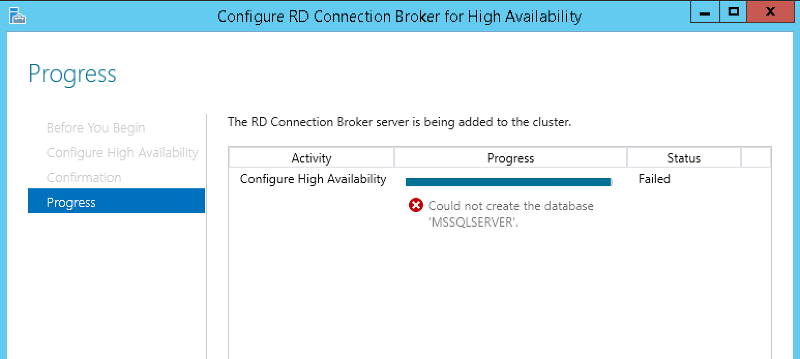
RD Connection Broker for High Availability could not create database error
does the database server have tcpip/named pipes enabled? (sql configuration manager) does that account have login properties?
Are you trying to connect to remote SQL server? Please provide the DB connection string just as well or at the very least the syntax you are using.
Have you confirmed that you have met all the prerequisites for High Availability for the RD Connection Broker role?
Taken from this following Microsoft blog post: http://social.technet.microsoft.com/wiki/contents/articles/10390.deploying-rd-connection-broker-high-availability-in-windows-server-2012.aspx
Have you confirmed that you have met all the prerequisites for High Availability for the RD Connection Broker role?
Taken from this following Microsoft blog post: http://social.technet.microsoft.com/wiki/contents/articles/10390.deploying-rd-connection-broker-high-availability-in-windows-server-2012.aspx
- A Microsoft SQL Server with write permissions granted to all RD Connection Broker servers that will be part of the deploymentAlso make sure that your SQL permissions and firewall is configured correctly: http://social.technet.microsoft.com/wiki/contents/articles/10393.rd-connection-broker-ha-sql-permissions.aspx
- The Microsoft SQL Server Native Client is installed on all RD Connection Broker servers that will be part of the deployment
- Static IP addresses have been assigned to all RD Connection Broker servers that will be part of the deployment
- DNS resource records with a single DNS name have been created for all RD Connection Broker servers that will be part of the deployment
- Also note that the SQL Server must be at least SQL Server 2008 R2.
ASKER
Hi VB ITS, I've done everything in the documentation you mentioned.
It's interesting I didn't pass the following at first: Configure: Database connection string, Folder to Store Database Files, DNS Round Robin Name until I removed SQL completely and reinstalled.
After doing so I can now get past the above screen but it fails with the screen shot.
Seems like something with SQL to me.
It's interesting I didn't pass the following at first: Configure: Database connection string, Folder to Store Database Files, DNS Round Robin Name until I removed SQL completely and reinstalled.
After doing so I can now get past the above screen but it fails with the screen shot.
Seems like something with SQL to me.
There's no error log? Or at least an entry in the Event log?
That error message is too generic and we need to get something more to point you to the right direction.
That error message is too generic and we need to get something more to point you to the right direction.
You'll need to provide more information as Vitor has mentioned above. Can you please at least confirm that you have a dedicated SQL server running at minimum SQL Server 2008 R2?
Have you verified that your environment meets the minimum requirements outlined in my previous comment?
Have you verified that your environment meets the minimum requirements outlined in my previous comment?
ASKER
Yes all the requirements are met and tried SQL Server 2008 and 2012 R2.
ASKER
Dell support has been working on it for hours, appears it may be something in the registry and at this point a fresh install is likely the way to go. The server was taken out of the box four days ago, it's this new and nothing is on it. Problem is we really need the remote access.
Others have had this problem with the same results (not allot of information reporting back). Others that had this problem didn't report a solid way to fix which doesn't help much. When I say "Others" I mean the few posts I found.
Others have had this problem with the same results (not allot of information reporting back). Others that had this problem didn't report a solid way to fix which doesn't help much. When I say "Others" I mean the few posts I found.
it shouldn't be creating a database mssqlserver but a database ON servername\mssqlserver. This is the default instance, if you changed the instance name then it would be server\instancename
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank you for all the help, greatly appreciated.