VirtualBox machine has different Default Gateway
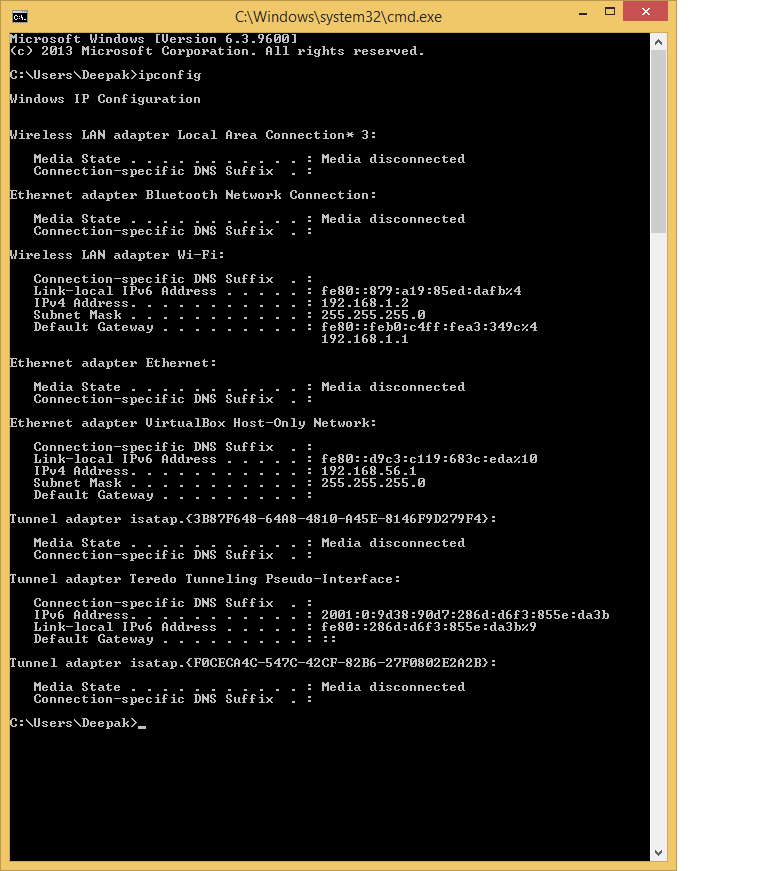
I have Windows 8.1 as my host machine and
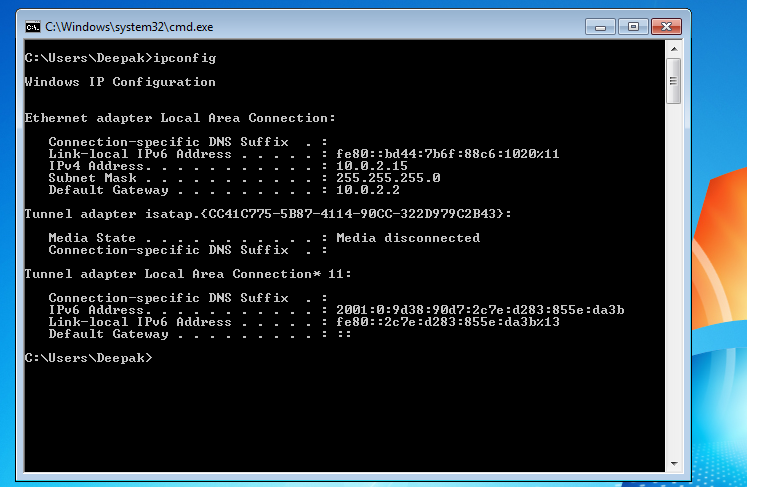
under virtual box I am trying to run Windows 7.
But the issue is from Windows 7 I am not able to access my host on network.
I came to know that the network settings are different on Windows 7 like Default Gateway.
I need to know what settings I need to do so that I can access my host machine from my Virtual box windows 7.
under virtual box I am trying to run Windows 7.
But the issue is from Windows 7 I am not able to access my host on network.
I came to know that the network settings are different on Windows 7 like Default Gateway.
I need to know what settings I need to do so that I can access my host machine from my Virtual box windows 7.
ASKER
From Windows 7 machine, I am not able to access the host machine when I do \\192.168.5.1 (ip Address of host machine).
I don't have any other machine on the network.
I don't have any other machine on the network.
are you able to ping ?
What is windows 7 IP addresS?
What are the IP addresses of the machines? Are you using NAT or bridged networks?
ASKER
I am able to ping the host machine from windows 7.
on Windows 7 I am using the default Nat
on Windows 7 I am using the default Nat
have you given Static ip ??
ASKER
no, I havn't given static IP.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
or give static ip in the same range.. which windows8 has
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks the Bring network works for me.
Thanks for help
Thanks for help
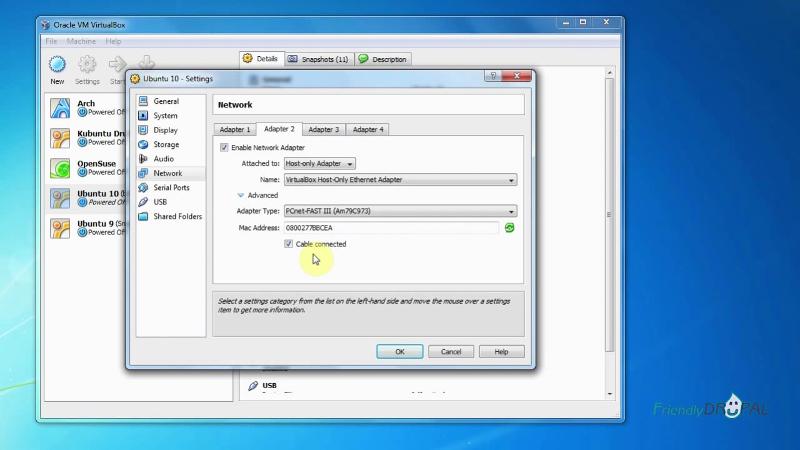
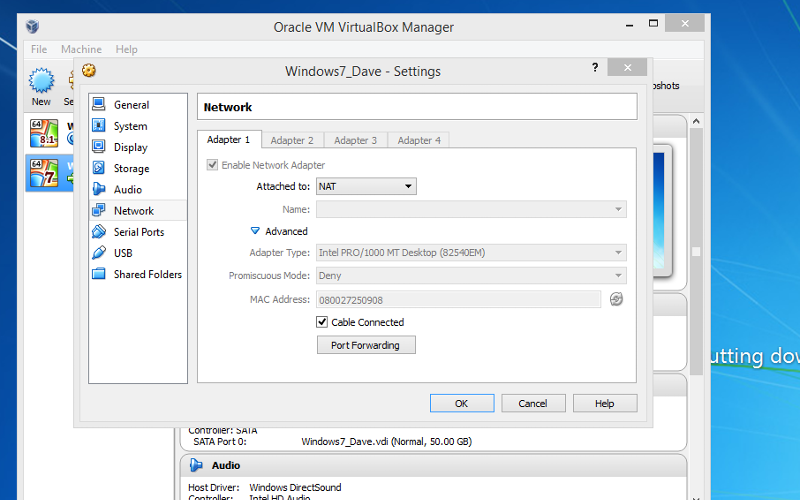
by default when you create Virtual machine in virtual box it use NAT network in that vm will be communicated with host machine.