John Steele
asked on
Open specific ports on ASA5505 for backup appliance
We have installed a Barracuda Backup appliance inside our network protected by a Cisco ASA5505 firewall. Per Barracuda:
Ports 80/443 and 1194 outbound for both TCP and UDP are required for communication while ports 5120-5129 are used to replicate data to Barracuda Cloud Storage
I have an SBS 2008 Server inhouse so I presume 80/443 are open, however, I need to open ports 1194 and 5120-5129, as the appliance cannot talk to Barracuda at all. I put old firewall in and was able to activate backup appliance but once put ASA firewall back in, backup appliance stops communicating to Barracuda.
I have access through ASDM or Putty. I have figured out how to log into ASA5505 via Putty but unsure what to do after that. ASDM is confusing.
Can anyone provide me with commands to open these ports via Putty or directions to do so through ASDM? I know how to do this on other firewalls, but this ASA5505 escapes me.
Ports 80/443 and 1194 outbound for both TCP and UDP are required for communication while ports 5120-5129 are used to replicate data to Barracuda Cloud Storage
I have an SBS 2008 Server inhouse so I presume 80/443 are open, however, I need to open ports 1194 and 5120-5129, as the appliance cannot talk to Barracuda at all. I put old firewall in and was able to activate backup appliance but once put ASA firewall back in, backup appliance stops communicating to Barracuda.
I have access through ASDM or Putty. I have figured out how to log into ASA5505 via Putty but unsure what to do after that. ASDM is confusing.
Can anyone provide me with commands to open these ports via Putty or directions to do so through ASDM? I know how to do this on other firewalls, but this ASA5505 escapes me.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
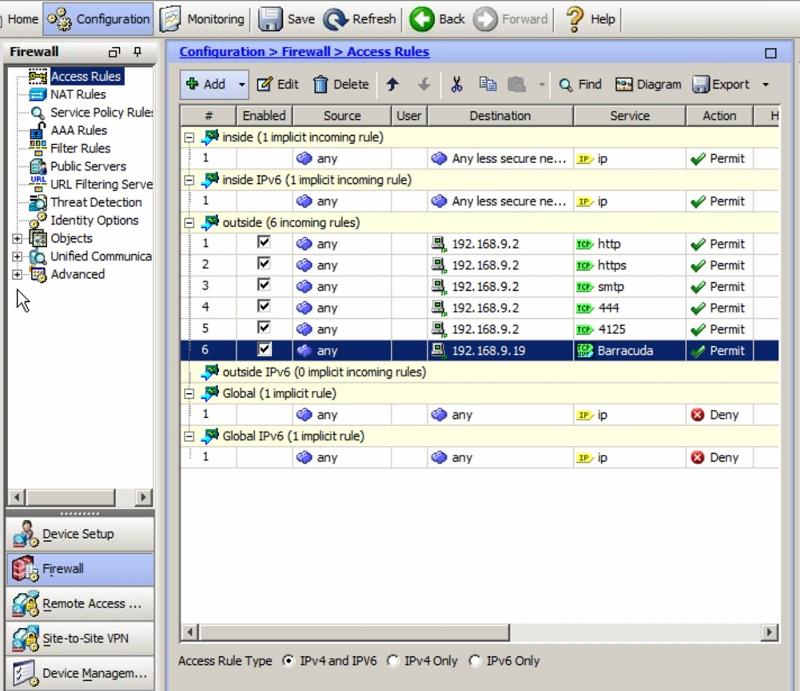
wouldn't it be interface "outside"? Looking at the existing SBS rules, they are all under "outside"...???
Can you post a screenshot of what you are doing?
Outside is only to be used if you are "hosting" something, SBS for instance needs outside rules for Exchange/OWA, Remote desktop if you use those services.
Outside is only to be used if you are "hosting" something, SBS for instance needs outside rules for Exchange/OWA, Remote desktop if you use those services.
ASKER
ASKER
Third time was a charm. Thank you for your help.
Glad it worked out.
ASKER
Hey Spartan-Thank you very much for such a quick response to my question. You are appreciated!!
ASKER