SimonBrook
asked on
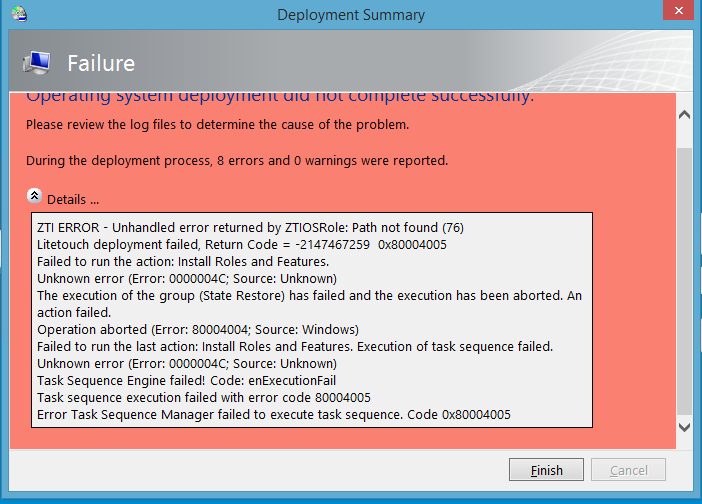
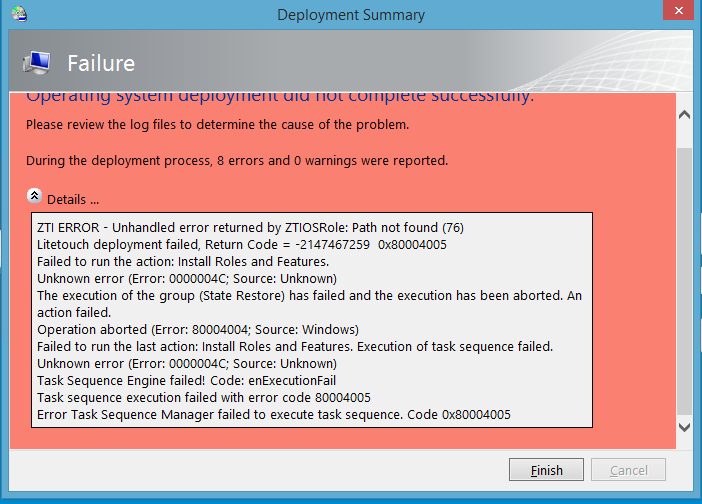
Deploy Windows 8.1 MDT / Litetouch Error on Surface Pro 3
Hello,
I'm having problems deploying our Windows 8.1 image to Surface Pro 3's.
I get as far as Installing "Roles and Features -> processing netfx3" before things start going wrong. This build works on other laptops and we've injected the drivers for the surface pro 3.
"ZTI Error - Unhandled error returned by ZTIOSRole: Path not found (76)"
Any ideas?
Thanks,
I'm having problems deploying our Windows 8.1 image to Surface Pro 3's.
I get as far as Installing "Roles and Features -> processing netfx3" before things start going wrong. This build works on other laptops and we've injected the drivers for the surface pro 3.
"ZTI Error - Unhandled error returned by ZTIOSRole: Path not found (76)"
Any ideas?
Thanks,
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
PXE boot server was pointing build or different (wrong) server. Resolved and now working.
just wondering if you have had any issues with Surface Pro 3 crashing after being imaged using MDT?
Check the below link :-
http://goo.gl/f1eHXo
Bahloul.