Brandon Garnett
asked on
Access Report Events
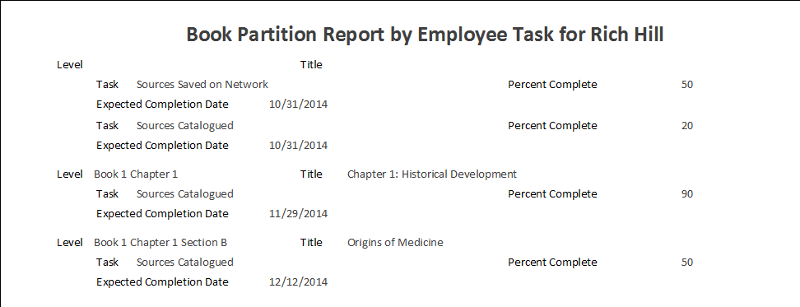
I am using the report_open event in access and I have code in it to change the value of a text box for each different item that loads. It fires the correct amount of times, but it fires too soon. Is there a way to wait for the elements on the page to load and then run the function? Right now all my data is shifted down one item. The level and title are the items that are wrong. The rest of the data is correct. The level and title for the first item are blank, but the level and title for the second item should be in the first items place and the third item in the second. It is also not running the last items level and title. 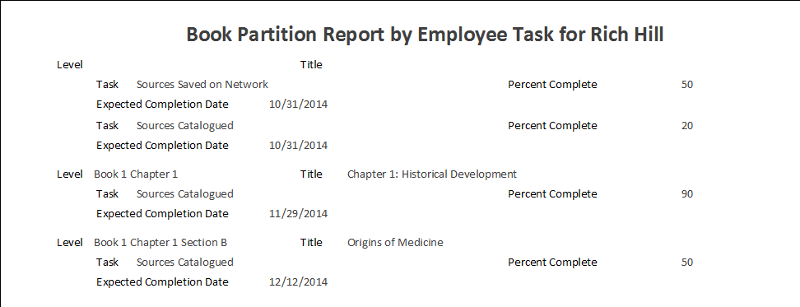
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Please reply to the above two experts first...
what is this function? What does it change and why?
For example, If your report is based on a table or query, ...then what needs to "change" for each record or group?...
...In other words, perhaps there is a better way to accomplish this...
(Perhaps adding the function to be called in a field in the reports recordsource/query, ...instead of trying to do this with report events.
JeffCoachman
I have code in it to change the value of a text box for each different item that loads.
Is there a way to wait for the elements on the page to load and then run the function?Can you clearly explain what that means?, ...and provide an explanation or example?
what is this function? What does it change and why?
For example, If your report is based on a table or query, ...then what needs to "change" for each record or group?...
...In other words, perhaps there is a better way to accomplish this...
(Perhaps adding the function to be called in a field in the reports recordsource/query, ...instead of trying to do this with report events.
JeffCoachman
ASKER
Placing my code in the OnFormat event worked.
If more work is needed, upload a sample report demonstrating the issue.