Embedded Webpage Videos don't auto play on Windows 7
Client's computer stopped auto-playing embedded videos on web pages, and they would like the videos to start again.
Windows 7 Pro 64
Websites that used to auto-play:
I looked at one of the web pages that I visit, and I noticed that the embedded video had a link to "never autoplay videos"
Is there a reverse option for this that would start auto-playing the videos? A right-click didn't offer any options.
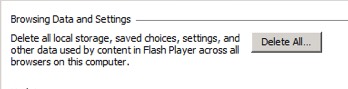
I realize that there are different plug-ins for playing embedded videos. I didn't see any specific options in the Flash Player Control Panel, but I saw an option to delete all local storage, saved choices, settings, and other data.
Would this reset auto-play option for embedded Flash videos?
Windows 7 Pro 64
Websites that used to auto-play:
GoldDerby.com
HollywoodReporter.com
LAtimes.com
HollywoodReporter.com
LAtimes.com
I looked at one of the web pages that I visit, and I noticed that the embedded video had a link to "never autoplay videos"
Is there a reverse option for this that would start auto-playing the videos? A right-click didn't offer any options.
I realize that there are different plug-ins for playing embedded videos. I didn't see any specific options in the Flash Player Control Panel, but I saw an option to delete all local storage, saved choices, settings, and other data.
Would this reset auto-play option for embedded Flash videos?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.