WIn8.1 shortcut to desktop from start screen does not appear to work
Hello,
I just installed my new Win8.1 computer and am gradually acclimating to it. That said, I've encountered a (minor) issue.
When I click on the windows icon on the lower-left of my screen it brings up the Start Screen (with the tiles -- I think that's what you call them) representing the various programs. One of the tiles clearly indicates that it's for my desktop -- I can even see the wallpaper I installed; however, when I click on it, it takes me back to what appears to be the application I am currently using.
How then, can i most easily access the actual desktop (from both the Start screen) and elsewhere.
Thanks,
Steve
I just installed my new Win8.1 computer and am gradually acclimating to it. That said, I've encountered a (minor) issue.
When I click on the windows icon on the lower-left of my screen it brings up the Start Screen (with the tiles -- I think that's what you call them) representing the various programs. One of the tiles clearly indicates that it's for my desktop -- I can even see the wallpaper I installed; however, when I click on it, it takes me back to what appears to be the application I am currently using.
How then, can i most easily access the actual desktop (from both the Start screen) and elsewhere.
Thanks,
Steve
ASKER
John,
I guess I'm still a bit unclear (on MY end) per Win8.1 terminology.
When you say "I use the desktop". to what are you referring?
1. The screen that when you start using your new computer has maybe one or two icons on it and on which you can add icons?
2. The screen that has the tiles or whatever you call them with names such as MAIL, CALENDAR, WEATHER, etc.
3. The screen (that you access via the downarrow from #2) that contains tons of applications grouped by letter of the alphabet and "topic" area?
Thanks again.
Steve
I guess I'm still a bit unclear (on MY end) per Win8.1 terminology.
When you say "I use the desktop". to what are you referring?
1. The screen that when you start using your new computer has maybe one or two icons on it and on which you can add icons?
2. The screen that has the tiles or whatever you call them with names such as MAIL, CALENDAR, WEATHER, etc.
3. The screen (that you access via the downarrow from #2) that contains tons of applications grouped by letter of the alphabet and "topic" area?
Thanks again.
Steve
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
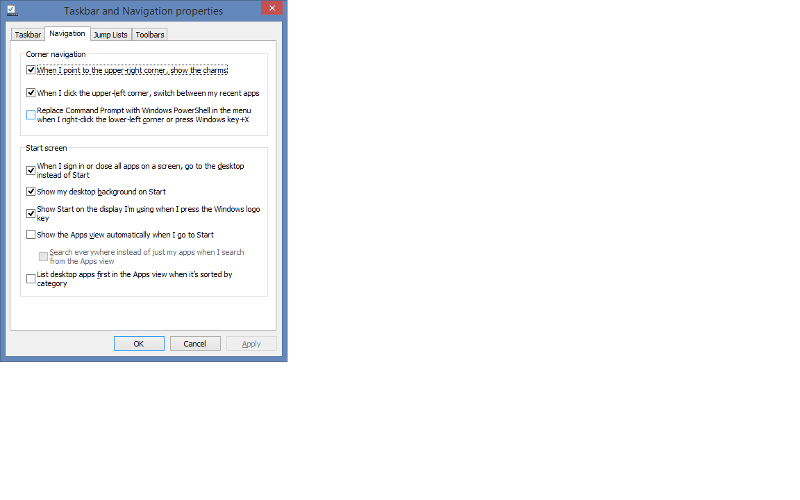
If you restart after checking the boxes above, then upon startup, you should be seeing a standard Windows Desktop (not the Metro screen). Is this true? Please let us know.
Then, what Icon and shortcut are you talking about?
Any application shortcut on the Windows Desktop will keep you in the Desktop. Again, this is where your regular applications live.
Then, what Icon and shortcut are you talking about?
Any application shortcut on the Windows Desktop will keep you in the Desktop. Again, this is where your regular applications live.
ASKER
OK maybe I wasn't being clear
This is the screen I mean:
With the DESKTOP icon in the lower-left, the one with the picture of the moon which is my wallpaper.
Thanks
Steve
This is the screen I mean:
With the DESKTOP icon in the lower-left, the one with the picture of the moon which is my wallpaper.
Thanks
Steve
ASKER
OK the image did not appear. Oops. Trying again...
Screen-with-a-lot-of-icons-on-it.png
Screen-with-a-lot-of-icons-on-it.png
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
OK. So when you refer to installing my regular apps on my "desktop" do you mean this:
Thanks.
Desktop-moon.png
Thanks.
Desktop-moon.png
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Rindi and John,
Thank you both for your help!
Steve
Thank you both for your help!
Steve
@stevefromc - You are very welcome and I was happy to help.
Add a Start Menu to Windows 8
Right Click on the Taskbar
Select Toolbar, New Toolbar
Add the following content in the space provided:
%ProgramData%Microsoft\Win
Save the toolbar. It should call itself Programs.
Everything you need is now in Programs on the taskbar.
Read my article on ways to improve Windows 8. I have been using it now for about 2 years.
https://www.experts-exchange.com/OS/Microsoft_Operating_Systems/Windows/A_16620-Ways-to-improve-Windows-8.html