Troubles with security certificates, exchange 2013, GoDaddy and internet/intranet invalid names
Hi Experts,
As the title suggests, I'm having issues getting my SSL security certificates in Exchange 2013 validating Outlook from both internal and external connections. I can't seem to make the certificate accepted for internal (servername.domainname.loc
Help me Experts-Exchange, you're my only hope.
As the title suggests, I'm having issues getting my SSL security certificates in Exchange 2013 validating Outlook from both internal and external connections. I can't seem to make the certificate accepted for internal (servername.domainname.loc
Help me Experts-Exchange, you're my only hope.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
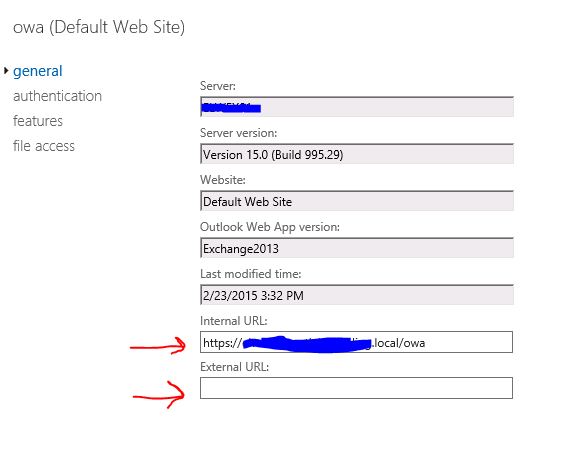
OK, so if I understand correctly, I need to change all the internal and external URL's in the virtual directory entries to https://mail.domainname.com/<type> next to the red arrows? is that correct?
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Oh no, the exchange server is hosted in house, just the certificate comes from GoDaddy. Thnaks, I'll use PS to change the config and report. Thanks fory our help
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks, let me try it.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
checking in... how'd it go?
ASKER
Just picked this up again from being on vacation, thanks for checking in. I'll let you know how it goes.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I figured out the final part of the problem myself.
I was having the same issue. I added the SRV Record and no longer get the warning.
You will need to use a split DNS system to ensure the external name resolves internally, then configure Exchange with the external name for both internal and external URLs.
http://semb.ee/hostnames2013
Simon.