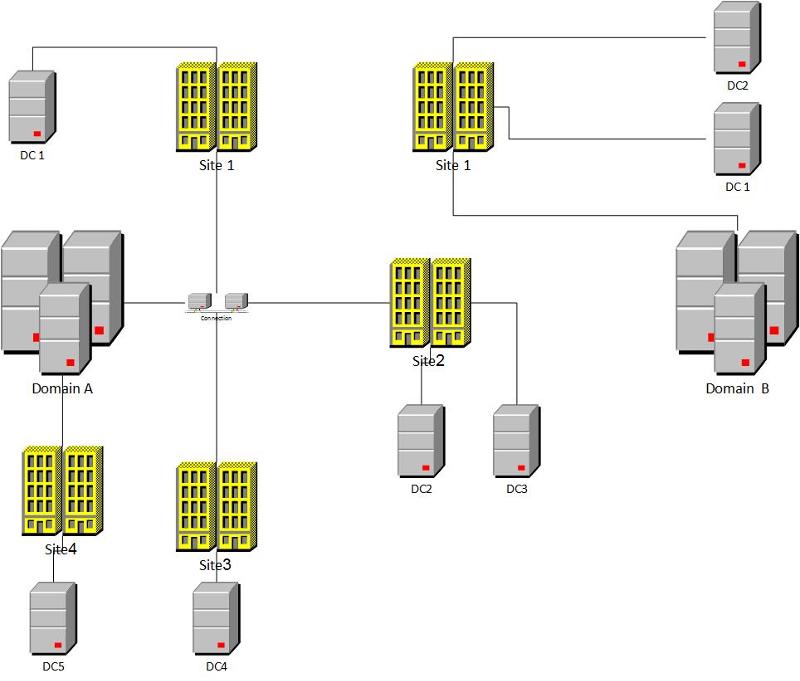
I have a problem with the domain and trust relationship between two different domains as you can see in drawing1.jpg >> we did trust between domain A and domain B and it's successfully created >> Domain "A" has multiple sites >> domain B has one site ..The problem is when we list the resources "Users ,computers..etc " of domain B from Domain A it's listing them but it did not list users,computers of domain A from domain B and it asks you to enter user name and password ,when you enter any Enterprise admin of domain A or domain B it shows to you "Access is denied " and images number 1,2,3 logged in the event viewer
Please bear in mind the following items
1-Stub zone created on both domains.
2-we did the same configurations in new domain"test.com " in the same physical location as domain A <<we did Trust between Domain B and Test .com and it worked fine "listing the resources " from both sides.
3-VMware Tools has been removed from all servers.
4-Firewall is off on both domains.
5-subnets crated for all sites.
6-They have the same forest and domain functional level 2003.
7-Domain A has windows server 2003 and domain B windows server 2008.
Please advise about this issue..Thanks.
break / remove your trust and then create a 2 way transitive trust again
ASKER
Hello david ;
Thanks for your reply I did that many times and created forest ;transitive ;one way trust incoming ;and one outgoing with the same results "error message "
Thanks for your reply I did that many times and created forest ;transitive ;one way trust incoming ;and one outgoing with the same results "error message "
It seems to be an authentication permission issue. Have you verified the domain B has proper authentication permission in Domain A?
ASKER
Yes Zacharia,
We use Domain admin user of domain A and domain B ,enterprise admin of A and B also.
We use Domain admin user of domain A and domain B ,enterprise admin of A and B also.
What is the Domain Function Level and Forest Function Level for domain B ?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Hello,
Also to create a forest trust, the minimum forest functional level for the forests that are involved in the trust relationship is Windows Server 2003.
For more information about trust requirements:
http://technet.microsoft.com/en-us/library/cc816810(v=ws.10).aspx
Also to create a forest trust, the minimum forest functional level for the forests that are involved in the trust relationship is Windows Server 2003.
For more information about trust requirements:
http://technet.microsoft.com/en-us/library/cc816810(v=ws.10).aspx
Abduljalil, the information in both of your last 2 comments is already in the original question.
The problem is when we list the resources "Users ,computers..etc " of domain B from Domain A it's listing them but it did not list users,computers of domain A from domain B
What kind of trust have you created? Could you please give more details?
Are you sure that the "DNS" records are been populated properly in your forests?
Did you make sure the domain admins have proper authentications rights on each forest?
Just for you clarification with regard to the trusts please have a look into the below link.
http://www.edwardsd.co.uk/work/2012/02/domain-trusts-guide/
I believe that you have created only "one way trust" which allows you only to access Domain B from Domain A. Is this your requirement or do you want to have access vise versa?
http://www.edwardsd.co.uk/work/2012/02/domain-trusts-guide/
I believe that you have created only "one way trust" which allows you only to access Domain B from Domain A. Is this your requirement or do you want to have access vise versa?