sglee
asked on
Increase OS partition size in Windows 2008 VM in VMWare
Hi,
I have VMWare V5.1 with several VMs. One of them is Windows 2008 Server and it is running out of space and I need to increase the size.
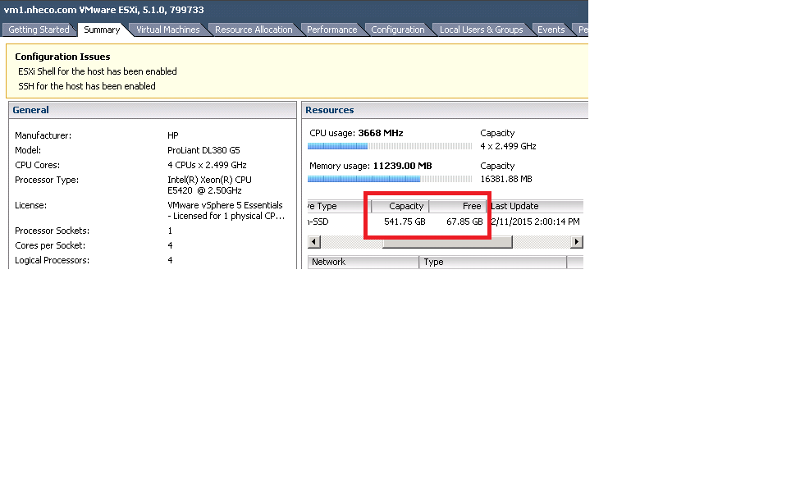
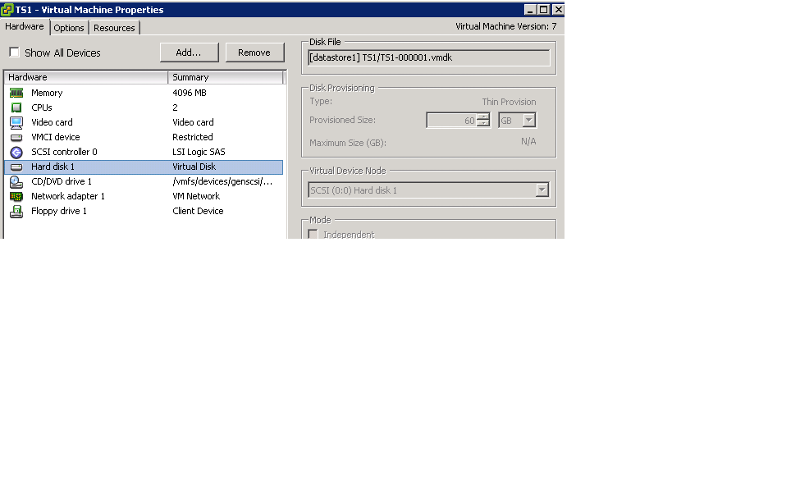
When I check the storage section in VShpere Client program, it shows that is about 67GB available. In Windows 2008 Virtual Machine, I have about 16GB left. I ran DiskMgmt and right clicked on the drive C, but I don't see "Extend" option.
With that I have two questions.
(1) Why Extend option is recessed?
(2) If I extend, knowing that there is 67GB total available, how much space in GB would be safe number? Is there a danger of assigning all 67GB to this W2008 VM?
Thanks.
Cancel
Top Experts
I have VMWare V5.1 with several VMs. One of them is Windows 2008 Server and it is running out of space and I need to increase the size.
When I check the storage section in VShpere Client program, it shows that is about 67GB available. In Windows 2008 Virtual Machine, I have about 16GB left. I ran DiskMgmt and right clicked on the drive C, but I don't see "Extend" option.
With that I have two questions.
(1) Why Extend option is recessed?
(2) If I extend, knowing that there is 67GB total available, how much space in GB would be safe number? Is there a danger of assigning all 67GB to this W2008 VM?
Thanks.
Cancel
Top Experts
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
@Andrew
Can you elaborate on "or it's a system OS disk you have."?
Fyi, there is an old VM (no longer used) that I can delete and it will free up about 150GB of space.
Can you elaborate on "or it's a system OS disk you have."?
Fyi, there is an old VM (no longer used) that I can delete and it will free up about 150GB of space.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
You don't have any un-allocated storage space on the disk, hence why the option is grayed out.
you can delete the old VM, and then increase the disk space on this VM.
see my EE article for details.
you can delete the old VM, and then increase the disk space on this VM.
see my EE article for details.
ASKER
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I have backup program called Nakivo. Does it create a snapshot when it is doing the backup of VMs?
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Sounds like it is not that simple. I have decided to leave it as it is until I have to.
For now there is 16GB of space left and is enough to get by.
For now there is 16GB of space left and is enough to get by.
ASKER