WIndows 7 Pro losing Activation all of a sudden?
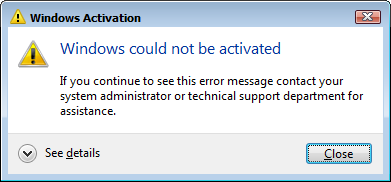
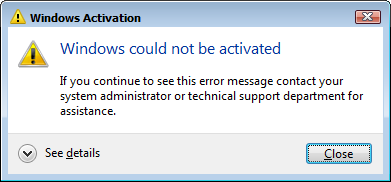
We have two users, both using the same type of laptop- an HP Elitebook 8460p, that suddenly after many months/years of use are getting a pop up that 'Windows could not be activated'.
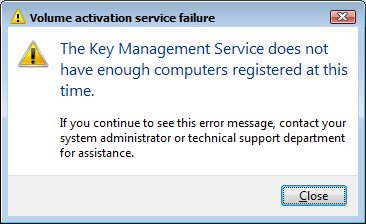
One of the machines also threw the error 'They KeyManagement Service does not have enough computers registered at this time.' I don't know what this even means- we do not have any volume licensing for Windows. We have many (about 80) of these 8460P laptops in circulation since 2013 and all of them had Windows 7 Pro pre-installed on them when we bought them.
What would cause this to happen, all of a sudden, to two of them ?
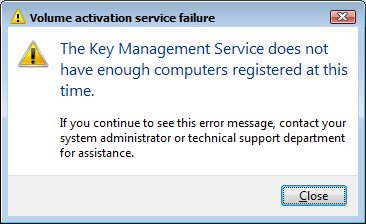
One of the machines also threw the error 'They KeyManagement Service does not have enough computers registered at this time.' I don't know what this even means- we do not have any volume licensing for Windows. We have many (about 80) of these 8460P laptops in circulation since 2013 and all of them had Windows 7 Pro pre-installed on them when we bought them.
What would cause this to happen, all of a sudden, to two of them ?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
OK, so it says it's licensed, so that's good...yet it says it's unactivated? Maybe try running slmgr /ato from the command line and then restart and re-check it.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
We don't do key activation on our network, no. I just had another user report they are receiving the 'The Key Management Service does not have enough computers registered at this time.." error. This is not an HP Elitebook 8460p, but another HP model altogether. As I mentioned before - we do buy these laptops with Win 7 Pro already installed... and we then install Office 2010 Standard and activate it online with Microsoft... is that somehow related?
ASKER
..but again, just to reiterate, these computers just suddenly started doing this. They have all been with users for 1 year or more.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Need to check if you have OEM systems
Can you download and run this tool on a machine that shows as could not be activated and one with the Key Management Server error.
http://go.microsoft.com/fwlink/?linkid=52012
In both cases the tool will generate a text output, could you post them both here?
Can you download and run this tool on a machine that shows as could not be activated and one with the Key Management Server error.
http://go.microsoft.com/fwlink/?linkid=52012
In both cases the tool will generate a text output, could you post them both here?
So did you try to uninstall KB3004394 yet? It's a known buggy update that causes different types of activation/not genuine errors.
ASKER
I split the points and I thank everyone who assisted. The cause was something I did not even mention because at the time did not think of it. Users connect to Citrix XenAPP servers for business applications. The Windows 2008 o/s on the servers is controlled by KMS. There was actually an issue with that process and that was the activation error they were seeing..(inside their citrix sessions.) Thanks again!
snyperj--Thanks for telling us the problem.
ASKER
Below are the results from both computers exhibiting the problem: