Microsoft SQL Server
--
Questions
--
Followers
Top Experts
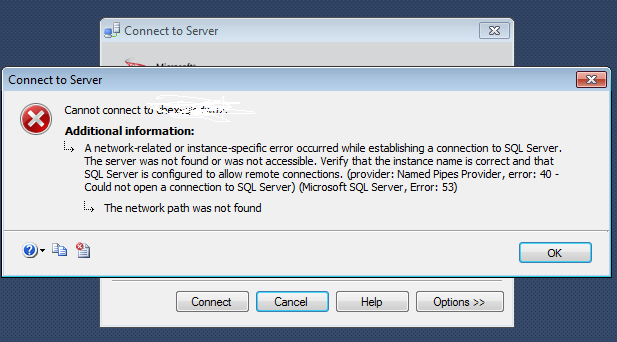
See attached for error message.
I confirmed on another machine that I am able to log into the correct server using windows authentication. My IT department has reinstalled the software 3 times and on the first attempt it was discovered that my new machine had several failed update installs on it, after this was recified, the software appeared to install correctly. but still failed to be able to log into the server.
Looking for suggestions to pass on to my IT department.
Thanks,
Karen
Zero AI Policy
We believe in human intelligence. Our moderation policy strictly prohibits the use of LLM content in our Q&A threads.
1.
Is there a database-alias on the older/working workstation where you successfully connected? (windowkey-R, sqlconfg)2.
If you right-click on the shortcut for SQL Server Management Studio (SSMS) and click run as administrator, does that help?3.
Does your older/working workstation have a fixed IP-address, which may be used in a firewall-rule allowing you access to the database server?thanks,
Karen






EARN REWARDS FOR ASKING, ANSWERING, AND MORE.
Earn free swag for participating on the platform.
Microsoft SQL Server
--
Questions
--
Followers
Top Experts
Microsoft SQL Server is a suite of relational database management system (RDBMS) products providing multi-user database access functionality.SQL Server is available in multiple versions, typically identified by release year, and versions are subdivided into editions to distinguish between product functionality. Component services include integration (SSIS), reporting (SSRS), analysis (SSAS), data quality, master data, T-SQL and performance tuning.