creative555
asked on
is there a way to run certutil for remote computer? switch -dc doesn't work
Hello,
I found this command that exports the certificates from computer personal store into text file. It is exactly what I need except is there is a way to query the remote servers to get the same info from computer personal store for the cert?
HEre is the command line that I need to work with remote computer:
certutil -store -v my > export.txt
WHen I run this command specifying the remote server I get this error:
certutil –store –v my –dc servername01 > >\output.txt
CertUtil: -store command FAILED: 0x80090011 (-2146893807)
CertUtil: Object was not found.
To display the certificates in the Local Machine certificate store:
CERTUTIL -store [-f] [-enterprise] [-user] [-gmt] [-seconds] [-silent] [-v] [-dc dc_name] certificate_store_name [certificate_id [output_file]]
I found this command that exports the certificates from computer personal store into text file. It is exactly what I need except is there is a way to query the remote servers to get the same info from computer personal store for the cert?
HEre is the command line that I need to work with remote computer:
certutil -store -v my > export.txt
WHen I run this command specifying the remote server I get this error:
certutil –store –v my –dc servername01 > >\output.txt
CertUtil: -store command FAILED: 0x80090011 (-2146893807)
CertUtil: Object was not found.
To display the certificates in the Local Machine certificate store:
CERTUTIL -store [-f] [-enterprise] [-user] [-gmt] [-seconds] [-silent] [-v] [-dc dc_name] certificate_store_name [certificate_id [output_file]]
ASKER
ASKER
Is this the Path?
HKLM\SOFTWARE\Microsoft\Sy
HKLM\SOFTWARE\Microsoft\Sy
ASKER
I know i get personall store certificates if I run this command. but same problem here, it doesn't perform remotely. SO, if I do it with registry, I dont have to login to each server :)
certutil –store –v my > >\output.txt
Please help
certutil –store –v my > >\output.txt
Please help
ASKER
no....I get gibberish when I query registry with this script:
REG QUERY "\\%1\HKLM\SOFTWARE\Micros
HKEY_LOCAL_MACHINE\SOFTWAR
HKEY_LOCAL_MACHINE\SOFTWAR
Blob REG_BINARY 0F0000000100000014000000EF
HKEY_LOCAL_MACHINE\SOFTWAR
Blob REG_BINARY 5C000000010000000400000000
HKEY_LOCAL_MACHINE\SOFTWAR
Blob REG_BINARY 5C000000010000000400000000
HKEY_LOCAL_MACHINE\SOFTWAR
Blob REG_BINARY 5C000000010000000400000000
REG QUERY "\\%1\HKLM\SOFTWARE\Micros
HKEY_LOCAL_MACHINE\SOFTWAR
HKEY_LOCAL_MACHINE\SOFTWAR
Blob REG_BINARY 0F0000000100000014000000EF
HKEY_LOCAL_MACHINE\SOFTWAR
Blob REG_BINARY 5C000000010000000400000000
HKEY_LOCAL_MACHINE\SOFTWAR
Blob REG_BINARY 5C000000010000000400000000
HKEY_LOCAL_MACHINE\SOFTWAR
Blob REG_BINARY 5C000000010000000400000000
The certificates are in binary (blob) form; the key names however are the fingerprints for the certs. So, for instance, the cert "VeriSign Trust Network" (1998-2028) has the fingerprint
85 37 1C A6 E5 50 14 3D CE 28 03 47 1B DE 3A 09 E8 F8 77 0F
and a quick check in the registry finds me:
HKEY_LOCAL_MACHINE\SOFTWAR
it is possible to convert the binary blob back into a usable DER file, but its not really required; re-adding the registry key restores the certificate to the keystore, which is all you usually want from a backup :)
85 37 1C A6 E5 50 14 3D CE 28 03 47 1B DE 3A 09 E8 F8 77 0F
and a quick check in the registry finds me:
HKEY_LOCAL_MACHINE\SOFTWAR
it is possible to convert the binary blob back into a usable DER file, but its not really required; re-adding the registry key restores the certificate to the keystore, which is all you usually want from a backup :)
ASKER
hi,
THank you so much for your answer. The purpose of exporting certificates data is to inventory and determine if the applications are using those certs and not the backup. So, we do need to get the output like the one performed with this command:
certutil -store -v my
I guess I don't have a choice and have to login to each server - over 100 servers??
I tried powershell too and it gave me error unrecognizable output. We are using all 2003 DCs, so the powershell is not going to work for 2003 DC I guess? or I should be able to make powershell script do it with 2003 certificate local store?
THank you so much for your answer. The purpose of exporting certificates data is to inventory and determine if the applications are using those certs and not the backup. So, we do need to get the output like the one performed with this command:
certutil -store -v my
I guess I don't have a choice and have to login to each server - over 100 servers??
I tried powershell too and it gave me error unrecognizable output. We are using all 2003 DCs, so the powershell is not going to work for 2003 DC I guess? or I should be able to make powershell script do it with 2003 certificate local store?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
# To get certificate information
cls
# Windows 2012 / 2008R2 local
certutil -view -out "RequestID,RequesterName,R
# Windows 2008 Local
certutil -view -out "RequestID,RequesterName,R
# To get information remote because Windows 2008 does not support[ csv]
# Windows 2008 R2 Remote
certutil -dump # to get –config string
certutil -view -config "host.domain.com\Company Issuing CA 1" -out "RequestID,RequesterName,R
cls
# Windows 2012 / 2008R2 local
certutil -view -out "RequestID,RequesterName,R
# Windows 2008 Local
certutil -view -out "RequestID,RequesterName,R
# To get information remote because Windows 2008 does not support[ csv]
# Windows 2008 R2 Remote
certutil -dump # to get –config string
certutil -view -config "host.domain.com\Company Issuing CA 1" -out "RequestID,RequesterName,R
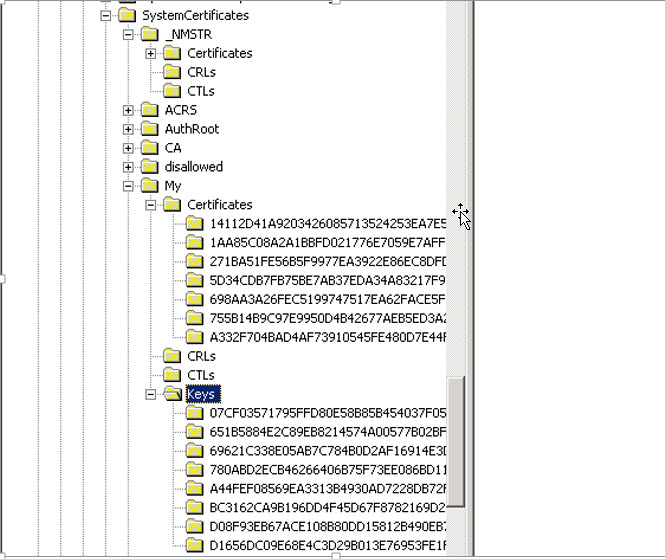
a) keystores are actually only registry keys and
b) you can remotely access the registry
to pull those keys directly :)
take a look at HKEY_LOCAL_MACHINE\SOFTWAR