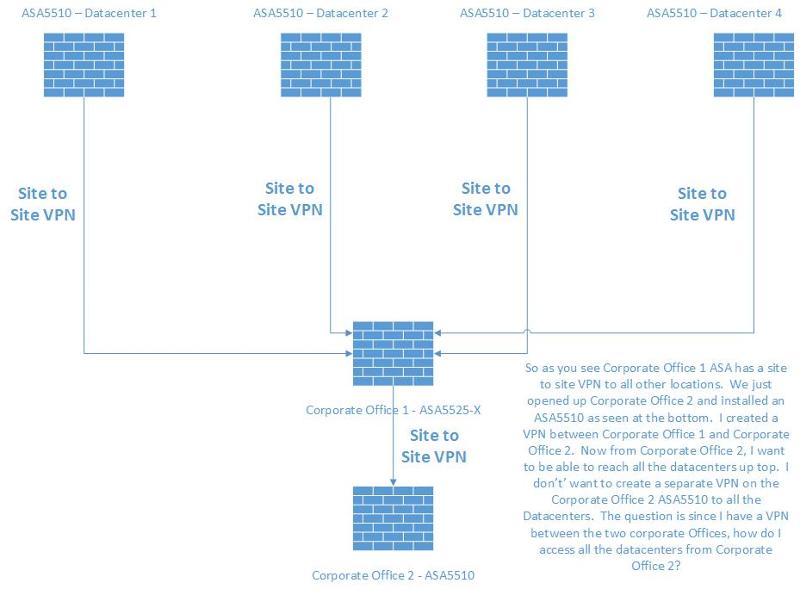
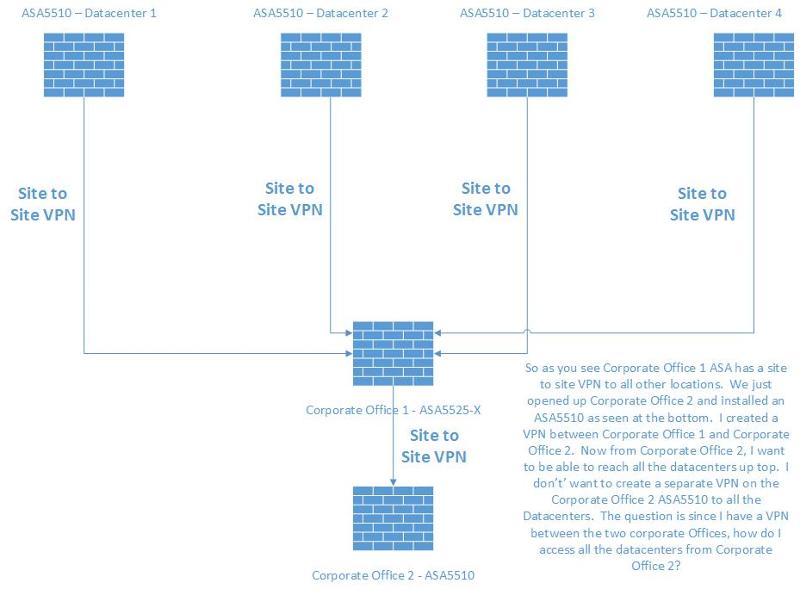
ASA site to site VPN assistance
If you look at network diagram, the corporate Office 1 ASA has a site to site VPN to all other locations. We just opened up Corporate Office 2 and installed an ASA5510 as seen at the bottom. I created a VPN between Corporate Office 1 and Corporate Office 2. Now from Corporate Office 2, I want to be able to reach all the datacenters up top. I don’t’ want to create a separate VPN on the Corporate Office 2 ASA5510 to all the Datacenters. The question is since I have a VPN between the two corporate Offices, how do I access all the datacenters from Corporate Office 2 going through Corporate Office 1?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ffleisma, is correct, If office 2 was of any size I would put in a VPN from it to each DC, but this does not scale very well if you are going to expand!
ASKER
Thanks.
Honestly i have never build such a setup but let me think with you.
Now beween branch office 1 and 2 are 2 ACcess-List active right? Both same but vice versa.
My guess is you need an ACL to each tunnel in the office 1 config.
Like: access-list permit branch2 datacenter1
Access-list permit branch2 datacenter2